Congressman George Santos was indicted on thirteen counts of wire fraud, money laundering, theft of public funds and lying on financial disclosure forms during his short period in Congress. He was taken into custody Wednesday in New York [DETAILS].
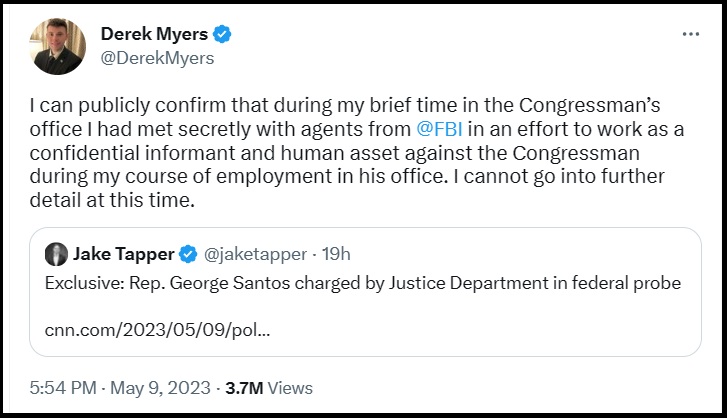
By most accounts and even his own words, Santos is a generally sketchy person, and I doubt there will be too many defenders of his character or the issues at stake. However, all of that said, this Tweet from a staffer in his office is wild:
The casual nature of this is quite alarming. It was not that long ago when the EXECUTIVE branch, using confidential human sources to investigate the LEGISLATIVE branch, would have been a matter of incredible controversy reserved for only the most serious of criminal possibilities.
An FBI informant penetrating the congressional office to relay information back to the FBI is quite remarkable. However, it appears we are in an era of justice administration where anything is just flippantly asserted inside the mechanisms of government.
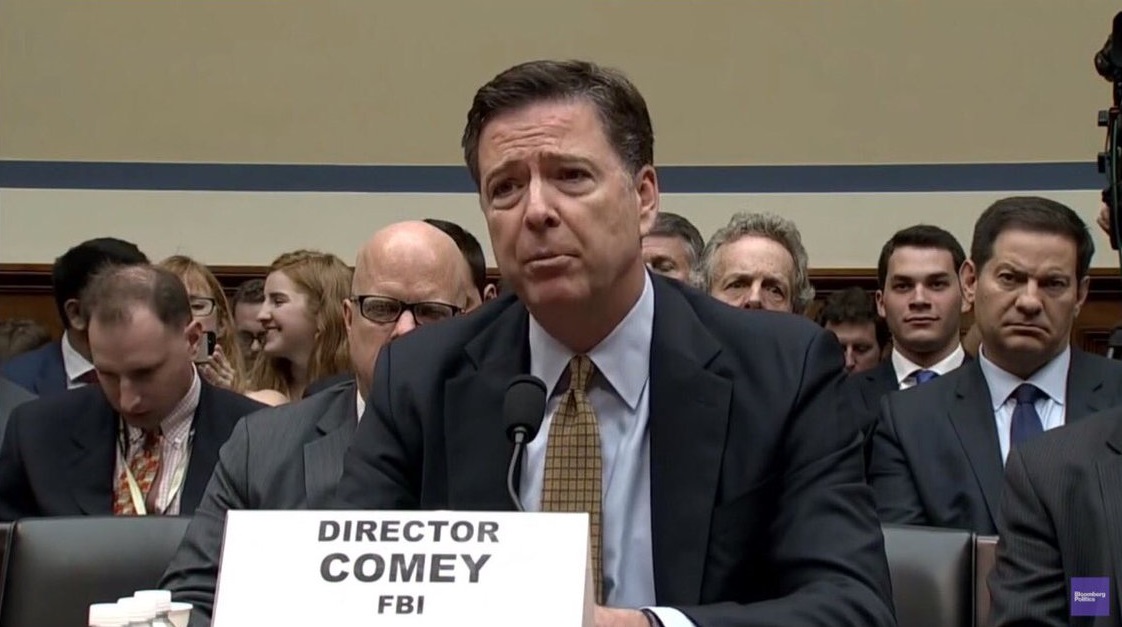
In the big picture, beyond the selfish issues of George Santos, when we consider the Fourth Branch of Government operating to protect itself against sunlight and scrutiny, this example of the FBI operating in the shadows of congress should start to make everyone uncomfortable. How can there be “checks” and balances, when the enforcement mechanisms can be deployed against any entity who threatens the system itself?
Extend this approach to legislative committee oversight, and you start to see how the system protects itself. A reminder below of what they are ultimately protecting.

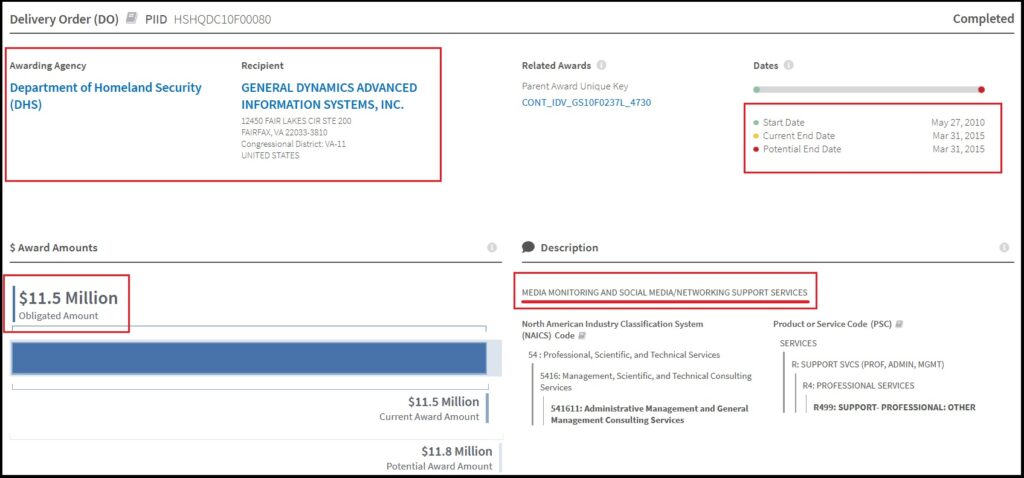



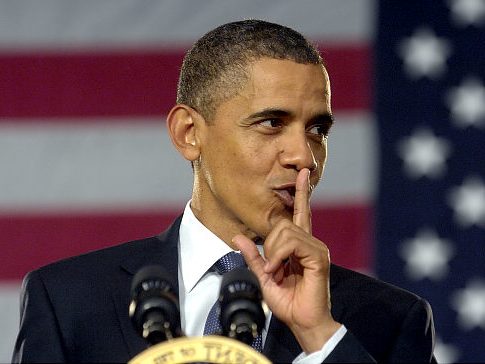 For years CTH has outlined how the Obama administration leveraged social media networks as part of a larger objective to shape public opinion, ultimately leading to the shaping of U.S. elections.
For years CTH has outlined how the Obama administration leveraged social media networks as part of a larger objective to shape public opinion, ultimately leading to the shaping of U.S. elections.