Put this in the tab labeled ‘conclusive proof of prior suspicions.’
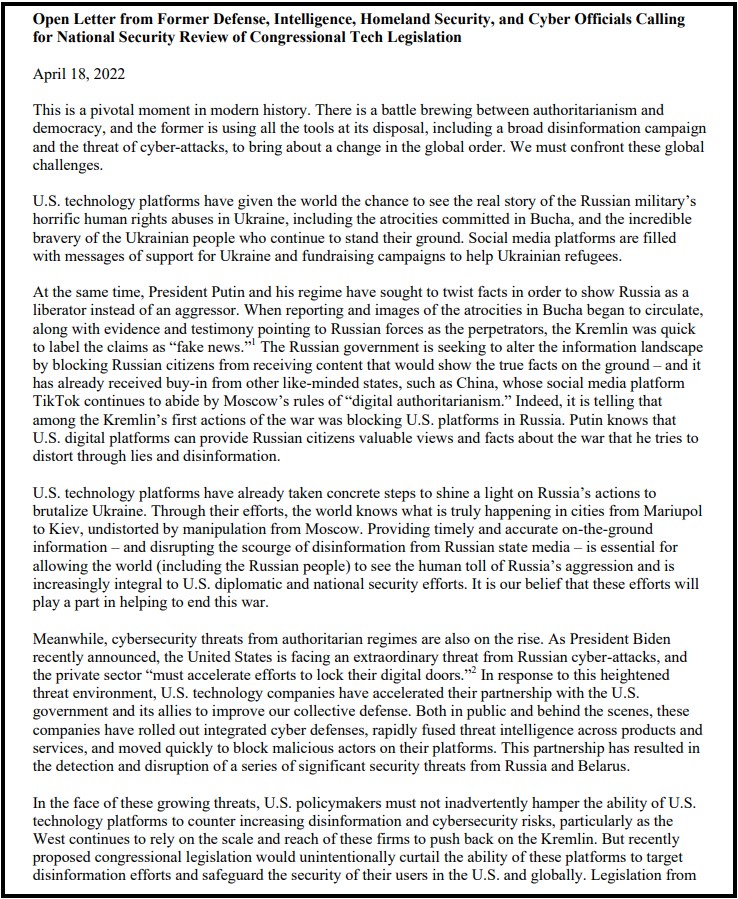
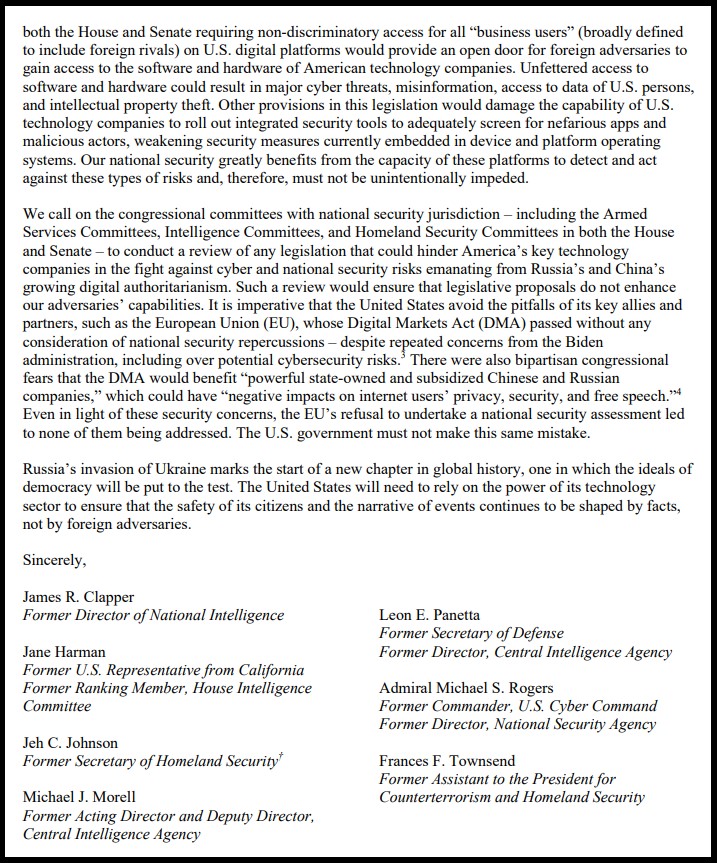
 Former Obama era intelligence officials, those who helped construct, organize and assemble the public-private partnership between intelligence data networks and supported social media companies, have written a letter to congress warning that any effort to break up Big Tech (Twitter, Facebook, Instagram, Google, Microsoft, etc.) would be catastrophic for the national security system they have created.
Former Obama era intelligence officials, those who helped construct, organize and assemble the public-private partnership between intelligence data networks and supported social media companies, have written a letter to congress warning that any effort to break up Big Tech (Twitter, Facebook, Instagram, Google, Microsoft, etc.) would be catastrophic for the national security system they have created.
Citing the information control mechanisms they assembled, vis-a-vis the ability of social media networks to control and approve what is available for the public to read and review, the intelligence officials declare that any effort to break up the private side of the intel/tech partnership will only result in less ability of the intelligence apparatus to control public opinion.
They willfully admit that open and uncensored information is adverse to the interests of the intelligence state and therefore too dangerous to permit. They specifically argue, if the modern system created by the partnership between the U.S. government and Big Tech is not retained, the national security of the United States is compromised. Let that sink in for a moment.
One of their reference citations revolves around Ukraine and the Russia narrative:
“U.S. technology platforms have given the world the chance to see the real story of the Russian military’s horrific human rights abuses in Ukraine, including the atrocities committed in Bucha, and the incredible bravery of the Ukrainian people who continue to stand their ground. Social media platforms are filled with messages of support for Ukraine and fundraising campaigns to help Ukrainian refugees.” (Paragraph 2, Letter)
 Keep in mind the “Bucha” narrative is widely disputed by people who have reviewed the western government/media evidence.
Keep in mind the “Bucha” narrative is widely disputed by people who have reviewed the western government/media evidence.
There is equal evidence the Bucha narrative was a western intelligence operation, created to give a false impression and generate public support for advanced military operations in Ukraine.
Seeing this public relations effort using the Bucha story as evidence to support their goal of keeping Big Tech isolated from legislative review, only lends more credence to suspicions the Bucha events were a U.S. led intelligence operation (false flag).
Glenn Greenwald has a good take on the granular details behind their letter:
[…] This is where these former intelligence and national security officials come in. While these former CIA, Homeland Security and Pentagon operatives have little sway in the Senate Judiciary and House Antitrust Committees, they command great loyalty from Congressional national security committees. Those committees, created to exert oversight of the U.S. intelligence and military agencies, are notoriously captive to the U.S. National Security State.
The ostensible purpose of this new letter is to insist that Big Tech monopoly power is vital to U.S. national security — because it is necessary for them to censor “disinformation” from the internet, especially now with the grave Russian threat reflected by the war in Ukraine — and they thus demand that the anti-Big-Tech bills first be reviewed not only by the Judiciary and Antitrust Committees, but also the national security committees where they wield power and influence”… (read more)
Of course, the Fourth Branch of Government would want to get the Senate Select Committee on Intelligence involved. The SSCI created all of the mechanisms to facilitate the existence of the Fourth Branch of Government. However, I would take the issue deeper…. and ask readers to see what really worries the intelligence apparatus about the potential breakup of Big Tech.
These are the intelligence people who constructed the model for Jack’s Magic Coffee Shop.
This public-private partnership between the cyber division of the intelligence apparatus and Big Tech social media is where the free coffee comes from.
Twitter, Facebook, Instagram, YouTube and even Google itself, are financially and operationally dependent on the scale of the data processing system that is run by the U.S. government. The capacity of each of the big social media companies to exist, operate and be financially viable, is dependent on the backbone of interconnected data networking, and massive data processing.
The scale of simultaneous user data-processing is not financially viable without the U.S government subsidizing it. That’s the free coffee that cannot be duplicated in the private sector by any competing social media company. That’s the cost and scale system behind the partnership that permits Big Tech to operate. Ultimately, this is what the intelligence apparatus needs to keep hidden from the American (and global) public.
The biggest of the Big DATA processing is done through a public-private collaboration between Big Tech and Big Government/Intel.
Any private sector entity who attempts to create, or duplicate the scale of social media runs into this cost issue. It is just too expensive to operate a competing coffee shop without the free coffee. That’s why the coffee providers are lined up against Elon Musk’s attempt to buy Twitter.
The ramifications of the public discovering Facebook and Twitter social media are only possible with subsidy from government tech architecture are massive. Essentially, the U.S. government is in control of our social media networking. That’s the bigger story behind this letter.
These officials are trying to preserve the surveillance system they created.
The public-private partnership is a system for surveillance of the American people through technology.
BACKGROUND – The volume of metadata captured by the NSA has always been a problem because of the filters needed to make the targeting useful. There is a lot of noise in collecting all data that makes the parts you really want to identify more difficult to capture. This admission, along with the admission of collaboration from 2021, puts a social media filtration system in the metadata that circumvents any privacy protections for individuals.
Previously, the Intelligence Branch worked around the constitutional and unlawful search issue by using resources that were not in the United States. A domestic U.S. agency, working on behalf of the U.S. government, cannot listen on your calls without a warrant. However, if the U.S. agency sub-contracts to say a Canadian group, or foreign ally, the privacy invasion is no longer legally restricted by U.S. law.
What was announced in June 2021 was an admission of a relationship with Big Tech along with open intent to define their domestic political opposition as extremists.
July 26, 2021, (Reuters) – A counterterrorism organization formed by some of the biggest U.S. tech companies including Facebook (FB.O) and Microsoft (MSFT.O) is significantly expanding the types of extremist content shared between firms in a key database, aiming to crack down on material from white supremacists and far-right militias, the group told Reuters.
Until now, the Global Internet Forum to Counter Terrorism’s (GIFCT) database has focused on videos and images from terrorist groups on a United Nations list and so has largely consisted of content from Islamist extremist organizations such as Islamic State, al Qaeda and the Taliban.
Over the next few months, the group will add attacker manifestos – often shared by sympathizers after white supremacist violence – and other publications and links flagged by U.N. initiative Tech Against Terrorism. It will use lists from intelligence-sharing group Five Eyes, adding URLs and PDFs from more groups, including the Proud Boys, the Three Percenters and neo-Nazis.
The firms, which include Twitter (TWTR.N) and Alphabet Inc’s (GOOGL.O) YouTube, share “hashes,” unique numerical representations of original pieces of content that have been removed from their services. Other platforms use these to identify the same content on their own sites in order to review or remove it. (read more)
The influence of the Intelligence Branch now reaches into our lives, our personal lives through their efforts in social media.
In the decades before 9/11/01 the intelligence apparatus intersected with government, influenced government, and undoubtedly controlled many institutions with it. Back then, the legislative oversight function was weak and growing weaker, but it still existed and could have been used to keep the IC in check. However, after the events of 9/11/01, the short-sighted legislative reactions opened the door to allow the surveillance state to weaponize.
After the Patriot Act was triggered, not coincidentally only six weeks after 9/11, a slow and dangerous fuse was lit that ends with the intelligence apparatus being granted a massive amount of power. The problem with assembled power is always what happens when a Machiavellian network takes control over that power and begins the process to weaponize the tools for their own malicious benefit. That is exactly what the installation of Barack Obama was all about.
The Obama era intelligence team took pre-assembled intelligence weapons we should never have allowed to be created and turned those weapons into tools for radical, political and fundamental change. The target was the essential fabric of our nation. Ultimately, this corrupt political process gave power to create the Fourth Branch of Government, the Intelligence Branch. From that perspective, the fundamental change was successful.
…It’s all Connected Folks, SEE HERE


[…] “The vision was first outlined in the Intelligence Community Information Technology Enterprise plan championed by Director of National Intelligence James Clapper and IC Chief Information Officer Al Tarasiuk almost three years ago.” … “It is difficult to underestimate the cloud contract’s importance. In a recent public appearance, CIA Chief Information Officer Douglas Wolfe called it “one of the most important technology procurements in recent history,” with ramifications far outside the realm of technology.” (READ MORE)
One job…. “take the preexisting system and retool it so the weapons of government only targeted one side of the political continuum.”
References:
Jack’s Magic Coffee Shop – HERE
The Fourth Branch of Government – HERE
Well then…everyone…start doing some dot connecting.
One part of the connecting necessarily requires visiting and reviewing content on these and more obscure web sites that promulgate the IC disinformation. For example, Linkedin since MS took over has slowly morphed into a Facebook like operation. I caught a thread the other day posted by someone I knew who worked for a DC area corporation with a large cybersecurity footprint who has now advanced to a CISO position. The thread referenced a lengthy article at Atlantic magazine decrying the social fragmentation large scale social media has fomented. The punchline for the article was that gov’t needs to intervene and regulate Big Tech in order to promote societal community/unity. This particular thread received an uncommonly large number of comments all of which registered agreement. THE POSTER APPROVINGLY INTRODUCED THE REFERENCE AS AN ISSUE WITH NATIONAL SECURITY IMPLICATIONS. So now I have insight and intelligence of my own on where people line up in this bigger power play.
It’s not hard to figure out where the big data facilities are located (e.g., press statements, power consumption analysis). Connect that dot to the recent spike (it’s been there all along for over a decade now) in critical infrastructure threat warnings from the MSM and gov’t. Much like the perp trees that one used to see in popular movies piecing together who works for whom (i.e., the hierarchy) – the same can be done for the actors in this game down a few levels in the tree by conducting what used to be called “opposition research”.
An effective response to the power play is going to require some in-house intelligence work itself. Sundance et al are dong some of the heavy lifting. A lot more is needed – at scale.
Good comment Phillip.
The Intel Letter is focused on “foriegn” propaganda but we all know the reality of domestic censorship, the real threat to our republic.
Let me suggest this solution to foreign “misinformation”: FBI do your job.
If it really is foreign propaganda they are after 1) find the spies, find the foreign agents who are actually doing the dirty work for China, Russia and others enemies who are these so called foreign influencers and charge them with a crime or run them out of the country, AND, 2) block or sabotage FOREIGN ENEMY sources of misinformation from entering the country, and 3) LEAVE AMERICANS ALONE.
Of course “2)” above would require us to choose sides and actually stipulate who are enemies are. The Lib’s have been cosy with communism for decades now and have successfully blurred the lines between friend and foe. Now, if what the intel letter says is true, and, as the Reverend Jeremiah Wright has said, “The chickens have come home to roost”.
If the intel community really believes what they are saying, follow the money. FBI, find out who is taking money from foreign governments, including our own elected officials. Stop the flow of foreign money coming in this country in the form of “donations”, expose the shell organizations, expose the corruption, expel or arrest those who are actual foreign agents. If what your letter says is true, you can do that.
But do not censor Americans. Leave us alone.
Get Kamala on it, she can get to the root cause.
You mention James clapper in the same sentence as intelligent official🙄😂🤣😂🤣🤣🤪😂🤪
I think back to John Ashcroft and Bush the lesser implementing the pre-planned patriot act like good little serfs of the deep state.
With that, they gave us the TSA (control of transportation hubs), and that huge data center in the desert among other “gifts” that keep on giving.
This was all pre-planned. If you think that is beyond the pale, then read Malachi Martin’s Windswept House to read exactly how these minions of satan go about their ways.
I know right. Trying to pass the buck to Obama when really they just passed him the torch.
Admiral Mike Rogers.
The “Hero” who warned Trump????
I see names, but no signatures.
Wouldn’t you need approval from someone that had ‘read’ the letter before putting their name on it? 🙄
Normally yes. In these days and times, no so much.
Let’s see if Rogers makes a public statement. If not then the curious cat should appear.
I know I was surprised to see Michael Rogers name…..?
Their fear mongering is so obviously obtuse. It’s laughable really. They still want us to believe their narrative, which is 180 degrees from the truth.
“Protect the public from disinformation”? The reality is just the opposite. THEY want/must control the narrative by censoring truth while feeding the public THEIR own disinformation! The emperors have no clothes…..
That horse left the barn years ago….
The National Imperative is wrestling the power from the intel agency cabal and giving it back to The People. The Patriot Act released the Kraken on the citizens of this country. How do we cram the genie back in the bottle now?
That’s a good question and I don’t have an answer at the moment. How many times have we heard in the past few years:
“Sorry, that information is classified…”
or
“Sorry, we can’t give out information on an open investigation…”
Clear and accurate insight!
You have to give up counting the propaganda words after a couple of paragraphs…the “incredible bravery,” “scourge of information,” calling out the boogeyman Putin by name, and on and on. They’re getting completely obvious about it.
Those at the upper echelons of the world’s dominant machinery of lies and disinformation have put themselves at the pinnacles of organized crime. The rule of law has been sacrificed to those who used 9/11 and then the manufactured COVID crisis and now the Russia-Ukraine operation as vehicles for enlivening devices for further our enslavement.
Bill Binney related the original message – in my opinion – that was the preamble to Sundance’s deep reveal. The “Magic Coffee” concept makes sense, and is the leading reasonable explanation for a lot of the grotesque behavior of the intel community.
We have gone from the age where “do not believe anything you read on the internet,” to believe everything that big tech posts on the internet. Good Grief!
“created to exert oversight” -GG
SSCI was created in the 1970s. The “family jewels” were declassified in 2007. These were a set of reports that detailed illegal activities by the CIA between the late 1950s to 1973.
-The Family Jewels
“The Central Intelligence Agency violated its charter for 25 years until revelations of illegal wiretapping, domestic surveillance, assassination plots, and human experimentation led to official investigations and reforms in the 1970s.”
gwu.edu/~nsarchiv/NSAEBB/NSAEBB222/index.htm
The CIA wised up during the 1970s and started seeding their “own” candidates for political office in the United States on both sides. It was very easy of them to funnel money backing select candidates through their foreign and corporate global allies.
That’s how we’ve ended up where we are today. A Congress independent of CIA influence would look radically different.
Folks,
David Knight’s been talking about this for YEARS! For years, DK has discussed the role that In-Q-Tel and other CIA front, venture capital companies played in establishing the Big Tech companies. They gave seed money to all those wanting to start tech companies, then let them fight it out; once the survivors were established, the Deep State had what it wanted: a “private” arm to carry out its bidding.
The Deep State also wanted a feedback mechanism, so as to verify the effects of their propaganda disseminated via the MSM. You see, while there was a time that there were only the Big Three TV networks, there was no way to see how their propaganda was being received by the masses. David Knight has also discussed the role of a DARPA psychologist named JCR Licklider. It was JCR Licklider who came up with the idea of the Internet back in the 1960s; for those who know the history behind the Net, you’ll know that it was once called the Arpanet, for DARPA’s predecessor-hmmm! It wasn’t until the 1990s that technology had improved to the point where the Worldwide Web was possible. But yeah, the gov’t was always behind the Net. They wanted the Net to observe the effects of DS propaganda, so they could adjust it in real time.
Oh, do you know that Facebook’s predecessor was a DARPA program called LifeLog? It was! Is it any coincidence that Facebook began the day that LifeLog was ended? If you think so, there’s a bridge in Brooklyn I’d just LOVE to talk to you about! As FDR once said, nothing in politics happens by accident. If something happens in politics, you can bet it was PLANNED that way (emphasis mine)…
Lots of us have known this. But consider the fact that to varying degrees, journalism is a risk balance. Sundance must always remain careful not to risk going too deep into the woods on certain issues. But while I’m sure he too is familiar with these facets of reality, one cannot simply blast out seemingly non-linear bits of information and expect people to just accept it and to get it fully.
ALSO, the fact that this is being reported on now doesn’t mean it hasn’t been reported on or mentioned previously. There are a lot of people waking up and need this information in a fresh delivery.
I know this is the popular narrative,but there are a few things that are wrong.The most important is the idea of ‘the world wide web’,Avis rent-a car had a world wide web in the 1970’s.Anyone in the company could send and receive company information,could obtain information about individual customers and their accounts,and use a local terminal to write rental agreements and even communicate with other Avis locations around the globe.Supposedly,one guy invented it,and it became his life’s work for at least a decade.All of the elements of the current internet were part of this system,and it worked pretty well even then.The internet as we now know it was no surprise or particular mystery to their employees,they’d had it for years.
Yeah, but the Net as we now know it wasn’t possible until the 1990s; only then was there enough bandwidth and technology to make it possible. I’m well aware of the ARPAnet. Do you think that, for one second, TPTB wouldn’t have brought the Net to us sooner if they could? Again, TPTB needed a real time feedback mechanism, so as to adjust their propaganda in real time.
Big Brother
The harder they push the more desperation you can smell, and they’re all really beginning to stink. ( I know, they’ve always stunk but you get my meaning).
TPTB are concerned about white supremacist violence, but not about BLM / AntiFa. Color me surprised. Very surprised.
I really wish people would stop writing “TPTB” for so many reasons. They don’t “be.” That they are powers is a violation of the spirit of this constitutional republic. And they are not concerned about white supremacist violence in the way you think. They are concerned that it’s HARD to find in nature and so it’s difficult to actually put it on display. They are also concerned that any existing or historical white supremacists are all DEMOCRATS.
And I won’t color you anything… that’d be racist.
And all that insistence in itself, by those entities is enough for me to support bringing Big Tech to heel…..I DO NOT TRUST a one of our Intelligence organizations now. NOT ONE….
At the same time that they trample on our rights they say they are necessary to protect our rights.
Time for folks like Judicial Watch to ramp up against this. This needs to go as far as it needs to to end this type of constitutional violation.
I work as a data processing consultant, and I have always cautioned my clients to stay away from “the Cloud,” no matter how financially appealing they make it to be.
You don’t know where in the world your “crown jewels” are. You don’t know who else has access to them. They could sell it to your competitor and you would never know. The companies could “de-platform” you just because they’ve decided they don’t like you anymore. (As happened to CTH first-hand.) If something sounds too good to be true, it is.
I feel the same way about “social media,” which by the way I have never used and never will. There is a time and a place where the smartest thing to do is to shut up. When something is offered to you free of charge, it’s not because they want to sell you advertising: it is because you are the product.
Have you bothered to consider why Facebook wants you to “tag” people in photographs? Because you are feeding a facial-recognition database. This is also why your phone identifies faces in every picture that you take, and during the night analyzes those photos and sends them along with GPS coordinates … somewhere. Whether you want it to or not, and you can’t stop it. Same databases. Cameras can watch a crowd in Times Square and in real time identify everyone in that crowd. You drive down the highway past cameras that are doing the same. And you’re the ones feeding it information.
Surveillance, like any other form of control, “is an intoxicating beverage.” Government agencies do it because they can – and because they and their contractors can make vast amounts of money that the rest of government isn’t watching closely “because national security.™” (And, “Top Secret” is the perfect hiding place.) They want to record everywhere you go and everything you say, not because they have a 4th Amendment need or legal right to, but because they can. And because you are not aware of what they are doing.
“Loose Lips Sink Ships!”
First, I am once again stunned at Sundance’s ability to see the larger picture that others cannot even imagine. I am also in awe of, and grateful for his determination to keep the Treehouse free of outside interference. I didn’t totally understand the issues when CTH was kicked off of the last platform but I now understand his objectives. Knowing the cost, I will be more disciplined about donating to keep freedom in the Treehouse.
This issue is actually what is causing the National Security Crisis through the US pursuing a policy of regime change through Color Revolutions. A huge part of Color Revolutions is big tech manipulation of the press and social media in foreign countries.
“Needless to say, the U.S. security state wants to maintain a stranglehold on political discourse in the U.S. and the world more broadly. They want to be able to impose propagandistic narratives without challenge and advocate for militarism without dissent. To accomplish that, they need a small handful of corporations which are subservient to them to hold in their hands as much concentrated power over the internet as possible.”
The letter pretty much admits that Facebook, Twitter, Instagram, Google are working for the CIA. And the letter these IC characters wrote, pretty much outlines how the world will react: “the Kremlin’s first actions of the war was blocking U.S. platforms in Russia“. And this will result in the rest of the World following Putin and unplugging from the US tech companies. A country would be an idiot not to given what US foreign policy has become. IMHO
“…conclusive proof of prior suspicions”
Sundance – NAILED IT! (But was there any doubt? Not by me.)
It is a violation of EO 12333 for a US Intelligence Officer to ask a foreign ally to spy on US citizens without a US warrant. And likely a violation of US law as well.
Does that mean it doesn’t happen? Nope. But it puts the Officer at personal risk every time he/she does it.
Not much risk unless one is a True Conservative. Then…
In a better world aka the world 30+ years ago, you’re right.
It is illegal, it should put reputations, careers and livelihoods at risk.
That is no longer the world we inhabit. The conundrum we face is how to wrest the control away for the malodorous miscreants that have hijacked our republic.
KILL it ALL! It does NOT SERVE America. Whoever devised this network is a seditious ass. It needs to be thrown out and develop a network that prevents censorship, serves America, lends INTEGRITY to our elections and prevents our adversaries like CHINA from propagandizing American citizens.
If you break up Big Tech into five separate companies for each previous company, that means the IC has to deal with five times as many management teams to maintain the same take. And eventually those five new companies will invest in different technologies, build new facilities and have different opinions on supporting IC programs. All of which will cost the IC more.
Sundance, thank you for covering this. The IC created social media as we see it today. The amount of subversion is amazing. This is the tip of the iceberg
“… any effort to break up Big Tech (Twitter, Facebook, Instagram, Google, Microsoft, etc.) would be catastrophic for the national security system they have created.”
I consider that a feature, not a bug.
Here are a few dots to connect:
1. The Democratic Party is facing electoral disaster.
2. The Democratic Party knows there is an underlying pro-Ukraine sympathy in the US population.
3. The Democratic Party is strongly invested in the “Trump is allied with Russia” meme. This could tempt the Dems to engage in a more reckless pattern of pro-Ukraine behavior, to get Trump to criticize it, positioning the Dems to claim this proves Trump’s treasonous allegiance.
4. Countering this would be the known aversion of the US population to more direct confrontations with Russia.
Bottom line: this tempts the Dems to act against the expressed preference of the US population, and in favor of their own electoral interests! This is a temptation that the Democratic Party has often succumbed to without hesitation!
My God…. this country is getting sicker and sicker…. a huge positive from Trump’s presidency is the whole thing opened my eyes… I thought my government was noble my whole life…. now I know different
But wait a minute. Isn’t there the possibility that a new and improved social media would actually enhance the security of the US? Why would these people not see an opportunity to be more intrusive? Is this simply the woke mind virus blocking the ability of people to see logic? Change is not always bad no matter who you are.
If I was a lefty, I would put operatives in place and encourage the breakup with dollars and support in order to get a better system for my sneaky spying.
chop off the head of the serpent
We the American people have purchased Vanguard and BlackRock for Big Tech, IC and Corrupt Government. The accumulated wealth was not used for us.
When you find a leach on your back or arm, for example, what should you do? First Aid Treatment.
I wonder if this is what Maxine Waters was talking about when she said “Obama’s got a data base no one has ever seen before”.
https://grabien.com/story.php?id=852
They don’t realize that half the country knows this same crew lied about the laptop being “Russian disinformation” — thereby proving what we already knew: 1. Their word is not to be trusted, and 2. They will call anything inconvenient “disinformation”?
Or they just don’t care. The latter, surely.
The military/CIA/NSA/DARPA, never, politely out of the goodness of their heart, turned the internet over to the American people to, “have and to hold until this day forward”… Like the FBI of today, they set us up, and now we are trapped in it… It was their plan all along.
“Until death do we part”…
I was curious why LeoNetta was crack-babbling on the news last night.
Good. Breakup intelligence too while we are at it. They are anything but
Snowden exposed this years back. Corrupt government is linked to corrupt social media.
No, it’s a national anti-freedom and control initiative. Every techy thing you do has some level of spying and information gathering attached. The ultra leftist government either wants you dead, paying all your income in taxes, completely under their control or marching to their dictates without questioning anything.
Here are some dots for you… Snowden revealed that in 2008 Google began sending the NSA all of the searches entered into their search engine. Snowden also revealed that the NSA claimed that in 2008 the NSA could monitor 100 percent of all internet activity (including Google searches) in Norway. Anders Breivik revealed in 2010 he spent 16-hours a day for 2-weeks using Google EXCLUSIVELY from his home in Norway to look up how to make a car bomb from scratch (which pre-cursor chemicals to use, how to prepare them,where to buy them, etc.) and then used the internet to have all the chemicals (including 7-tons of ammonium nitrate) shipped to his home address, using his personal credit card.
AND… the NSA had no record of his online activities and were unable to warn our NATO ally of this impending attack on its government… that could only happen if Google withheld Breivik’s online activity from the NSA. James Clapper was informed of this information within 3-days of Breivik’s massacre of 77-people in Norway.
The result, Pres. Obama ordered all US-domiciled News Media outlets to cease reporting on the Norway attacks. Coincidence?
x