Go figure. If you read between the lines of the Washington Post’s current description of the “classified” documents, as noted by anonymous federal officials connected to the investigation, the ‘classified‘ documents in context were personal correspondence between President Trump and Chairman Kim Jong Un about the need to chill out on the nuclear stuff.
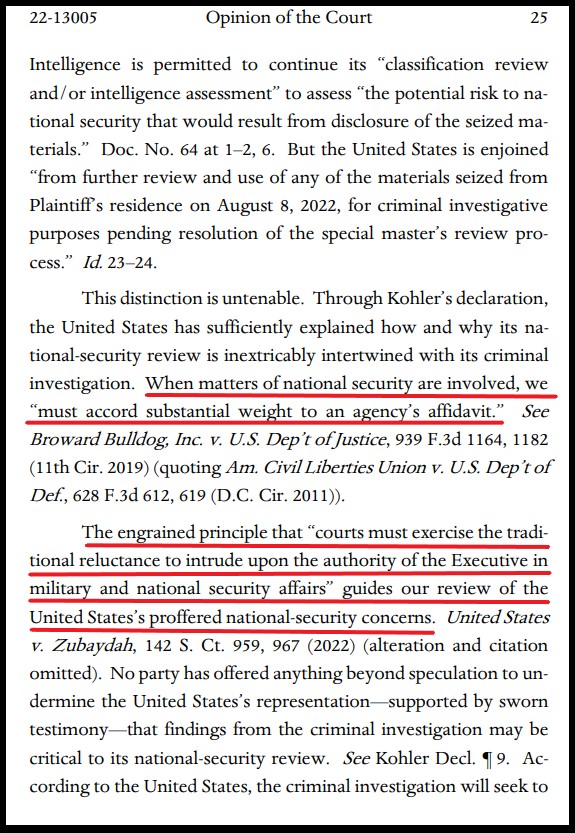
 President Trump considered these types of papers personal mementos, while the administrative state -seeking to weaponize the DOJ/FBI for maximum political damage and narrative engineering- considered them top secret national security documents.
President Trump considered these types of papers personal mementos, while the administrative state -seeking to weaponize the DOJ/FBI for maximum political damage and narrative engineering- considered them top secret national security documents.
The election is over, so the narrative is no longer needed. Narrative dropped…
(Via WaPo) – Federal agents and prosecutors have come to believe former president Donald Trump’s motive for allegedly taking and keeping classified documents was largely his ego and a desire to hold on to the materials as trophies or mementos, according to people familiar with the matter.
As part of the investigation, federal authorities reviewed the classified documents that were recovered from Trump’s Mar-a-Lago home and private club, looking to see if the types of information contained in them pointed to any kind of pattern or similarities, according to these people, who spoke on the condition of anonymity to discuss an ongoing investigation.
That review has not found any apparent business advantage to the types of classified information in Trump’s possession, these people said. FBI interviews with witnesses so far, they said, also do not point to any nefarious effort by Trump to leverage, sell or use the government secrets. Instead, the former president seemed motivated by a more basic desire not to give up what he believed was his property, these people said.

 At this point in history, anyone who is claiming the U.S. Government is not directly coordinating with social media platforms to shape opinion and cull information adverse to their interests, is being intellectually dishonest. There is simply too much evidence of the intelligence apparatus, specifically the Dept of Homeland Security, being enmeshed with the platforms of Twitter, Facebook, Instagram, Google and Microsoft.
At this point in history, anyone who is claiming the U.S. Government is not directly coordinating with social media platforms to shape opinion and cull information adverse to their interests, is being intellectually dishonest. There is simply too much evidence of the intelligence apparatus, specifically the Dept of Homeland Security, being enmeshed with the platforms of Twitter, Facebook, Instagram, Google and Microsoft.