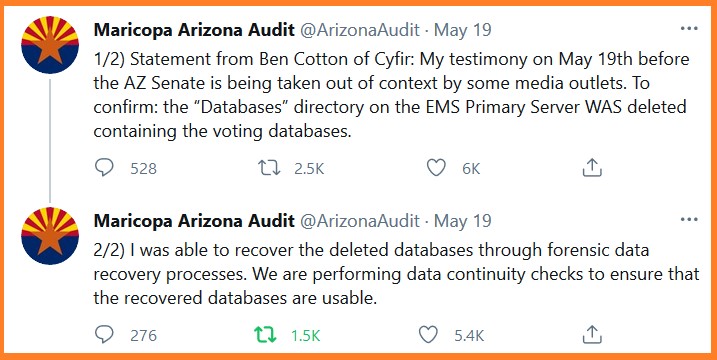
The media and Maricopa County officials have been claiming that voter result databases were not deleted; and they reference the ability of the auditors to recover the deleted information as proof the voter data was never deleted. However, according to technical forensic expert Ben Cotton, the ‘D’ drive of the EMS Primary Server was in fact deleted. It was only because of his extensive experience in the data forensics field that he was able to recover the deleted files; which is exactly what he said at the Arizona State Senate hearing on May 19th.
https://youtu.be/jrz5lht2Ofc
.
QUESTION – ““Did you determine that the D drive was deleted?”
BEN COTTON – “I did. We follow a very strict forensics acquisition process in which we don’t turn on a system if its delivered powered off. We remove the hard drives and perform forensics imaging with write locks on to prevent any changes to those hard drives. We produce a bit for bit forensics copy of that drive. In the case of the EMS servers, there were 6 drives. 2 drives were for the operating system and they were (unintelligible) configuration. So if something was changed on the operating system drive that would automatically be reflected on both drives.”
“The other four drives were data drives and they were in a RAID configuration known as 1 plus zero. So you have a volume that is mirrored but also data redundancy and striped across both drives. If I don’t turn on a system I don’t have access to the RAID parameters and the county did not provide those to us. so I had to do a discovery process to determine what that RAID configuration was. Part of that process is a scan across those drives to detect partitions of data and to also detect a master file table which is a record of all of the directories of the files that are contained in that partition, and a pointer to where that data resides on the hard drive. In the course of performing that discovery I found that an MFT that clearly indicated that the data base directory was deleted from that server. All of this may be moot because subsequently I have been able to recover all the deleted files and I have access to that data.”
Some points of clarification…
Because the D drive is used for data, it is not typically written to by the operating system. This makes recovery easier than a deleted file on the main operating system drive.
The database may have been deleted using the database manager rather than from the operating system tools. This may have been even less effective than doing it manually.
So… there’s a good chance that all of the database data is intact.
There is an excellent chance that all the data has been recovered intact. The reason being that the machine was shut down for transport just after the directory was deleted.
Further the drives were removed and imaged at the bit level, without restarting the computer.
So “someone” deleted the voter data and then switched the computer off before transporting the device to hand it over (grudgingly, after being legally compelled) to the auditors? Nothing shady about that.
Who deleted it?
Better yet, who ordered it to be deleted?
Except for the fact that all applications write data to any drive via the operating system as it controls the filesystem and direct disk access.
“all applications *CAN* write data to any drive via the operating system”
FIFY.
Yes, they CAN. His point was that the OS writes *very often* to the drive that it is installed on, so recovery on that drive is generally much more difficult that on other drives, because those other drives only get “intentional” activity, not nearly constant background activity from the OS.
The more writes to a drive, generally speaking, the harder it is to recover data, for several reasons.
Not necessarily. While not still widely in use, there were a number of operating systems that made that distinction EXPLICIT. Sadly, Windows wasn’t one of them which helped spawn some of its issues. But even MS has attempted to redeem itself in version 10 by making a number of directory trees inaccessible to normal applications write processes.
Amateurs, they should have hired Hillary’s team and used their hammer to the drive to make it unrecoverable. Just saying.
To those of us who understand the underworld jargon of computer forensics, he’s CORRECT.
Once the data is deleted, unless overwritten numerous times, IT CAN BE RECOVERED. Apparently Dominion isn’t smart enough to know how to ‘REALLY DELETE’ their Corrupt Voting Database. Congratulations to the forensics team, this isn’t easy!…Been there Done that many times. I had about an 80% success rate, sometimes the drives crashed and were unrecoverable. I had one instance where the drive crashed and we disassembled the disk platters, reassembled them into a working hard drive and recovered the data. It took a few days but we were successful. Now to find out WHO deleted the data. Hopefully there were some audit logs but I doubt it…
would the overwriting software be visible when searched?
maybe they always soft delete cause they know no-one-will-ever-question-it.
strictly speaking to delete operations.
fat32 and NTFS deletions are very rapid compared to milgrade wipe.
and to truly wipe with no chances of recovering other than a very slow electron microscope (SANS, FBI level kit), would just take a very very long time.
AND to wipe without evidence of attribution would take not just even more time, but skills and gear very few people actually possess.
thus, this deletion was speedy, simple, attribution remains preserved.
so the question becomes:
other than just minor frustration to a well regarded qualified forensic team, what would have been the goal.?
it would be akin to oiling the road behind the bank robbers car…
it’s not very effective, given the police have helicopters.
cyberninja has a fleet of helicopters.
deleting data in the way it’s been described raises quite a few questions about whether this was an intentional distraction.
I’m certain cyberninja is aware of this obvious issue.
it’s also important to notice the media battles being waged… MC has every intention to smear the auditors.
CN is simply responding with facts that factually respond to MC false narrative.
will the deleted data have wheels in any area of fraud or irregularity to outcome?
that remains to be seen
But these DNC/DS/ngo hijinks have been good enough for the last 40 – 60 years.
Attribution also depends on account controls. For instance, I can’t tell you which user used a shared account. Also if a switch user (su in UNIX systems) is not audited properly, I may not be able to see much either.
Yes and then there is the creation of accounts for new or dummy employees and also old accounts that don’t get deleted. A lot of times people are assigned accounts and for one reason or another never use them. We call many of them boss and you probably login into joe.boss with the original welcome1 password that they were supposed to immediately change. If you want to screw up your employers computer ot database you make damn sure they can’t trace it back to you unless you are an idiot.
Who deleted it?
This might help fill in the blanks.
To my mind the deletion points to someone who does not really understand computers, probably an election official. Of course it could have been some sort of accident, but I doubt it. Somebody of roughly Hilary’s level of competence attempted to wipe the data without asking anyone who knows anything.
I would be curious to know how often those machines are backed up and where those backups are. I also wonder in logins are shared or if there were unused logins created not assigned to specific users. There should not be of course but I suspect they run a pretty lose ship in Maricopa County.
Only two types of deletions possible, logical and replace. The logical, is a program belonging to the OS that simply marks the first character of the file name by replacing it, marking it available to the operating system for use. Replace is a program separate from the OS, called a lot of different things by various manufactures, it works by locating every byte of the existing file of your choice on the drive and replaces by byte, with a new byte in the same physical location on the drive, programmers choice for byte coding used. This is called shredded. It’s really just that simple.
If you could look into a disk after a good shredder has worked on a file it could show all zeros for example. Then it’s marked for logical deletion.
Soft delete is used because it is quicker (especially with rust disks, SSD have a different issue but possibly worse: wears out the disk faster). A LOT quicker.
Whether or not it is visible is highly variable. You can install utilities that allow you to hard delete things (existing file, fast deleted file, free space on the disk, possibly even an entire disk), but most people don’t. It could theoretically be coded into the program. My experience is that usually it is done with an external boot device because the process is SO time consuming it is ONLY done when you are preparing to dispose of the disk. I think it has been about 10 years since I’ve been asked to do that. Process could take anywhere from several hours to several days depending on the size of the disk and the precise protocols to be followed. I think these days places that engage in the practice actually purchase either a degausser or a shredder because even at the cost of the device it is cheaper than the multi-pass wipe process, even though the wipe process is mostly a start and leave it process.
Maybe, maybe not. If they used a system program to erase the data disk I think it would be visible in some log. On the other hand if they used a USB or DVD that loads to memory like Parted Magic or Gparted, I don’t think it would be visible. Then again I am not an expert, maybe someone can clarify?
I’ve done a platter transplant before, but that required a filtered positive pressure glove box. It’s not a quick exercise.
As to Dominion, they are unlikely to be the culprits. They would have used random overwrite on all sectors were the database files were.
The criminal who tried to delete the subpoenaed data clearly wasn’t a computer expert.
Reeks of Board of Supervisors, Katie herself. Im waiting for the results of the fire.
Somebody somewhere is very worried to have done something this clumsy and ineffectual. Whoever they are is now the weak link in the chain whose only way out is to rat everyone involved out if/when they are identified and I think they will be identified because they are obviously not very cognizant of how data security works.
I hope you are correct. I worry that even though they are that worried and that trapped they are still even more afraid of being Epsteined for snitching.
If he only used delete he was a computer idiot. The previous post on shredding, overwriting and zeroing is what an expert would attempt. Yet that all takes time, which the culprit may have not had when the subpoena was ordered. Yet the culprit must have had some warning to have deleted the data, a court insider?
So now that this has been pointed out, Dominion and the crooked politicians will make sure to be more thorough in the future.
Next time they’ll use a cloth. I just don’t want them getting the expertise of anyone like Konrad, regitiger, Mick JT or Baby El! ?
Exactly! This is what happens every time we discover any of their fraud, deception, corruption, etc. they just get better at hiding and this is because they are never held accountable in the first instance.
Deletion by the computer’s software simply replaces the first byte of the name field with FF. Restoring that first byte restores the file.
It’s even easier when the drive is deleted rather than deleting each individual file as only the drive name need be restored.
Restoring the Drive’s name should instantly restore all files within.
For a brief time, I worked with a disk drive forensics expert. He was engaged in imaging drive platters, removing one layer of magnetic media then imaging the drive again. This allowed him to track changes over time.
Sounds a lot like what Ben Cotton was preparing to do.
Been in the computer field since the beginning of hard drives and I concur.
Writing over a whole hard drive to erase it is very time consuming, it requires multiple passes and it’s not fully guaranteed to work. Apple, for example, recommends a minimum of six consecutive rewrite passes over the whole disk and still is not guaranteed to work 100%.
There are better ways. The expensive one is with a specialized degaussing box. Drives can be erased by degaussing just like magnetic tape but it takes a lot stronger magnetic field. So much so that it needs a secure enclosure.
The cheap way is by physical destruction, the ole standard 15 pound sledgehammer. It too requires multiple “passes” though, and obviously leaves evidence of tampering.
I worked in tape storage for Sony for 15 years (also 10 years in optical storage). Degaussing would only apply for the entire tape. We were not able to recover data on an overwritten tape or erased tape (short or long erase). This was streaming DDS, AIT and SAIT tape drives. I wrote diagnostic software for Sony tape and optical drives.
With hard drives manufactures have tools that allow access to a sector address on specific platter.
I also worked for WD for a short while.
Asking as non-tech grundoon, how does the “bleach bit” app work?
This is a really good explanation of what bleachbit does and how it does it. Not TOO techy.
Link: Bleachbit Documentation
As I mentioned manufactures have diagnostics tools to access individual disks in the hard drives. The drive would be put into a diagnostic mode and manufacturer sw would be used. I recovered Sony Optical disks and tapes used by NSA and others like DIA. Believe me they had no idea how to recover the data. I didn’t even have a security clearance. Usually Optical disks were scratched. Sometimes I could buff out the scratches but not all data was recoverable. With damaged tapes if not readable there was nothing that could be done. There isn’t any Government agency of 3rd party company that can do more than the manufacturers of the drives and media. Period end of story!
Physical destruction is the Hillary Clinton preferred method of evidence destruction.
I wonder why these crooks didn’t call Hillary to bring her “Bleach-bit“ goons over? They might have shown a little more competency. They sure are trying desperately to hide SOMETHING! And that something HAS to be election fraud, what else could it be? They must be in full panic mode right about now. Maybe Dementia Joe will loan them some of his diapers. Got a feeling they’re going to need them.
so how many people had access to these machines to do this, it can not be that many, do like they treat conservatives today, lock them all up in solitary confinment and do not let them out until one talks.
Most of the people involved in this fraud were pretty amateurish. They thought they got rid of the fingerprints by doing a quick wipe down of a few things, thought they got rid of the body by throwing some leaves on top of it, and thought they had disguised themselves by all wearing pencil thin mustaches.
True, but good wiping takes TIME. I use Darik’s Boot and Nuke DBAN to wipe, overwrite and zero. The process takes hours on just a 250 gig hard drive. Then I do it all again. KillDisk is another good alternative. If you really want security, you can use the 35-pass Gutmann method. Using Bleachbit like Hillary did will not prevent recovery.
I worry that with all of the revelations concerning audit processes, the cheaters are learning which actions they took that can be discovered, which mistakes they made that can be discovered, and which changes/improvements they NEED to make in the future in order to cheat better, with less detection – detection that could be used as evidence against them.
If that is true, then us on the Side of Right are closer than ever in our pursuit. If those on the side of Tyranny are one step ahead of us, all it takes is for us to keep running.
Easier said (written) than done, I know—but we’re right on their tails. The best people are on this, and the Narrative Engineers’ schlepped-together Narrative on Arizona is falling apart like clay from iron.
Much more and the country might run out of gas or luck, then crash and burn.
Don’t worry, any cop will tell you all criminals leave tracks. It’s sort of magical mystical that lies subvert logical thinking and mistakes are made. In the digital realm there are so many, many ways to screw up and get caught. With the scope of election touchpoints, locking down mistakes just will never scale. Our local up to state up to feds partitioning makes it so the Dems deviously targeted only a handful of critical cities and tried to lock those down. A lot of mafia lockdowns of small groups of loyal to the cabal were paid and threatened, have no doubt. Including judges. I’d bet anything dominion’s algorithms cheated on a much wider scale. The thing for the Senate to do is run surprise audits in supposedly undisputed areas as control checks. That would be very telling since they didn’t print or insert fake ballots probably in those areas and buy everyone off. A forensic audit would show more glaringly.
Your worries are well founded and will probably bear out the NEXT TIME they cheat, my educated guess is the 2022 election. Once our side finishes pointing out all of the ways they were caught, but not held accountable, they will have a year to impletment better, less detectable methods of cheating. This is why we are where we are and they know it.
For the most part criminals are A) stupid and B) lazy. If they were not both of those they would know it is easier to make an honest living. They seldom learn and usually can be caught if somehone has the time and resourses to chase them down. The people who stuff ballot boxes are not going to take the time to learn how election machinery works. They know that once bad ballots go into the box they will never come out and will be counted. From there they count on the guys/gals they got elected to protect them. In this case somebody paniced and did something that will get them caught or worse.
That the ‘D’ drive data directory was deleted indicates to me that (1) The individual(s) who deleted the data were incompetent and that (2) They were desperate; if either of these two possibilities are true, it’s likely that there was a (lame) attempt at a cover-up.
It’s unclear to me whether this could have been Dominion or Maricopa BofS personnel.
I am kinda leaning that way myself. As much as I dislike Dominion, I would think they would be more competent than this.
This screams incompetence. In fact I would bet the BoS has a awww crap moment when it comes out who did this.
Don’t get me wrong. The BoS are in my estimation corrupt. Just not too sure their own ding dongs did the deed and lied about it.
Same, same. They need to go down.
Agreed…
Corruption and incompetence almost always go hand in hand. From the Maricopa County level to the State, then across State lines, to National, to Dominion/ES&S/et al, and to transnational criminal organizations. I consider it merciful that they are thus more or less self-limiting, but there is a line that will at some point be crossed.
It’s as the corrupt become less incompetent that the true danger to humanity arises.
Think of it as the Clinton EOB staff removing the “W” keys from the keyboards before they left.
The Dominion people would not be that stupid. Can’t say the same for BofS personnel. I am still up in the air about Dominion. They certainly are acting like they are guilty of something but I still believe 95% of the fraud in this election was multiple forms of ballot box stuffing.
I think that any and all Journalism departments, schools and programs in higher education should just update their appellations to “Narrative Engineering” or—more to the point—Psychological Warfare.
Having taught and chaired in one for what were the very worst years of my life, I know that it’s a long-overdue change.
The only bad thing about telling how he can recover what has been deleted is now the enemy will be much more thorough next time
The more they dig a hole, the deeper it will get. A good audit reveals EVERYTHING.
Did he tell everything? It is obvious that some are not viewers of columbo.
In addition, the end game is to eliminate all machine (computer) tabulators (scanners, counters) in the election process.
The crooks can learn all they want about an obsolete process.
We are really proud of our current day super patriot trackers . They are reading the digital tracks left by the “gang that couldn’t cheat straight” just as our founding fathers trackers read footprints and broken branches to hunt down the enemies of that day. They can run but they can’t hide and we will get them.
Criminals always slip up eventually. Even the very smart ones.
Alternatively they are busy working on Mi, Ga, Nv as this unfolds. Send in the National guard before they do. Then they will resort to arson or the electronic attack aka Nashville.
Not really. All of this has been known since at least 1985 and is common knowledge for ANYONE who works in IT. I’m picking 1985 as the inflection point for personal computers starting to become accessible to most people. I can’t imagine the people working on mainframes who proceeded the microcomputer didn’t have similar tools at least for disks. Granted, it is sort of hard to erase a punch card. Spindle, fold or otherwise mutilate sure. But not erase.
And the FBI could not recover Hillary’s emails???
BS.
the most likely explanation is that those servers and comms were retrieved.
that we the people were not put on the notification about contents is perfectly in line with DOJ, DOD, ABD NSA level power.
think of it this way:. RADM ROGERS informed TRUMP and his transition team they were targets AND subjects to state surveillance WITH embeds!
do you think the secret police spy state is about to even tolerate what that apparatus was, and what data was collected and whom the embeds were?
the secret police spy state is focused on compromising ALL powerful people and orgs.
letting us now what they are up to is antithetical to the agenda.
same thing and argument can be made with state fusion centers.
it’s secret…and unlikely to change in it’s secret missions and ops.
I don’t feel safer…I don’t find more freedom and liberty.
so obviously, these powers are not furnished to protect anyone except those that are sufficiently powerful and can be coopted to the self interest of the secret police spy state and TECHNOCRAT who actually run the show around the world.
I think they had them all on Wiener’s laptop. Naturally the failed to review that and instead faked that they did in a too-short time.
When he says “ray” instead of “RAID” configuration, I seriously wonder if ANYTHING in this article can be trusted…
It’s weird, whenever someone talks about something I happen to know a lot about, it’s invariably wrong. The rule has always applied to MSM, and now clearly also to alternative media. It must be a law of nature, or something…
Please elaborate if you can
RAID (“Redundant Array of Inexpensive Disks” or “Redundant Array of Independent Disks”) is a data storage virtualization technology that combines multiple physical disk drive components into one or more logical units for the purposes of data redundancy, performance improvement, or both.
It’s been corrected. :^)
Cool
Just to be clear, when they reference “RAY” in this article the person speaking actually is say “RAID” configuration. In the first instance, and is typical, the operation system drives where in a RAID 1 “mirrored” configuration, and I suspect the D / Data drive was a RAID 10 which is a mirrored RAID 1 for performance PLUS redundancy.
If you want this audit to have any influence just give us the bottom line finding and skip all the tech mumbo jumbo that nobody understands and just makes your eyes glaze over.
You may be confusing the auditors’ discussion with No Child Left Behind.
It is your responsibility as an informed citizen to keep pace with the ongoing revelations. Don’t be the slow poke who can’t follow the trail of evidence, allowing the scent to grow cold and the prey to escape.
Dear “Maricopa County Election Officials …”
“The Arizona State Legislature” equals: “your boss.”
They’re the ones who created “the job that you hold.” They’re the ones who established the procedures that you were to follow, and the standards that you were to uphold – “under penalty of law.” Therefore, as “your boss,” they’re now perfectly entitled to ask questions and to demand truthful answers. Which you seem rather curiously reluctant to give them.
They’re also entitled to independently satisfy themselves – by whatever means they see fit – about “what you were actually doing.” Simply because this is both “part of their job,” and “their duty” as representatives of the people of the state. Once again, you seem rather curiously opposed to this.
“The Guilty Run When Not Being Chased.” Wouldn’t you agree …? ?
Varmints in general make the most threatening noises when they’re cornered.
No one is taught the structure of government anymore, unfortunately. These little BOS tyrants actually act like they are an independent private corporation for crying out loud. It’s sickening, the insolence.
Yes. This.
Just like the states created the federal government. The federal government was created with certain limited powers, but has become the Leviathan, routinely dictating to states. Our Founding Fathers wouldn’t recognize the place.
They can have all the “accidents”, “fires”, etc., they want, but I suspect these IT forensic guys are professional enough to have off site copies of everything they need.
Sure, that wouldn’t keep the rats from claiming those off site copies were somehow manipulated….
What will be interesting to see is if this calls into question down ballot races. If County Commissioners, local representatives, Senators, etc., all benefitted from rigged elections and that is shown, how fast will the recalls start? Or demands for a new election?
Which leads to the ultimate question: If down ballot races are affected by this fraud and action is demanded, what action is possible to resolve a stolen Presidential election?
Publicly hanging the faux Victor and his protégée?
Perp walking his handlers, Susan Rice and o himself.
Or, reverse those consequences.
This much is clear: “It would actually be illegal to try to deploy a financial or medical system that was designed like this.” Security-aware statutes such as Dodd-Frank, Sarbanes-Oxeley (“SarbOx”), or HIPAA would have made it impossible.
And “it’s not just the software,” although there were software vulnerabilities at every level simultaneously. It also extends into virtually every aspect of the human processes. (Which, by the way, the above-mentioned statutes also address.)
“Folks … we’ve been naïve. In fact, we’ve been stupid.” We paid very thorough attention to finance and medical records, yet it seems that we utterly neglected this most-important thing of all.
“Security-aware statutes such as Dodd-Frank, Sarbanes-Oxeley (“SarbOx”), or HIPAA would have made it impossible.”
Ironically, those sort of frameworks would give the Federal Government a foot in the door for creeping authority over elections! :^p
HIPAA isn’t about protecting patient data confidentiality. It was always about streamlining and standardizing data portability between payers in the health care management system.
I suspect that financial information is equally transparent now.
I don’t consider ANYTHING to be confidential or “secure” anymore, unless I write something on a physical piece of paper and keep it under my mattress.
You are right. The irony is that the big push for security and audit in financial and medical records comes from the same crowd that resists the very same level of integrity for the voting process with every fiber of their being.
Even XKCD knows voting software is evil and corrupt:
https://xkcd.com/2030/
Yeah, yeah yeah. I’ve read the brochures too.
But I also work in the trenches. So I KNOW better.
Another interesting question that will be answered is who in the county deleted this file?
Dominion would have known enough about the drive configuration to know a simple delete of the files would not be enough.
A county or other employee with Administrative access deleted the file, which puts the lie to the BOS claim they didn’t have those passwords.
Was Ruby’s daughter the BOS in Fulton County ?
Apparently, the Database Administrator had an I/O Problem (Idiot Operator!)
Step 1 – Deleted Database
Step 2 – Power Down Machine
Step 3 – I/O problem, the data was never overwritten, they thought it was “gone” alas, though, it was easily found!
I haven’t heard that lame excuse since the late 1980s when the computer ignorant thought they could BS others as easily as they BS themselves.
More accurately, their justification is akin to saying, those paper documents weren’t “destroyed” since the investigators were able to piece together their shredded remains
I’m shocked that the media and some Democrat County officials are trying to mislead the public.
Of course, I’m not really shocked but I am glad that there are courageous Arizonians and sites like CTH that will call out their lies unlike the GOP’s sell out 35 that bow or curtsy to Pelosi on demand like she’s royalty.
It is a constant job to counter the lies and the spin of the concerned and fearful left.
There is no small fish in this 2020 election scam. Charge and send them to jail.
I keep hearing ‘fraud situated everything’ !!
How much (quanity and quality ) fraud is required?
It sure looks like there was enough to affect ‘outcome’.
But … the Journolists at mockingbird Inc. told us it wasnt!
Vituates not situated!!
Although the cabal definitely thought they were pretty well situated too !
Not sure if this question has been asked… but something to consider.
So Maricopa IT Braintrust insists that a.) the database files were NOT deleted, and b.) Ben Cotton is misinterpreting what RStudio is telling him about the “modified” dates shown in the screenshot that was presented.
Of course… that’s just misdirection… they’re jumbling the database file modification date into Cotton’s claim that the files were ACTUALLY deleted and ACTUALLY recovered, and hoping it’s confusing enough for Tapper and Maddow to make something of it.
As part of that misdirection, the Maricopa IT Braintrust informs everybody that the modification dates (4/12/2021, IIRC) would represent the date that the MySQL instance was shut down… a process that causes the database files to be updated, thereby updating the file modification dates. I don’t know the details of the shutdown, but, in the least, internal MySQL data structures (not the EMS data itself) would be updated as part of the shutdown.
Ok… so that’s how it works with the MySQL database. But this raises a thorny question… in my mind, at least…
Why was EMS/MySQL shut down at all on 4/12/2012?
For what purpose would the EMS be running beyond, say, the two audits that were conducted in December (or maybe it was January)?
At some point, EVERYTHING about the November election needs to be LOCKED DOWN. In fact… that’s what they do… they literally seal up the tabulators, pack up the ballots, store it all away in a secure location, etc. etc.
So… why exactly was EMS running on 4/12/2021? It should have been shut down and packed away WELL before 4/12/2021, one would think. Shut down, locked up, stashed away in a locked room.
My hunch is that somebody booted up the databases to delete the data itself… OR they modified the database content using data that was prepared outside the EMS in order to try to correct the ballot counts (I bet Dominion provides this service for a nominal fee)… then doubled-down by deleting the database files.
So it’ll be interesting to find out what exactly was recovered. BTW, I think I saw the “LDF” files in that screenshot, which would be the transaction logs… which could give you info on what data was modified/deleted.
I love the openness and transparency of the Democommunists even more than I love their kindness and compassion.
These Ninja boys need to sleep with one eye open and have redundant data security and disemination plans in place. They took out Justice Scalia and this AZ domino has arguably larger implications
DOJ needs them alive to go in based on Katie Hob Knob’s ridiculous claim that everything is being tampered with, arrest everybody, confiscate everything right down to the blue Bic Pens that weren’t supposed to be there, and have Emmet Sullivan put the whole lot under seal. Of yeah… they’ll need some of that Solitary Confinement thrown in there, of course…
We can count on the truth of the politicians and unionized government employees are a top to bottom crime gang. Government employee unions /associations need to be criminalized.
Yes, things are not deleted permanently. You need special Wipe software so that deleted files are more than covered over.
And don’t forget the Cloud. Election crooks trying to delete files in storage may forget about Cloud backups.
I know these machines are not supposed to be connected to the internet, but we have since found out many or most of them are.
Hillary’s bleach bit?
Wow. These Dumb Onion people are dumber than even I thought.
Deleting the directory without a degauss of the hard drive or replacing all the data with zeros is really dumb.
All those Dumb Onion people did was remove the file (the directory) that pointed to the location of the files on the hard drive. The data was left intact.
Any good hacker knows this.
All stupid criminals are caught for being stupid. How was it the Dumb Onion people haven’t been caught before now?
They can’t do it without physically accessing the machine. This is a problem when you look at the thousands of machines out there. They either will have to destroy the complete system or prevent audits. preventing an audit might be easier.
They are busted. It is a matter of time. But what will be done is the most important thing.
He lays everything out in an orderly and logical way so that you’re able to follow along with what steps were taken even if you don’t know how to do anything he’s talking about. Unfortunately, there are a lot of people out there who would make no sense of that block of text; they simply wouldn’t understand how one word connects to the next. They’d see only jumbles of words suggesting triggering concepts which prompts them to scoff or feign being offended.
Sometimes I listen to the dialogue of The Professionals In Charge and feel my spirit sinking…
It’s not in their “lived experience” so it’s just Charlie Brown adults talking… whomp whomp whomp wamp whomp.
Maricopa Supes don’t want to labeled Bozos of the Year and shown they ran a shoddy election. What do you expect them to do but obstruct, obstruct, obstruct. Self-preservation is a powerful motivator.
Don’t get distracted by side issues and petty egos- push back, keep the record straight and continue the counting and verification. That remains job one.
We have your back. Yes, this is the hill to die on – even if nothing is found.
The stakes are too high and as another person recently said – even 45% of voters thinking there could be election fraud is too high – it should be ZERO percent. You are working to make sure there is 100% faith in the next election and that is a noble but messy calling.
Fraud vitiates everything.
DePerno points this out too, but who has to do what to get the frauds out and the rightful winners in office? The left, likely some of the very people responsible, or at least aware of the fraud, control every facet of government.
I hope the Senate understands this clearly. It’s illegal to even attempt deletion, a momentous Federal crime. Who had access? Who did this? Who needs some water boarding to spill on others? arrest them all NOW, separate them and start asking questions like real justice for all of America is at issue here.
AZ Senate, maybe and in their case they MIGHT try to do something about it.
US Senate? Irrelevant. If they care at all, they care that the evidence is buried out of site.
I know this because IF they cared there would not have been a rush to rubber stamp an election with a multitude of questions about accuracy and authenticity.
Jerks! Lock ’em up!
Jerks? Yes. Criminals, traitors. Hang ’em.
I have been in IT since the early 1970’s. This account is entirely consistent with my experience and the way Windows and RAID works. In Windows, when a file, folder or directory are “deleted” by a user-level program, the directory entry for it is marked to indicate that status. At that moment all the data blocks that file occupies are then available for Windows to allocate to any other program that asks for space on the disk. So you can get a recovery that is partially complete with blocks missing. There are utility programs to do complete integrity checks on a database which must be done in this case. If the machine in question was shut down in a normal (orderly) manner after this “delete”:operation, all the data of the target database would still be completely recoverable. The person who issued the delete was too smart by half.
one thing for sure,when the originals of the adjudicated ballots aren’t there, boom.
You can be sure that Dominion right now has someone developing a failsafe delete function that erases all data across the whole stack, and hides that it did it.
Not feasible.
Until the voter is provided with a “certified” receipt showing their vote as well as visual feed back when they cast a ballot, ALL remains “suspect” as there is NO proof how a voter actually cast their vote. The only true audit is a sampling of voter receipts.
I voted yesterday in Allen, TX as part of the city council run off election. Still, they are using machines and when one FEEDS their “bar coded printed paper” ballot into the LAPTOP as step 2 in the voting process…my selections DID NOT appear on the computer screen where I fed by ballot. The system is still broken.
I pointed out these facts to the voting officials on sight and got ugly stares from them and the cop on duty at the polling site.
There are many comments here bemoaning the fact that these bastards will learn all of the forensic tricks from this audit and use them to better steal an election next time around. There is a simple solution for this, don’t allow these machines anywhere near an election. paper ballots only. The only people who want [supposedly] quicker results are the 24/7 media who want to brag about being first to call the winner. I have no problem waiting till 1am or the next day to find out who won.
I have no problem waiting three days or even a week before knowing who won, if that’s what it takes to make the election counting process fully secure from tampering, and also fully auditable after the election.
In recent years I have come to the conclusion that such a LONG period for counting the votes would actually be beneficial to the Republic. It would put an end to the incessant drive to Call the Election First and in the process F* up the election itself.
I’d be more surprised if democrats weren’t misleading the public.
Misleading the public is pretty much what they spend all their time on.
Liberals mistakenly thought no one could outsmart them.
We have access to that data!!!! No wonder their running around scared! I’ve lived here since 92 and watched the elections deteriorate starting with Matt Salmon being robbed!