In the lead-up to the critical 2018 mid-term elections, President Trump’s political opposition needed a control mechanism in order to remove him from office and support the impeachment path. The administrative state -writ large- produced an overwhelming narrative leading to the issuance of a Executive Declaration of A National Emergency to Avoid Foreign Interference in Our Elections.
At the time the narrative was framed (mid-2018), the argument was: if President Trump did not declare the emergency, and grant the federal intelligence community the right to enter state election databases and “monitor” the activity therein, that refusal itself would be proof Donald Trump was a Russian asset. Remember, the Mueller investigation was at its apex and the office of the president was surrounded by administration officials like Mike Pence (VP), Jeff Sessions, Rod Rosenstein (DOJ), Alexander Vindman (NSC), Dana Boente (FBI), Dan Coats (DNI), Michael Attkinson (ICIG), et al; all of them carrying ulterior motives.
President Trump signed the emergency declaration and granted the Intelligence Branch of Government full access to the state-level election systems.

In short, President Trump was forced by his Machiavellian captors to seal his own fate. Yes, this is how the DC apparatus works. The Intelligence Branch of Government works with their political agents within the legislative branch and simultaneously coordinate with their media operatives to surround the target with fire until the action they need is executed. In the fall of 2018, the unrelenting pressure worked exactly as designed. [Federal Register]
It was not coincidental that most of the new 2018 Democrat candidates for office came from former and/or current CIA and intelligence agencies. A few people wondered why so many ‘new’ DNC approved candidates were from the intelligence agencies of the government. Some even coined the phrase “CIA Democrats“, but for the most part it was ignored. The 2018 federal election outcome was delivered exactly as planned. Democrats took control of the House of Representatives and paved the way for Mueller to deliver what they needed for articles of impeachment.
Fast forward to 2020, and the same Federal Declaration of a National Election Emergency was used to support the COVID mail-in ballot narrative, while the same intelligence branch operatives coordinated with state-level political activists to manipulate the outcome.

 The intelligence apparatus, including the DOJ/FBI and aligned agencies, in addition to the DOJ officials within the Mueller probe, previously exploited their surveillance access to records and communication of Donald Trump and his administration. Those intelligence operatives then spun and leaked parts of those records in order to build a fictitious Trump-Russia narrative and simultaneously distract from the prior unlawful surveillance.
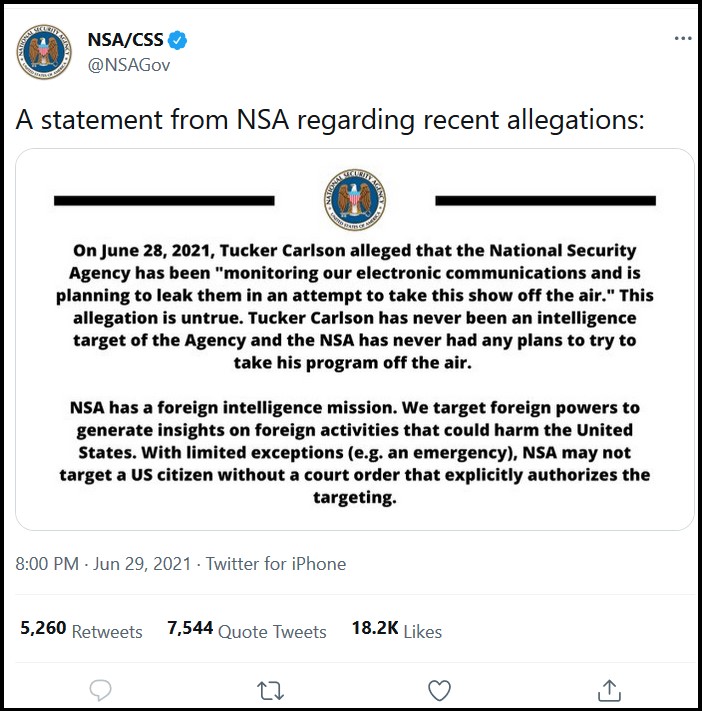
The intelligence apparatus, including the DOJ/FBI and aligned agencies, in addition to the DOJ officials within the Mueller probe, previously exploited their surveillance access to records and communication of Donald Trump and his administration. Those intelligence operatives then spun and leaked parts of those records in order to build a fictitious Trump-Russia narrative and simultaneously distract from the prior unlawful surveillance. In addition to a global scraping of metadata, the NSA also collects the domestic private information of all Americans. This was the essential background story that NSA Contractor Edward Snowden broke several years ago. We now know this to be an accepted fact.
In addition to a global scraping of metadata, the NSA also collects the domestic private information of all Americans. This was the essential background story that NSA Contractor Edward Snowden broke several years ago. We now know this to be an accepted fact. First, Andrew Weissmann comes from the DOJ-National Security Division (DOJ-NSD). More specifically, in that division Andrew Weissmann was in charge of the section that used FARA (Foreign Agent Registration Act), or FARA-951 as a weapon against their political enemies.
First, Andrew Weissmann comes from the DOJ-National Security Division (DOJ-NSD). More specifically, in that division Andrew Weissmann was in charge of the section that used FARA (Foreign Agent Registration Act), or FARA-951 as a weapon against their political enemies. After many years of granular research about the intelligence apparatus inside our government, in the summer of 2020 I visited Washington DC to ask specific questions.
After many years of granular research about the intelligence apparatus inside our government, in the summer of 2020 I visited Washington DC to ask specific questions.