Why would any foreign actor go through all the trouble to rob a bank and yet take nothing?…
This is the metaphor for U.S. officials noticing the backdoor to our national cyber-network was found wide open, and yet not a single organization attached to the SolarWind’s Orion network points to any negative impact other than the existence itself of the originating malware. It just doesn’t add up.
Keep in mind… this “malware” has been in place since May and only recently identified.
DNI John Ratcliffe announced there was “foreign interference” in the election, and while citing Russia, China and Iran the DNI said the report on election security would be delayed. Secretary of State Mike Pompeo points to Russia as the source of the SolarWinds’ intrusion; but there is no specific evidence outlined. Today, following a briefing on the issues President Trump noted it could be Russia, but it could also be China.
There seems to be a coordinated effort to blame Russia by government officials and a host of media groups. Russia is a favored scapegoat, and given how the media falsely blamed Russia for 2016 election interference/collusion, corporate media carry a self-interest in perpetrating that narrative.
Any suggestion it was *not* Russia is then used to weaponize a Russia-apologist narrative. However, considering most of our institutions have a financial relationship with China, the self-serving hypocrisy of China-apologists carries a particularly deafening tone.
Accepting that no-one really knows, yet, who originated this intrusion, here is a Big Picture notation from the Rebel Alliance:
Due to the widespread use of SolarWinds and the length of time the SolarWinds vulnerability was possibly exploited, this attack could be the full-on equivalent of Pearl Harbor, except in a global scale.
In defending networks, very good cyber defense teams (eg, as with large financial firms and some portions of the US gov), have a good chance of success, primarily through use of extensive measures aimed at prevention and/or early detection.
But, when an attacker gets inside a network for an extended period of time, they typically focus first on becoming “rooted” (ie, they implement numerous alternate backdoors and cleverly hide malware throughout the network such that attacker access may be restored even after detection and cleanup).
Once rooted, an attacker is often extremely difficult to fully remove from the victim’s network, even if the victim completely replaces all hardware and rebuilds his entire network from scratch.
Most less capable victims, and there were potentially hundreds or thousand of direct and indirect victims in this attack, do not even have the capability to rebuild their networks and, hence, have little hope of ever completely eliminating the attacker.
Attackers are not solely interested in removing information in bulk. When large amounts of information are unexpectedly seen leaving a network, this often flags an attack in progress. So, slower and more careful movement through the network is typically seen by highly skilled attackers.
Attacker motivations are highly varied. In government networks, the attacker may wish to spy to learn about foreign agents, for example.
In a commercial network, there are many opportunities for financial gain (eg, knowledge of pending business deals). Some attackers may also wish to implement a longer term ability to physically or logically destroy the victim’s network.
Restoring a destroyed network in a large enterprise is amazingly complex. Many organizations, even those having backup data, could not do it. Even if skilled enough to rebuild, the lost time can potentially destroy the enterprise. If hundreds of firms were destroyed simultaneously, the economic impact could be crippling.
America must now confront the reality that most of its corporate network infrastructure could be entirely at the mercy of a foreign power AND that this situation is unlikely to be reversed anytime soon. This is a blow potentially as powerfully impactful as Covid-19.
I am NOT convinced this attack was perpetrated by Russia, as is being preliminarily alleged, due to the difficulty of reliable attribution. Hardly any evidence has been provided and attribution is notoriously difficult.
The evidence should be collected, the extent of the attack [in terms of the actual versus potential] use of the SolarWinds backdoor to invade Gov networks and US corporations should be determined. It must also be assessed whether the SolarWinds attack facilitated interference in the election.
Critically, it must be determined whether “nuclear worms”, capable of physical or logical network destruction, were implanted anywhere and which are now silently waiting for a signal to activate.
(Personally, if I were an IT manager, I’d be VERY worried for the safety of my Active Directory right now, since sabotage of AD is relatively easy and recovery can be extremely difficult and sometimes impossible, depending on the implementation.)
If this attack is limited to just gov networks and does not include major corporations, the election, or nuclear worms, the gov networks should be cleaned up and an appropriate response delivered to the attacker via our Cyber Defense force.
If the attack included the gov networks and election, interference, the same gov network cleanup is needed. However, the response must be more severe, and I would think should include some level of physical destruction.
If, however, the attack spread additionally to most of the Fortune 500 networks and/or includes nuclear worms, a massive gov initiative to facilitate a cleanup of corporate systems is needed.
After the initial triage, activation of plans for a kinetic response to such an attack must be considered. Eg, if the attack was attributed to China, we must respond forcefully and the response must fully respond to Chinese perceptions of US psychology. So, if China perceives the US a paper tiger, the appropriate response my be to take control of the Three Gorges Dam and open its valves.
In my view, this attack *requires* a FORCEFUL response, not necessarily limited to a cyber delivered response. The attacker must pay a high price based upon scope and severity. To do nothing projects unacceptable weakness. And the thought that US corporate infrastructure might be taken out at will, possibly through nuclear worms, possibly through more direct individualized attacks, is just unacceptable.
Regardless of the response, this attack should be taken as a wakeup call to the country. The risk of a destructive attack could be far higher than previously acknowledged.
I hope this summary is helpful to you in helping others understand the significance of this.

Look over there, no, not there, over there, no… over there….
The enemy is within… stay focused.
It’s CHINA. Brennon, Comey etc. et al.
Solar Wind let them in via China
To screw Pres Trump
Who the heck is Solar Winds? After this, they should be prosecuted for negligence, or worse, IMO.
AND that is MY thinking also spoogels…a Traitor committed a TREASONOUS act…
Too many questions. Who is this ‘Rebel Alliance’ (outside of Star Wars)? It this you, Sundance?
Why do It managers allow ‘updates’ from vendors (like Solar Wind) without independent verification of no malware or back doors? Why are essential management networks (Federal, State, Municipal, Corporate, etc.) on the Internet at all? If you’re managing a nuclear power plant, or a municipal water supply, or Lockheed Martin, why would you open your critical services network to anyone outside?
The best defense is a secure wall, and the best wall is an ‘air gap’, a virtual moat. The Dominion systems were supposed to be air-gapped, and they weren’t; they were on the Internet. Is that true of every damn organization, department, and enterprise in the world?
Call me naive. I’d like to see answers to these questions.
<i>If you’re managing a nuclear power plant, or a municipal water supply, or Lockheed Martin, why would you open your critical services network to anyone outside?</i>
Because you received your degree in computer science after 2008, you’ve been brainwashed into believing leasing a shared computer outside of your control at a unknown planetary location is completely safe and secure?
If you are connected to the internet, you are open.
worse yet is ‘cloud computing’. Oh no, use our cloud services and all your stuff is always backed up always!! Yeah and now you no longer have ownership of it. NM what the contract says.
The best defense is NOT a WALL.
Breach the “WALL” and everything within is vulnerable (see Troy regarding the horse)
The proper strategy is called “DEFENSE IN DEPTH”. It requires defenses around and throughout including physical ones (eg: physical disabling or locking of USB/WAN/LAN ports) and TRAINING (eg: the stuxnet virus was reportedly deployed by dropping infected USB thumb drives in an Iranian nuclear plant parking lot…people just can’t resist plugging in a thumb drive).
The main security issues these days come from WITHIN either maliciously OR by accident. (just ask John Podesta)
to infect the iranian atomic enrichment network, the stuxnet perpetrators merely left USB drives in the parking lot of the facility.
curious employees plugged them into computers to see what was on them and the infection was introduced.
“how did the GOP miss this…I smell a lot of collaborators.”
Sniff deeper. The GOP was IN on it. BOTH wings of the Uniparty have been using various means, to manilulate elections, FOR YEARS.
Trillions are at stake. You don’t think they are gonna leave decisions up to the great unwashed, do you?
But, its like Men in Black.
They don’t want us to KNOW about it. The are threatened, with us knowing the elections are rigged, see how hard they work to suppress the evidence?
Even in atrim county, the judge allowed the report, but with the logs redacted.
Hence, they can continue the “no evidence” narrative, because the logs ARE the evidence.
And, Mitch doesn’t want any Senator to object, because the optics exposes the Uniparty, and they don’t WANT us to know.
But, Mitch is in for a surprise, because WE KNOW, and on Jan 6th we are going to show him how many KNOW, and are mad as hell, and not taking it, any more.
Could the ‘resident’ Hacker in Solar Winds detonate a US nuclear missel at will up over the US?
Is that what nuclear worm means?
Anyone who believes Russian hacking or interference was anything beyond “nuisance level” is not thinking. Russia is practically broke. They have little spare cash with which to sufficiently bribe enough corrupt US politicians (who are now used to getting big bucks from China) to have made a material difference in the election.
No, Putin doesn’t like President Trump, but President Trump hasn’t hurt Russia anywhere near as much as he’s cut into China’s financial scams.
So why is Secretary Pompeo saying it was definitely ‘the Russians’?
The italics used here usually mean it was a block quote from a person or news site. I do not see it credited. So was SD saying that? Or was he quoting another source?
Who are the hackers?
ChInA of course.
I seeeyeaye what you did there.
although it will be tough to get rid of this hack, once the malware’s process signature, method of replication and communication ports are identified, removal can be done.
this is extremely serious, though, and shows the vulnerability of our networks and IT infrastructure.
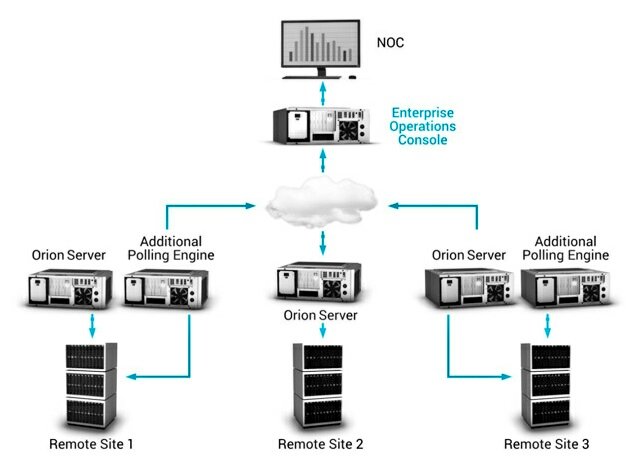
this hack succeeded by faking a ‘certificate of authority’ (CA) on an update of a network/device management utility called “Orion”. a CA is required by Windows to allow non-microsoft (3rd party) software to install without it being red-flagged by MS Defender/Windows Security.
having faked that CA, the backdoors could be installed and Windows let the hackers right in.
Five Stages of Hacking:
They did a good job, but ultimately not good enough.
My money’s on the Chinese being behind it. Whether or not this hack spread to ‘election software’, i doubt. The election sham, although coincidentally timed, is a domestic act.
When the “recon” happened that should have been the “line in the sand” so to speak that someone was hacking a .GOV system. Which begs the question: “where did the recon start?” AND work from there…That is what .GOV cybersecurity is for and they failed…WHAT CAUSED THE FAILURE? Answer those 2 questions and the answer(s) come more into focus!!!
I don’t agree graficgod, 9 months seems like perfect timing for all of it. Seems like the perfect plan to see everything as well as take over the Presidency. Stupid low level Dem’s have their hands out for a buck here and there, took care of the extra footwork.
More fallout from the Chinese theft of our technolgy? Corona invented and spread to western nations a cooincidence? It all points right at DNC, and the suspicion levied that Russia,Russia,Russia must have done it is telling as well. If the DNC, cyber corps, and China have distorted the election, is this their defense or just a distraction? I have never bought into the whole store it in a cloud mindset.. I much prefer my data is kept locally and preferably in print or backed up on a storage device. Shouldn’t all data in sensitive computers be encrypted ? The same companies that are spreading propaganda and censoring level headed people look suspicious to me. I suspect everyone is busy trying to cover their tracks. The timeline of this breach plays into the coronavirus debacle and preparation for election fraud planning. It will be interesting to see how this plays out.
I want the entire government burned to the ground. The Declaration COMMANDS us to do it.
One of the names associated with this propaganda leak was Dimitri Alparevich … Sound familiar? It should
Agree the “Russia Russia Russia” line is likely more disinformation. So why is Pompeo out front parroting this about the hack when he’s been among the most hardline against China?
Maybe he intends to use this as a ploy, to keep China thinking they pulled off the disguised hack using a Russian signature?
Would love to see our side send through our most deadly malware coding into China’s mainframe…take down their satellites, mil comms and financial centers. You want war? ZAP!
The “threat actor” is named UNC2452 aka Dark Halo. The competent civilian IT security firms that have analyzed it say it is a “state sponsored actor of unknown origin,” so the swamp can get away at pointing fingers to whoever they want.
As to Russia, it could well be them as far as the cyber attack. I recall back during the Obama administration, somewhere I do not remember exactly where, Putin discussed how the wars of the future would be fought in cyberspace, not with soldiers and planes and ships and tanks. I also remember back then arguing that we were creating an enemy in Russia and unwisely driving them into alliance with China. I thought Trump had a chance to reverse that when he took office but his decision was to come down harder on Russia. I have blamed the liberal and neocon influences in our intel. Fate was complete and Russia did enter into alliance with China. Who could blame them as we placed even harsher sanctions on them? I am not defending them, just pointing out action and potential reactions. So it may well have been Russia and China collectively together but also others such as Iran and Venezuela, all countries Trump has put the harshest financial attacks on during his administration. From my perspective, this year has bought us covid which could possibly be a bio weapon attack. Next we had antifa and Black Lives Matter insurrections. Both are communist movements and both had to have significant financial support and efforts behind them. Next was the election which obviously was fraudulent. Now we learn as we were under attack from the virus and insurrections in our cities, we were as well under cyberattack. Coincidences? No. I think ‘they’ went to war against us and no thanks to our pathetic intel agencies, we have yet to realize it.
I agree on the easily credible collusion between China and Russia. Consider what they have accomplished since Trump was elected:
1. It is KNOWN that oligarchs close to Putin were the source of the dossiers used in RussiaGate. That whole thing was, as I said at the time, a “poison pill” operation that the Russians knew our deep state / swamp and their owned major media would enthusiastically run with and which would cause major political division and further delusion with government in the US while damaging Trump.
2. I’m definitely not one who comes to conclusions easily, so rather than write a book here about all of the supporting evidence, I believe that the SARS-CoV-2 release was intentional and timed for Trump’s reelection year, but would not have been done with high level Chicom government approval. Instead, it was either a lone wolf act exactly like the post-9/11 anthrax attacks here or a Chicom intel agency act done secretly. They also knew that the US medical firm which funded viral gain-of-function research at the Wuhan lab would provide cover and they did: it has recently been exposed that that firm was secretly behind all of the “But, but, it’s a natural virus!” garbage in the corporate media at the beginning of the pandemic. The perps also knew the CCP would cover this up whether they discovered the actual ID of the perps or not.
3. Finally, there is the blatant compromise of the 2020 election which the attackers knew, as in step #1, the deep state / swamp would not investigate because they would support the results. Thus, the in your face, blatant attack and fraud.
Mission accomplished: the ejection of Trump from office, the destruction of any trust whatsoever in government in at least 50% of the US citizenry and the serious wounding of the US economy costing more debt-based money created from thin air (and counting) than created during the entire (phony) recovery from the 2008 global financial crisis, that debt-based money required just to paper over the problem, not to fix the economy on a sustainable basis. As an added “benefit,” small businesses are destroyed and the primary owners of “your” government, huge multinational corporations, are strengthened.
It is impossible toknow who did this without seeing the code and/or without information from somebody inside the group that did it. However… hacks leave cultural tracks in things like the order of operations and the choices made in naming and hiding. In that context this does not appear to be russian, it looks most like Microsoft’s own work – i.e. as if the key players had previously worked for Microsoft and internalized Microsoft’s “standards” for clean and repeatable development.
ask Seth Rich that one.
Maybe China paid Russia tons of money to do the cyber attack with China’s IT guidance.
Seth Rich. Sending a message?
China wants us to have a war with Russia .. FIRST, so they can come in and clean up and be in control.
why would they take out large corporations they already own or control? It is the individual or privately held companies they want. They are destroying small businesses at an exasperating rate. The worms are meant for them. They know they are more likely to have their departmental information on line. This isn’t a game to them, this is a battle for world domination.
Both Solarwinds and Dominion seem to have crappy c code prone to buffer overflows
https://borncity.com/win/2020/12/17/sunburst-malware-analytic-tool-solarflare-a-kill-switch-and-einsteins-fail/
https://cve.mitre.org/cgi-bin/cvekey.cgi?keyword=SolarWinds
No detection of overflows in arithmetic performed on vote counters.
A 32-bit signed integer requires over 2 billion votes to overflow a counter. While statistically unlikely6, if an overflow were to occur, election results could be affected in unpredictable ways.
https://verifiedvoting.org/wp-content/uploads/2020/08/democracy-suite.pdf
https://s3.eurecom.fr/docs/issta08_evote.pdf
https://www.defcon.org/images/defcon-25/DEF%20CON%2025%20voting%20village%20report.pdf
Dominion Software uses INSECURE routines known to cause buffer overflows. Leaving this in the final deliverable is unprofessional BS
Elections run by proprietary insecure code with a history of crashes
Dominion Software uses the UNSECURED STRCPY () function within their source code. Just like the California Report says an insider or skilled villain could hack it.
https://votingsystems.cdn.sos.ca.gov/vendors/dominion/ds52-sc.pdf
https://doc.castsoftware.com/display/SBX/Never+use+strcpy%28%29+function
https://www.mccabe.com/pdf/Appnote-ControlFlowSecurityAnalysis-BannedFunctions.pdf
“ ICX Prime DRE with VVPAT/Report Printer
During test performance, using manual session activation, it was noticed that units were printing random Unicode characters in between valid report lines on the VVPAT unit. Based on Dominion’s investigation, the root cause of the issue was determined to be the buffer overflow caused by the memory limitations of the printer input buffer, and a short timeout (200ms) on the host side of the USB data transmission.
The solution was to increase the timeout to five (5) seconds on the host side, so that the function that transmits data to the printer waits long enough to allow the printer to sufficiently empty its buffer so that it has room to receive the next data packet, regardless of the printer speed setting.”
https://www.eac.gov/sites/default/files/voting_system/files/Dominion_Voting_Systems_D-Suite_5.5_Test_Report_Rev_A.pdf
Our elections shouldn’t be using “outside vendor unverified proprietary source code “ Our elections should not run by proprietary algorithms from anonymous programmers
Does anyone in America Run Penetration testing on our voting software or is this type of analysis all done in China and Russia?
This is PATHETIC
“ Security experts say the small number of companies that dominate the nation’s election technology market, including ES&S, have failed to acknowledge and remedy vulnerabilities that lie in systems used to hold elections across the country. Once left to obscurity, the entire ecosystem has been called into question since the Russian government was found to have interfered with the 2016 ”
“ “That prompted us to ask if DHS could do penetration testing of an election system,” Wlaschin told CyberScoop. “[DHS officials] said they’ve never done it before, but were willing to try.”
“ Christopher Krebs, director of DHS’s Cybersecurity and Infrastructure Security Agency, told CyberScoop that tests like this are a force-multiplier for the outreach the agency is conducting ahead of the 2020 election.
“We’ve got to reach out and in part we can actually work with the vendors in that outreach,” Krebs told CyberScoop. “In a lot of cases, the vendors work with the local jurisdictions more so than the 50 Secretaries of State or the election directors do. So we’re taking a multi-pronged approach to actually getting to that real, true ‘last mile’ engagement.”
“ ES&S seems to have taken a page from Mark Zuckerberg’s playbook. The company told CyberScoop that it’s working with “a set of Congressional staffers” on legislation that would shape an industry-wide coordinated vulnerability disclosure program in lieu of setting up a program that is only for their tech. The company refrained from naming the staffers since talks are at an introductory phase.
The company has been examining such a program for the past few months, collaborating with its competition on ways the industry could create bug bounty and coordinated vulnerability-disclosure programs. Company representatives from the three big election tech companies —ES&S, Dominion and Hart Intercivic — have attended numerous meetings or events over the past few months, including one set by the Information Technology Information Analysis and Sharing Center (IT-ISAC) where executives spoke with company officials who have set up bounty programs in the automotive, aviation and healthcare sectors.
While the company doesn’t need legislation to set up such a program, ES&S told CyberScoop it would prefer if a law forced the entire industry to follow a similar set of program guidelines.
“We want coordinated vulnerability disclosure and bug bounty programs to apply equally to all the vendors in in the industry,” Wlaschin told CyberScoop. “We don’t want ES&S to be out there alone.”
Dominion and Hart InterCivic told CyberScoop they are interested in figuring out a baseline that can work for the entire industry.”
Ref:
https://www.cyberscoop.com/election-security-es-s-dhs-pen-testing-idaho-national-labs-procircular/
Moreover, per my other posts they use known banned routines such as strcpy know to be prone to buffer overflows
Bottom line: nobody but our adversaries are consistently and rigorously doing fuzz and penetrating testing on our voting systems. This is a FAILURE OF TECHNICAL LEADERSHIP!!!
https://www.mccabe.com/pdf/McCabeIQ-FuzzTesting.pdf
It could be both. Duh.