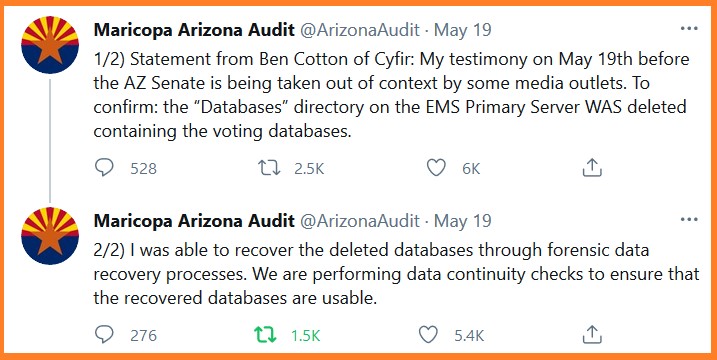
The media and Maricopa County officials have been claiming that voter result databases were not deleted; and they reference the ability of the auditors to recover the deleted information as proof the voter data was never deleted. However, according to technical forensic expert Ben Cotton, the ‘D’ drive of the EMS Primary Server was in fact deleted. It was only because of his extensive experience in the data forensics field that he was able to recover the deleted files; which is exactly what he said at the Arizona State Senate hearing on May 19th.
https://youtu.be/jrz5lht2Ofc
.
QUESTION – ““Did you determine that the D drive was deleted?”
BEN COTTON – “I did. We follow a very strict forensics acquisition process in which we don’t turn on a system if its delivered powered off. We remove the hard drives and perform forensics imaging with write locks on to prevent any changes to those hard drives. We produce a bit for bit forensics copy of that drive. In the case of the EMS servers, there were 6 drives. 2 drives were for the operating system and they were (unintelligible) configuration. So if something was changed on the operating system drive that would automatically be reflected on both drives.”
“The other four drives were data drives and they were in a RAID configuration known as 1 plus zero. So you have a volume that is mirrored but also data redundancy and striped across both drives. If I don’t turn on a system I don’t have access to the RAID parameters and the county did not provide those to us. so I had to do a discovery process to determine what that RAID configuration was. Part of that process is a scan across those drives to detect partitions of data and to also detect a master file table which is a record of all of the directories of the files that are contained in that partition, and a pointer to where that data resides on the hard drive. In the course of performing that discovery I found that an MFT that clearly indicated that the data base directory was deleted from that server. All of this may be moot because subsequently I have been able to recover all the deleted files and I have access to that data.”
Let’s hope they find enough discrepancies to over turn the state being given to Jo(k)e Chi-den.
I hope they find the T (Trump) drive!
Care to elaborate as to what your reference to the ‘Trump Drive’ means?
Go to “the Professors Record” Dr David K Clements on Rumble watch his interview with a man named Daniel… it is about ballot printing and adjudications here in AZ, alarming! I voted early here in Maricopa and I am positive my ballot was adjudicated. This is another reason the BoS, SoS and election recorder are scared about the ballot count! I am guessing Trump won by 200K- 400K.
As far as canvassing go to UT “Patriot Liz Harris” she was in the hearing in Nov and has done great work. I think they will find phantom voters galore!!!
Dan Sundin? Cann Con and David were just talking about him on a podcast last night tht I posted this AM. Sadly, it was already taken down by yt before I even finished listening to it.
AZ Ballot Printing Company “Runbeck” Causing 11%+ ERROR RATE!
by The Professor’s Record with David K. Clements
Published May 19, 2021
In this interview I interview patriot Dan Sundin over his findings on the company “Runbeck.” Maricopa Voters—-we have a problem.
https://rumble.com/vhbebf-az-ballot-printing-company-runbeck-causing-11-error-rate.html
According to media reporting I saw, the deleted directory was “LOST” and the recovered directory became “FOUND”. It was written to make the audit team to appear incompetent.
Yes, the data was deleted days before the machines were moved to the Coliseum for the audit… it was shown at the hearing…. they are nervous!
If the system was truly in the condition described, it was a malicious act.
You cannot accidentally destroy mirrored OS drives and data RAID configurations without intent.
To destroy those, you have to get into system administrator tools, separately find and destroy the data and os configurations.
The mistake was in not realizing forensics tools can rebuild the RAID after the config is wiped.
If need be even smashed hard drive platter info can be obtained through electron microscope analysis.
So if you really want a hard drive wiped , take it out and toss it into the ocean.
That or get a solid state drive, much easier to wipe and stay wiped.
The cheaters should have just thrown the drives in the garbage and installed new ones , then played stupid.
I would assume that is exactly what they did….All the rest is smoke and mirrors
It wasn’t an array reconstruction, it was an undelete of the files and directory path where they were as indicated on the MFT.
Bingo! Tech is magic to those who don’t know it can bite them in the A$S
Translation= ✓Democrat Criminals at work. We need Paul Blart.
We need Judge Isaac Parker of the old west.
At least Blart was honest. Bumbling but honest!
I am so glad that we have Brainiacs like this guy on the case in Maricopa! They are not fooling around and will get to the bottom of this cesspool before long. No wonder the Demo Commies are freaking out.
Folks are waking up. We did not know the cheating was all over all the elections since probably FDR…The RINOs are complicit. We just didn’t. The media is for power & money only. Marxism has been here in the USA for more than a century. I hope American citizens keep up the hard fought fight. We can do this.
It was the neoconservative RINOs who conceived of NAFTA and pushed for the great transference of U.S. jobs, U.S. capital investment, U.S. invention/innovation to foreign nations, and enabling the importation of foreign workers, along with the Democrats. Considering they did THAT, why do we think RINOs wouldn’t join the Democrats in covering up election fraud?
CON servatives here in Canada under our PM Mulroney was in bed with your Rinos and pushed through NAFTA.
Lying Brian Mulrony.
He and the CONserves brought in that much hated VAT tax , the GST.
A great book about him by Peter C . Newman ” On the Take ” greatly explains that POS PM.
I still can’t get his song and tap dance with Regan out of my mind.
” Irish Eyes are Smilin “.
Barf.
Including the trade deal.They traded huge amounts of illicit drugs to eliminate competition from US native workers.
Both sides use Dominion systems to win elections. The proof is relatively easy to find.
Start with a Texas IT forensics company video on the 2019 Kentucky governor race where “Andy” won on late night vote flips.
Our “betters” are selected, not elected. For at least a couple decades now, election day was a show for the little people.
Nobody in leadership (except Trump) got there without approval and, quite likely, some Epstein-ish blackmail video controls.
Absolutely, Beshear won both elections by fraud. Same with Bel Edwards in LA, most of which uses Dominion as well.
They have to cover it up because the were in on it as well.
Election Fraud at the national level is deadly…
Election Fraud at the state and local level in the cancer that collapses and transform regional pride and tradition….School Boards, Sheriff, judges, attorney generals, prosecutors etc
better be prepared for a hamas missile strike
If voter fraud is definitively proven, but nobody reports it (and / or covers it up, spins it, or censors it) and nobody prosecutes it (or more likely falsely prosecutes those who are uncovering the fraud), is it still fraud? /sarc
fraud is fraud
justice can come from many out of the box ways
Yes.
Sincerely,
The Second Amendment
Election audits are good and hopefully reveals undisputable evidence…
The evidence to me was the thuggish behavior of all poll workers in the contested states…The exact behavior patterns in Az, Wisc, Mich, Pa and Ga…what are the odds? Couple that with all the state election Boards fighting an opportunity to prove the actual results .
Continue the audits, but my eyes and ears provide me with conviction and truth…
He may indeed be a Brainiac, but what the process he described here is actually computer forensics 001. Anyone who has ever in any way shape or form even touched on it would know this. And you can’t work in IT these days without touching it. I carried many a disk to the forensics team so they could perform JUST these operations. In my case they were usually looking into malware/hacking attacks. No, I didn’t do the analysis, I was JUST the courier.
And that may quite a lot about the morons behind the voting machines.
These types of tools (and the knowledge behind them) have been used since CP/M days.
IIRC Norton Utilities was one of the first high profile Apps available that allowed you to find “lost/deleted” files on MSDOS FAT formatted disks – Floppy and HDDs.
electronic forensic experts can reassemble the data off a magnetic HDD in most cases….in many cases when you first delete it, it only removes its reference in the registry so it does not show up as a file….it takes multiple times of rewriting data across the sectors that that file was stored at to prevent recovery
Hopefully multiple backup copies exist… in every state!
Yes, that’s how one effectively “wipes” a hard drive. Unless you use a physical hammer like Killary, of course. You have to overwrite it with something else, usually several times, if you really want whatever it was truly deleted. Of course, a hot fire works just fine, but it does leave a little more trace evidence? LMAO!
even using a hammer does not make erased data safe….if they have the pieces of the shattered disk they can recover enough data in most cases to infer missing parts of the file
MSDOS – you mean KDOS (Killer DOS) +2 lines of code changed? I believe Microsoft bought KDOS from Seattle Computing Company for $50,000 … as big a lopsided deal as our purchase of Alaska?
I recently watched the Bill Gates documentary on Netflix, which I enjoyed, but I believe he said they were working like gangbusters on MSDOS. Not!
He also claimed to be the first multi-product company. Borland also fit the bill. Any others?
The big takeaway from the MS/Seattle Computing deal was what MS did afterwards. Gary Kildall of CPM had already blown off the IBM team seeking to buy an OS and went to play a round of gold. Apparently Gates heard, so he invited the IBM team to look at DOS. The IBMers had so much faith in their ability to market their h/w system (put together by a rogue group in Boca Raton) that they didn’t request EXCLUSIVITY upon licensing DOS, and the clone race began. We had BIOS wars too!
golf not gold
Oh there were a LOT of shenanigans in that whole deal. Like Gates not letting IBM run the computer because he DIDN’T have a working prototype. They jury-rigged a fake program so he HAD to be the one running the software.
all hardrive manufacturers have developed disk tools. HP is a early pioneer.
I’ve used hobby level apps, like hirems tools and other “live disk” so the drive in question can be mounted in such a way as not to create data loss.
but in the big league, true robust drive analysis is pretty much a laboratory conditions type of work not available to almost anyone outside of perhaps 20 labs in the US.
When you realize the possible chicanery of the secret police spy state involvement, and at least the closed wall proprietary nature of dominion writing custom firmware and drive microcode, I think that’s this team will do well to not assume anything when examining these drives
Yep. I used that tool back in the day. Peter Norton was a cool dude.
Quite or quiet?
was actually supposed to be
And that may say quite a lot about the morons behind the voting machines
Interpretive logic of the media narrative builders:
Having recovered the data directory means it was never missing.
Since it was never missing means it was never deleted.
Analogy to interpretive logic of media narrative builders:
Having dug up the body in the suspects backyard means it was never missing.
Since the body was never missing means it was never murdered by the suspect.
The Woke Cancel Logic..Brainiacs Cancel The Woke
Precisely. The Left wants to control the narrative so they make stuff up that sounds good. In this case, the Democrats lawyers will force the State Senate to disprove their assertion that the files were never deleted.
Anyone with some machine knowledge knows when you erase files on a PC, it only deletes the pointers to the data. Many free recovery tools can easily recreate the pointers and allow you to access the data again. In the case of a RAID system (sounds like a RAID system was being used to store the Maricopa data) its whole designed is to guarantee recovery of data thru built in parity info stored on each disk in the RAID system. Bottom line it is really hard to loose or erase data. What is hilarious is the Maricopa officials thought they were really smart and could get off the hook by just deleting stuff. What is even more hilarious is that now there is an attorney that is mandating that the auditor team needs to “save all the documentation they are creating” which is the whole point of the FORENSIC AUDIT – LOL.
I was told the only surefire ways to erase data are:
A. Large magnet
B. Destroy the hard drive
C. The best – A + B
I hope all Patriots in states are verifying backup copies & protecting existing copies / systems.
I also believe President Trump was competitive in California.
Your last point is 100% true. And hilarious.
The audit creates evidence that stands up in court. Well, if the court isn’t corrupt and actually hears the evidence (unlike SCOTUS).
I can delete data and replace it and there is NO ONE AND NOT A SINGLE TECHNOLOGY that can notice this.
this is the entire premise of stuxnet type exploits.
the only…only way…to detect it is from indirect observation…such as noticing centrifuge devices destroying themselves.
in the industry this kind of exploit is often called
file less exploits.
of course there is much more to it than I could explain in a few paragraphs.
but the reality is that I. can effectively after the state of data and preserve the data that would be impossible to notice if you audit said data.
deleting data would be a very amateurish method to exploit a voting machine.
altering results by manipulating the machines with a file less exploit would be how I would do it.
Kaspersky wrote about stuxnet and how they finally determined the nature of this never before seen exploit.
since then, stuxnet type attacks and other file less exploits have predominated the most serious and technically challenging exfiltrations and attacks.
if this is the case here, this forensic team will only get so far my examining the drives and data.
they will need to forensically examine the hard data (ballots, with voter interviews) and use that as indirect evidence.
and yes ROUTERS… with traffic.
and any USB or extenal drives or wifi devices or IOT devices they might discover.
in order to pull off a very coordinated difficult to detect and attribute election vote exploit in all of the problem states (9?), one must assume it was accomplished with nation state Cyber capability.
as with stuxnet
I believe he said, ‘RAID’, rather than ‘ray’. Redundant Array of Inexpensive Discs. A file preservation technique.
I believe you are correct especially the note about “Mirrored” which is a duplicate and “Striped Drive” which stores pieces of data on 2 or more drives.
There are several different levels of RAID drive configurations involving 2 – 5 drives. One configuration is known as a shallow drive where 2 separate drives record the same data at the same time. But the other configurations can interleave the data onto more than one drive allowing for a robust redundancy. In order to delete a file all of the drives would have to delete it.
Walt has a better explanation below.
Yes. I used to occasionally finding myself doing things like his forensic examination, but not due to skullduggery but rather due to the creativity of people who should have known better. 😉
Intentionally misleading the public? Now why would they do that? /s
So instead of doing a multi-pass over write on the data drives and competently deleting more than just the file pointers, they did a half-a$$ cover-up and allowed the forensics professionals to recover the incriminating data.
Exactly correct. They were lazy, incompetent bums.
LOTS OF PEOPLE SHOULD GO TO PRISON… FOR A VERY LONG TIME.
you mean they were thieving Dems?
I think it was more a case of idiocy. They figured if THEY couldn’t find it (and when you search for a file after you delete it, the computer will tell you “file not found”) then of course NO ONE who wasn’t a member of the democratic aristocracy would have any chance of finding it either…
This makes it look like it was a non IT-literate administrator who tried to cover some tracks, rather than a tech-savvy, lower level number crunched.
Same person has thousands of files in their Recycle Bin or thousands of emails in their trash folder thinking everything is gone forever.
Can you imagine what is going on right now in other precincts around the country knowing this may be coming their way?
More felonies. Are Patriots on watch?
How long would a “multi-pass over write on the data drives” take? (Vs a half-a $$ cover-up)
About 6 hours.
TY, Me200.
Shouldn’t there be an offsite backup??
Ask ILLary.
DJT has all this data, that s why he was in the skif, just like the fbi leaking the russian sh1t about DJT to the newspapers DJT has to have a bonafide way to get the data into the mainstream that doesn t have him shouting it from the washington monument
I’ve wiped many drives at work using DBAN, Darik’s Boot and Nuke. It’s a program installed on removable media such as a CD or thumb drive. Boot it up, then choose the drive to wipe. It writes 1’s and 0’s over the drive to wipe any data. I assume BleachBit does something similar.
I believe the most secure method will do a pass 3 times over the drive to insure it is wiped.
Speed is determined by how fast the machine is, and how large the drive is. Some wipes have taken a few hours, others I let run overnight.
SSD drives are a different story. Many modern laptops have SSD drives, and the BIOS includes a data wipe feature. I don’t know how reliable it is or what standard is used for wiping SSD drives.
Of course, drilling holes through the drive also works.
YUP!
We are working with STUPID diamond thieves.
Ha Ha Ha – Funny that!
When I first heard this – I posted that some techo somewhere, was about to Akanicide themself!
I think when they look at the tabulation machines closer, they will find something like the following:
// start fraud here
int x = 1, y = 2;
// adjust fraud here
int biden_vote = x + y;
int trump_vote = y – x;
// output fraud here
cout << biden_vote;
cout << trump_vote;
// end fraud here go on to next vote – LOL
Who is coordinating the obvious voter fraud? Soros? Obama? I am still amazed that not one whistleblower to call these criminals out?
This is the one reason I’m not sure what really to trust anymore. It seems like by now there would be loose lips somewhere. The fact that there isn’t gives me huge pause I have to admit.
Agreed- exactly where are the loose lips, the frightened would be prison inmates? I can only assume it will be an avalanche when it starts. But, bear in the mind that those enforcement agencies who would be listening to these confessions have no interest in pursuing the content, so they end up threatening and thereby controlling the hapless confessor with threats which has the effect of simultaneously locking down whatever it is they have to say. Who knows how many people have come forward only to find the authorities had no interest (or worse), whether out of complicity or fear of making a fuss ?
imagine your children in a room wiht these perverts, what better way to threaten parents ….”home schooling” that way no kid goes missing for weeks
These folks drank the Kool Aide …This is their religion, their belief…Peter Strzok is a prime example..
Watch the videos showing the poll workers…the secretive intensity as if a burglar craking a safe…Pizza boxes covering the windows? AMERICA?
“not one whistleblower” — I would say this could be possible at this scale only if a fed entity was involved and all key players were its “trusted” employees immune to criminal charges. Just like what happened to those in FIB during PDJT’s 4 years – no whistleblowers and no criminal charges.
I will theorize that there have been a ton of whistleblowers but there is nowhere to whistleblow to. Every media organization and every civic group has been compromised. Gamergate of all things showed that. They had connected the SJWs to Saudi royalty and al-Qaeda within a year of digging. With that on top of the sex scandal on top of the charity fraud on top of the censorship of the whole Internet, still nobody would listen to them. Although it did get a few people to start talking about George Soros.
With all due respect, we have had Whistleblowerjis – who get run over w a Mac Truck.
1. Joe diGenova / Victoria Toesing WB – Obama Uranium sales. Risked his life, smeared as an untrustworthy alcoholic while he battles cancer.
2. IT Contractor – home raided & fired.
3. Another HRC WB ignored.
4. Muslim Jihad expert kept a hard drive around his neck, informed everyone he wasn’t suicidal. Allegedly committed suicide on the side of the highway in Sacramento?
5. WB / San Jose Mercury writer who exposed the CIA helping run drugs into South Central LA – 6 years later ‘committed suicide by shooting himself twice’.
6. Seth Rich.
7. San Jose Merc writer was told that others who attemoted to go down his investigative path – were threatened with death by the Deep State. (Movie: Kill the Messenger, now on Netflix.)
Likely more.
Many have quietly died.
Wonder if that goes for Gen. Patton in Germany , at the end of WW2 ,when he quietly crossed a road and was “accidentally ” killed by a truck.
The last half hour of Mike Lindell’s “Absolute Proof” showed a map of the USA voting machines communicating to IT address outside the country .
One of Lindell’s large monitors looked like Matthhew Brodrick’s WarGames movie with incoming missile strikes .
On another large monitor , when, where and how many votes were flipped to Biden displayed on a spreadsheet.
I think this information could only have come from a whistleblower.
During the movie he had his expert analyze data from 19 unique attacks into US counties….2895 counties were cyber-attacked on the night of 3 Nov…these 19 were in WI GA MI and PA IIRC and shifted over 500k votes from PDJT to Slo Joe….think if they went through ALL of the thousands of attacks how many votes were purloined
I doubt anyone in their employ wants to be Epsteined.
“I am still amazed that not one whistleblower. ……….”
Me also!
And ….people must have been bribed with some good amount of money to participate in the fraud.
California early release program…”We’re gonna set you free, but we have a little job for you to do for us
and we know you need the money” 73,000 released….
If memory serves me right, Zuckerberg “contributed” $300,000,000 to “Get Out to Vote” programs, coincidentally primarily in battleground blue state big cities.
Who, in the voting processes, in the big blue cities, is going to manage the spending of so much money? If Zuckerberg had anything to do with it, I’m SURE he/she was impartial!#!!$#!%! Who was on the payroll? How much were they paid? What did they do? I believe they’re called “operatives”. In big blue cities, who would set up and manage a strict ccounting system for every dollar spent?
Yeah right….nothing to see there….
Some states have passed laws forbidding “outside money” in their election processes. Good move.
You are incorrect. They have the whistleblower who has spilled ALL the beans. Dr. Franks sat across from him. He was on one of Mike Lindell’s ABSOLUTE DocuMovie series, except they blanked out his face. He does not want to go to jail.
I found out this AM that they also raided the international servers where traffic was found. I am looking for the video on that.
Thank you,
I had forgotten about the “blanked out his face” whistleblower.
We have the proof.
The whistleblowers would risk being Seth Riches or Sicknicked.
CCP
Waterboard
Non-lethal, very effective.
If you were a whistleblower, in this environment, who would
You talk to? The FBI? DOJ? GOP?
The smart play is to dive into a hole and drive a 20 year old car…
What about the hundreds? Thousands? Of depositions?
My knowledge of the computer sciences is rudimentary at best. This sounds all techie and everything, yet I have no clue what I just read.
It will be interesting to watch our CTH computer gurus parse this out.
Have at it folks. Can’t wait for the discussion. I learn a little more each time.
Thanks in advance.
I’m not an expert by any means, but basically the system has multiple hard drives set up in a way to avoid data loss. When they’re talking about RAID configurations, these are just different ways to use multiple hard drives to prevent data loss if one of the drives becomes damaged or corrupted. There is enough of the data on other drives to piece it back together, or in the case of a “mirrored” drive all of the data are duplicated onto 2 drives.
When the auditors start, they do not disturb the system. They copy the data from the system onto their own drives, taking great care to make sure no data can be changed on the original system. As they were then analyzing the copies they made (the “forensic images” are just complete copies of the system being studied), they found that databases were deleted. Even on a home computer without this RAID protection, when you delete a file it’s still there it’s just that it won’t show up in your files anymore until enough new data writes over it. In the counting machines, since they have the RAID protection, they are even more robust against files being deleted or corrupted, so the job of finding and recovering the databases was probably easier.
Either way, this auditor has 25 years of forensic computer analysis, so I imagine this was not a challenge for him.
I did Computer Forensics in a sh!thole country for a year. They mainly use a program called Encase to make an exact bit by bit copy of hard drives (bit stream image), the process has a write blocker in place so as to not add anything to the HD. Once they have an EXACT replication of the HD that is when they can start a “carve” process and recover deleted files.
When a normal PC user deletes a file, the file isn’t actually deleted, it’s still there on the Drive, but the space it resides on is available for new data to be added to that space. So if a file was deleted & not wiped with the right tools and the system was shut off & not used for a few months, the file is actually complete & still there.
the file in question was reportedly deleted a mere 10 days before they turned the electronics over to Cyber Ninja
And if true, which it probably is, how does that happen. At that point how is anything touched, moved or deleted and who did it!
it was MAGIC….especially when you consider the MCBoS claim that they do not have the passwords…how did they open the computers up after hitting the START button?
Personally, I would not be surprised to wake up to the news that there was a fire, or the sprinkler system went off, or an unidentified band of thugs invaded the forum where the audit is being carried out and the machines and data ruined. I think the scum are that desperate and they certainly have not been adverse to using totalitarian tactics.
The more the Bad Guys resist the more guilty they become to a layman as Me. Why would anyone object to an audit which declares your innocence? In fact an innocent would encourage an audit removing any doubt as to suspicion.
There definitely will be some physical destruction. They will judge that it’s better to be considered or assumed to be a cheat than to be proven to be one.
The Ruling Class stole an election right in front of us. However, they do need to keep the Big Lie going by not having the hard evidence of their theft out in the public domain.
I think the election thieves will put out all the stops to prevent AZ and any other state from producing verifiable, documented hard evidence of election fraud–particularly if that fraud is on a scale that would have flipped the state to Trump.
Those who are guarding the place during the night are probably being offered HUGE caches of money to look away, but are they? It will take only one small miss-step to take the whole audit down, right?
I wouldn’t be surprised if Hussein ordered the woke military to launch a hell fire missile from a drone onto the coliseum. Final disposition matrix redux.
Agree. That is why VSG Trump told the guv to deploy the AZNG. Desperate people do desperate things.
Whoever deleted the files was a nitwit. When you delete a file, the Windows OS replaces the first character of the file name with a theta character. Replace the theta with any ASCII character. Voila! You get your file back. This dope didn’t know enough to perform a file wipe, which makes data non recoverable.
They’re not ILLary, for sure.
The absolutely ridiculous amateur attempted deletion of the database screams ‘non techie’. That means look at the folks who had access but have no technical skills. In a lot of areas of the country, it’ll be some politician’s high school kid, cousin, nephew, who’s given a job because of who they’re related to.. and given a ‘technical’ title so they can give them a wage well above what a non connected person would get.
Images of Hillary with her ‘What, wipe it with a cloth?” statement comes to mind! Good times.
“In the course of performing that discovery I found that an MFT that clearly indicated that the data base directory was deleted from that server.”
The time and date when the directory was deleted should be very useful.
Who deleted the directory and why?
pass the popcorn.
Leik: A Windows (NTFS) formatted drive has a Master File Table (MFT) at the beginning and a duplicate copy at the end of the drive. It stores the index of all files written to the drive.
An NTFS drive also has a SAM file (Security Account Manager). The SAM file logs the identity of whoever logged in and modified any file on the drive. Could be stolen identity credentials. But. To login, someone had to have login credentials and the SAM file logged that login and timestamped it. The combination of the MFT and SAM files will pinpoint the ID of whoever’s credentials were used to delete the database. Might be very interesting.
it also requires “Administrator Privileges”….not just anyone can log in and modify or delete files on most government/commercial systems
Quang in Shanghai?
No. I think Quang was involved in the OPM data hack. May have been his brother Quoc.
thank you ,
I tried to load my popcorn-eating antelope GIF here, but couldn’t get it to work.
Pray for their protection. Possession of truth is dangerous.
Deleted? Like with a cloth?
Ironically in this instance “like with a cloth” would be slightly more defensible. It would at least be indicative of total unawareness. This was just ham-handed.
I surprised the morons didn’t use ball peen hammers for those hard to clean hard drives.
When you delete files and folders you’re actually only deleting their reference points in the directory. The files and folders are still there, they just don’t show up in the directory. Eventually they will be written over by subsequent files and folders as they are saved. The only way to completely remove the deleted files is to wipe it clean, like with a cloth… or something like BleachBit.
Yeah, I made this point on Gab a few weeks back. Not many people outside of IT know that it is all but impossible to delete a file. Literally it is either physically destroy the hard drive, or a process of overwriting that can take weeks.
This is correct. A secure deletion of data from an HDD takes multiple passes of overwrites, and potentially many hours of time, depending on the file sizes. Military-grade deletion usually even involves the physical destruction of the internal platters themselves.
It is even more involved to securely delete data when SSDs or RAID arrays are involved.
A single keystroke ‘erasure’ merely deletes the MFT references, which the OS relies on. All the data is still there on the storage drive. A competent forensic examiner can usually locate the deindexed and orphaned data quickly. Standardized recovery software has been available to the consumer sector for many decades for this purpose, and for recovery of data from otherwise corrupted drives.
Most operating systems also maintain many hidden logs of system events which can identify in great detail when, how and often who executed such attempted deletion operations. Other markers will exist at the code level as well. Unless the perpetrator has very sophisticated code-level tools (generally only a state actor), it is impossible to not leave footprints and digital fingerprints for every intrusion and system command.
The attempted destruction of data is often additional evidence of culpability in criminal investigations. Fortunately, most criminals are not very sophisticated about these matters, and are usually caught. Covering up computer crimes is very hard to pull off.
Covering up computer crimes is very hard to pull off.
It helps if one’s allies own the judicial system. Hello Hillary.
All this really turns on that one reality. Anyone who’s watched how the judicial system handles the Communist mercenaries has seen the blueprint, and that’s obvious, in your face stuff, not the arcane science of computers.
Remember when ENIAC predicted Ike would win by a landslide and no one believed it? Heh, the young CIA surely took notice of that. And here we are.
What most people don’t understand is that when you delete a file on your hard drive, the actual file is not deleted, only the directory locator is deleted. It looks as if it is gone, but until future data actually overwrites the file data, the original file data is still there.
This is how forensic analysis recovers mucho info in criminal investigations.
This is a simplistic explanation, but suffice to say, the only way they could really guarantee that the data was gone would be to reformat the drive…in which case it would have been blank…everything gone…
That would be obstruction of justice…straight up.
Peace brothers…
Beware of the magnets
Assuming magnetic, even a reformat wouldn’t do it. That’s why DoD went to the three pass system decades ago then updated it to seven. If you don’t change the data sufficiently, you can (granted you need clean room lab conditions with very expensive equipment) read the edges of the tracks to recreate the data.
If you want to make the data GO AWAY there is really only one solution: Grinders that chew the drive into confetti. Degaussers are a close second, but still second.
I set fire to a couple of hard drives. BBQ lighter fluid and burn, baby, burn.
How’d it taste?
Correct answer: like chicken, of course.
“…they reference the auditors ability to recover the deleted information as proof the voter data was never deleted.
Masters of doublespeak.
Semantics. Word Salad. Someone TRIED to delete it but they weren’t that smart. So the file was hidden ready to be overwritten except they weren’t using it so it didn’t go bye bye.
It’s like someone above said. It was lost and now it was found. Does not negate the fact that SOMEONE did TRY to intentionally delete it. Now they are caught.
I found that an MFT that clearly indicated that the database directory was deleted from that server. All of this may be moot because subsequently I have been able to recover all the deleted files and I have access to that data.”
One of the last things done on this server was to delete the directory before being powered off. Otherwise, there is a high likelihood that these files could have been overwritten by the OS, preventing recovery under normal use.
This suggests that the directory deletion and the files it contained was pre-planned?
I agree. Whether RAID is striped or mirrored, eventually the good data will be over-written with the bad. Doesn’t mean it can’t be retrieved through forensics, but my guess is it makes their job easier. Plus proof of no tampering by the good guys. Would you agree Snoopy?
Yes, on all statements. I find it interesting that no backup of the server has been referenced. As you know, RAIDs are useful, but backups are mandatory.
I was also working on the estimated size of Dr Frank’s hidden database. The 200,000 voters could be 20M in size. But, I don’t have enough information to know for sure.
I know that I had a BDR with Shadow Protect for these issues when I was still working. (miss it too!) I wondered the same thing about who managed the backups for these servers or did they even bother. I wondered if the backups were requested for the audit, although it does seem a moot point now (maybe). Glad they have folks smarter than me doing this! 😉
You’re just being modest. It never goes away, only the technology changes.
Thanks! 😉
Hide the Crime.
CrimeS.
People who have nothing to hide, hide nothing.
I think it’s fair to say the Maricopa County BoS has a LOT to hide.
Hmm……
My limited experience with computers taught me this:
When you “delete” something from a drive, you’re not really deleting the data, itself. What you’re doing is deleting the “filename(s)” from the directory.
So, the next time someone enters a command to “find XYX” the operating system can no longer LOCATE “XYZ” because it’s not longer listed in the directory, even though the data still exists on the drive, itself. You’ll get an error message like “File not Found” or something similar.
Here’s the funny thing: ANYONE with any “ability” KNOWS THIS, but the Maricopa idiots are the ones who tried to do it, and then claim that the AUDITORS were the clueless ones! LOL
Bad transcript. While it is true that graphics cards calculate rays, you don’t find them in drive configurations. There you find either arrays or RAIDs (Redundant Array of Individual Disks). Given the first reference indicates a 1+0, I assume the actual word is RAID. A 1+0 configuration is a pair of striped drives (increases speed) which is then mirrored (perfect backup of the data).
Here is the smoking gun: In the course of performing that discovery I found that an MFT that clearly indicated that the data base directory was deleted from that server.
MFT is Master File Table. Most systems actually have two in case one becomes corrupted, but either way it is the track that tells the computer where the other tracks are. If it marks the file as deleted, as far as the computer is concerned when it is turned on the file is gone. Drive recovery software depends on the fact that most drives don’t actually physically delete the data, they just mark it as deleted and the disk space becomes available for new files to be written to it. If the deletion was recent, it may have been a fairly simple and straight forward process to recover it. But recovery =/= not deleted. At least not in this context. Maybe in CIA/NSA/DOD seven pass wipe terms it wasn’t deleted, but in ordinary parlance it was deleted.
Apologies for geeking out.
Thank you and other knowledgeable Treepers for clear explanations
Remember when Kamala Harris was jogging in the park and called Joe Biden congratulate him/themselves for supposedly winning the Presidency….It was so fake and unrealistic it was laughable….Kamala’s whole demeanor screamed ‘Scam’…It was so obvious I’m even embarrassed to bring it up…..It’s apparent fraud has been running rampant in our elections for decades…..Nothing surprises me anymore…..Just enjoy your life as best as you can….I’m going fishing tomorrow and not thinking about this corrupt, crap….
To me, this makes a pretty good case for intent to destroy evidence? And, a reason to prosecute.
Certainly but who is going to prosecute and what judge will hear it?
Sorry to be a wet blanket but the available data do not support a positive outcome. *
*What we would consider a positive outcome.
Who is going to prosecute, and what judge will hear it?
So, I guess, I have to go with a grand jury.
Unless you let me have a judge, who recently said, prove that they duplicated the ballots and I will force them to recall the electors in Georgia? This, of course, will never happen.
“All of this may be moot because subsequently I have been able to recover all the deleted files and I have access to that data.”
Praying that this sentence kept a whole lot of people awake all last week scrambling to figure out EXACTLY what was recovered and EXACTLY who is now implicated in whatever those files contained!!
You can bet the guilty are not having, “Good days”. It has to be a nightmare for them. GITMO has to enter their mind. I don’t think this will get it, “I haven’t done anything that hasn’t been the way it has been done in the past years and years”.
I would like to know more about the recovered database. Does it contain the hidden database of 200,000 voters identified by Dr Frank? As you recall, Dr Frank said they were hidden intentionally!
The official response was that “We never deleted any such file, and their discovery of it PROVES we didn’t. They are just so inept that it took them a while to FIND it!”
This strategy also partially explains why Maricopa didn’t want to participate in the first place. They didn’t want to be exposed to questions they didn’t want to answer publicly in REAL TIME.
We never deleted any such directory and I would say where are your multiple backups for the drive in question and of course the log files.
And, wait for them to say, we never backed up the drives which would contain the log files. In short, their date and time of deletion of the directory in question.
Then everyone in the IT world would know, they are lying.
Then bring out the recovered and unreferenced log files. I would bet the log files have been recovered.
I bet you are correct Snoopy. The Audit tech only said what was absolutely necessary.
I am sure he has a lot more to say. I am sure this has went to a criminal level now.
This!
MFT says a delete function was used.
The machines had already had a lawful subpoena on them. Someone went in and deleted said file then shut the machine down.
That is why the forensic auditors did not power up machines as much as I get from the steps they go thru.
They made an image copy of all hard drives.
Someone logged into that machine and deleted that file and they were not IT savvy either. Now the persons ID is there most likely that logged in on the machine.
This is a very serious offense.
Bingo! Can you say corrupt? Yeah, I knew you could 🙂
unintelligible = Mirrored (both drives are a duplicate of each other)
Replace ray with “array”.
The gentleman’s description is all about Redundant Array of Independent Disks or Redundant Array of Inexpensive Disks (RAID) technology.
The one plus zero is a RAID configuration.
I commented about the same. I almost stroked out when I read a ray and ray. Probably an automatic transcription issue but c’mon. This actually got released as an article. Unreal.
Such boneheaded actions, bordering on negligence to the point of absurdity.
Much of this is simply too obvious to be mere incompetence in regards to somewhat common IT knowledge in industry.
Just thinking that these are only the things that we are finding out about (for now).
Cue the suspicious cat.
The MCBoS propaganda is clearly garbage. Someone with administrator access to the EMS primary computer deleted the database directory, just before the computer was shut down for transport to the auditors.
That “someone” is unlikely to be a Dominion employee, because the actual “deleated” files weren’t professionally overwritten with random data. So that means county officials had administrator passwords for at least the EMS primary computer.
So the question is why the MCBoS wanted to prevent the auditors accessing those database files. What were they trying to hide?
Number of ballots sent to “adudication” and the speed of adjudication?
A sudden surge of Biden only votes, with no down ticket picks?
A mysterious tail end to counting where every batch maintains a constant Biden/Trump ratio after Biden takes the lead?
I would say you a sound theory in the works
Have a sound theory.
Sorry about that
At a minimum, it shows someone other than Dominion had Administrative access to delete a database.
It’s ARRAY. Not A RAY, Not RAY, it’s ARRAY.
I want say thank you to all the computer professionals that have posted their knowledge on the hard drives and files. My understanding has drastically improved.
This why I love the Treehouse. The wealth of knowledge and backgrounds is unbeatable.
Again thanks everyone for explaining these confounded machines to us notepad and pencil generations
Just remember that us computer folk are also used to getting away with talking BS jibberish, since nobody knows what we’re talking about anyway. Most people we work with just want their computer or monitor to work again, or for us to ask if they tried new batteries in that mouse that isn’t working. 😉
Hey, you are describing me.
Thanks for the laugh. I am guilty as you describe
2020 election was Totally Rigged therefore we have a fake president in W/House Right now and doing everything Bad for country,
Interesting story.
Tells me the Board of Supervisors were supported by the B-Team and did not have help from Micro-Soft, if their contractors did not know enough to go through every nook and cranny to clean the databases off the machines. I hope every state even contemplating an audit gets their hands on their State’s machines. Plus, in the future tight PHYSICAL and DIGITAL controls are put in place.
The UNI-PARTY and Puppet Masters will not repeat this mistake.
Even if these audits provide the physical proof of large scale cheating, the only thing that will force Biden to step down is a general strike on the part of the majority of the US population.
The left doesn’t care that it commits crimes. That includes the left sitting on the Supreme Court. The RINOs in the congress will also lack any spine to do something even if they are drowning in letters from their constituents to act.
On the other hand, any RINO trying to protect the current ballot counting procedures and bureaucracy will be totally stripped of any pretense that they are not active agents of the left. This at least provides some hope that the next elections might actually correspond to reality.
Independents are not all low info. Like conservatives, they have largely concluded that the media is a propaganda organ of the left. And unlike the left, most of them should be disgusted by the revelations produced by these audits. All they need is a sign that a real opposition movement with firm resolve exists as an alternative.
As always, it does not matter what proof of corruption exists.
Throughout history, kinetic military force has been required to overthrow systemic evil and corruption. What else overcomes a corrupt judiciary?
When right and wrong are lost in the culture and every decent impulse is compromised by wickedness, might DOES settle the point.
Throughout world history, who controls the military controls the nation.
America will be forced to endure whatever kind of government the military supports. If the United States military supports the rotten imposition of a fraud leader elected by massive cheating, that is our future.
BTW, in the statement, the word “ray” used in several places is almost certainly “RAID” which stands for Redundant Array of Independent Drives. This gets geeky, but it’s a method of having data backed up constantly even if a physical drive fails. The forensic ninjas know all about this and apparently were able to recover data that SOMEONE attempted to delete. Most excellent. That is what they’re paid for. This is cause for optimism. Stay tuned, freedom lovers.
STOLEN ELECTION WILL BE PROVEN
when the text says the disks were in a (ray) configuration it should be [RAID] (redundant array of independent disks).
Nope. See Hasty Hayseed’s lucid explanation above.
Democrats and their media wing (sometimes correctly referred to as the Fake News) are using Alinsky plays left and lefter!
They keep lefting, they will run smack into themselves.
It’s so bad now that you can literaly tell what they are doing by what they accuse others of doing.
I’m an IT pro with 30+ yrs. including some forensics background. Only two comments.
1. Ray = RAID. Fancy way of using multiple drives so they look like one to the operating system (OS).
2. Every fact and description is technically correct. Obviously I have no idea if the system conditions were as testified, but I will say 100% likely true. Why? He clearly knows IT forensics protocols and would use standard programs to analyze the systems. Those tools record everything with chain of custody and evidence protocols sufficient to stand up in court.
When you delete a file in the user programs, you delete a pointer to the file on the disk and the OS marks the sectors as available. NO DATA IS ACTUALLY DELETED.
To make the data unreadable, you have to use software that overwrites the data, say with all ones then all zero’s. And to defeat the best forensics tools, you have to make many passes. And even then, you probably should pull out the hammer or your mostest/hugest magnet (or both).
The delete actions seem to have been done by rookies or careless folks.
Only rookies or carelessness?
There is another possibility I can concieve of.
What if these particular things were intended to be found?
Well just think about it. What better way to bury more serious offense(s) then to use less subtle or criminal ones to serve as combination chaff, countermeasures and outright deflection?
I would not consider it implausible. We know that many of them are evil and cunning enough to be capable of such.
One thing is certain, there is much more to this sordid tale to be discovered.
Live feed shows the audit really rocking today….busy bees!
I heard a report they have 2 x the personnel on the ground now to speed things up
I just saw this Movie “Meet John Doe” (1941).
The parallel with what we are now seeing in the media is astounding.
https://archive.org/details/meet_john_doe
I am reminded of the phrase ” buying ink by the barrel “.
Hearst Media of Patty Hearst fame or infamy.
Media can make up anything.
data partitions (and unique physical and logical drives) are routinely deleted/wiped.
so the question really isn’t about whether something was deleted or not.
the question becomes..
what was the data that was deleted and of what consequence does that deletion have to the legitimacy authenticity accuracy of the machine.
in order to satisfy that question more investigative facts must be established.
a. when did the deletion occur? timeline
b. by whom under what authority and for what reasons?
c. if the data was important, was there a backup of that data to preserve it or to merge it into another volume?
d. what does the deleted data contain? votes? code? archives? manuals? call and contact directories? etc… again, what is the composition of the data and of what significance does it have to any aspect of irregularity toward any known other problem?
it’s important for this team to establish it’s professional chops in performing this forensic exam. no doubt, this discovery means the team is highly qualified to perform a carefully controlled forensic exam
but at this point, without knowing to what extent the deleted data has on the election process, we must remain patient and not extrapolate automatically this actually means anything other than it’s simple explanation.
anecdote: in order to furnish pristine hard drive,volume, MFT conditions to satisfy pre testing certifications, it is COMMON practice to delete and wipe physical and logical drives. this is a common practice well established for a variety of applications where high availabity and zero fault tolerance are required to be tested…simply:. you start from scratch and then test the drives for faults, bad sectors, etc…then you load test data and evaluate…once that is complete satisfactory, you again wipe test data and applications and load production data.
I present this example not to suggest this explains precisely what is the reason. for this deletion, but to explain. there are many potential very plausible real-world cases where deletion and wiping aren’t just common, but required.
I’ll wait to form an opinion about what this deletion means when the forensic team describes it in detail.
God Bless America
The auditors already explained that the directory the county tried to delete was the database directory for the 2020 election on the EMS primary machine. This deletion occurred while the machine and that data was subject to subpoena.
There is only one plausible explanation for this: someone wanted to prevent the vote tally data being cross checked against the physical ballots, and they were prepared to commit a crime to this end.
I would like to read the official technical forensic log captures of that deletion operation.
I understand what is “being said”. I have technical reasons to doubt what is “being said” is everything there is to know about the details.
it is very plausible that such a deletion was performed to frustrate the audit matching exams.
that seems very amateurish to be clear.
I’ll wait to read a technical report.
anyone have that?
please provide a link
TY
The Democrats and their Rino pals want to wear the public out with trivial discussion. Setting the record straight has merit, but it also plays into their hands. The media has its thumb on the scales. I’d prefer the audit group focus on completing the investigation, then presenting their findings carefully. Do your talking in court while having the BoS jailed for failing to follow the subpoena.
Pro Tip Never let a Social Worker be a Computer Crrime Boss
A few weeks ago over 300 million lottery tickets were sold in 4 days.
Within hours of the drawing, lottery officials knew how many winning tickets were sold and where the winning tickets
were sold; down to the specific store locations.
4 days after voting has closed, some voting officials don’t know how many people voted, how they voted, who they voted
for, or what the accurate results are.
The US election system is BROKEN ON PURPOSE.
*forwarded from @RealGenFlynn
All by design.
Phoenix was still counting ballots a WEEK later when they had supposedly already reported on 99% on election night…..so 99% in ONE night and 1% takes over a week…how does this compute?
And there you have it.
I ask again…….
Is there a way an individual AZ voter can ask to see how the AZ machines captured their own vote?
For example, Did John Smith’s vote get “COUNTED” as a vote for R or D in the Presidential election back in Nov.
Imagine the incredible outrage if in this example, John Smith who is a life long R and knows he actually voted for PT but his vote was recorded as a vote count for Biden.
Now imagine if thousands upon thousands of people in AZ learn that their actual vote and thus count was changed.
This IMO would cascade almost immediately across all 50 states as the outrage builds to the point where the people demand justice.
IMO the Supreme Court would have to hear this case.
Show the names for anyone who opts in and approves this public showing and how their vote was ACTUALLY RECORDED.
IMO this really shouldn’t be that hard to produce. And once this specific “truth” snowball starts, there is no way to stop it.
Simple answer is no. Because recording that information would prevent voter anonymity. This is why for absentee ballots, the ballot envelopes must be separated from the ballots.
But it is possible to check if a person is listed as having voted, just not who they voted for. And this alone would be very revealing. A lot of republicans who voted absentee would find no vote registered in their name. And a good number of persons with a record of rarely voting, who didn’t personally vote in 2020 will find that someone voted in their name.
that’s not how I would do a vote fraud.
at all.
sure, one “could” do it by swapping votes with many kinds of ballot stuffing..
but that’s not how I would do it.
considering a successful operation must accomplish the mission in at least 9 states, each with quite disparate and uniquely controlled rules, people and audits, a few rules would guide a successful cute fraud op
1. attribution cannot be achieved with forensic exams of machines
2. vote ballots and virtual images must maintain reasonableness…
3. laws and rules must be exploited that prevent external audits of actual voters and their signatures
4. closed wall proprietary code by privately held legally protected companies prevents external exam of firmware, records, live data backups, and EXTERNAL command and control servers
5. contingencies for fail safe measures should the ghosts in the machine either fail to accomplish the successful path, or in the case when the ghosts in the machine are rendering effects that would alert observers.
It may work out that forensically examining drives and machines will reveal some hidden features.
however, I am not convinced anything less than a complete and thorough examination of every single known and unknown factor of the infrastructure will produce the truth.
there are similarities we can draw from this to the fisa court.
it’s pretty much a protected and we’ll concealed wall of secrecy.
with all the investigations engaged, ultimately it’s led to no changes in that secret police court.
we KNOW it’s fraudulent, but what will cause it to change?
that needs to be on everyone’s heart and mind.
if this fraud is indeed the work of massively resourced coordinated conspiracy, finding the fraud is only the first step.
if it’s not the work of massively resourced coordinated conspiracy, we are dealing with unique state issues of corruption.
I’m not sure which of these two poses a greater concern… they would appear to me as equally challenging to correct.
thus, it’s imperative we simplify and make transparent the election and vote laws in each and every state. removing the mail in seems obvious.
automatic pre production testing and audits of machines and also live audits during and then post election audits before certification.
basically, the task seems to me:. remove every possible loophole that can be exploited.
It’s idiotic to let people cheat in an election. A fair election is what balances all our individual interests; you talk about ripping the fabric of society ?
Liars & Cheats never stop till they’re forced back in their holes.
You can delete a file and recover it, a database, a directory, etc. and recover it. MC’s logic is the same as saying if you find your wallet you never lost it. Dopes.