Years of agonizing and frustrating reviews and analysis of the Trump administration activity in real-time are reconciling today. During Senate testimony today before the Armed Services Committee, Joint Chiefs of Staff Chairman, General Mark Milley, clarified some very painful issues to accept. President Trump was being heavily managed by operatives of the Senior Executive Service (SES), and his inner circle was willfully participating.
What follows is in no way a defense of Milley, quite the contrary, Milley is a brutally political, manipulative, entitled and arrogant member of the United States armed forces. His delusions of grandiosity represent the worst of our nation and can only be topped by one other, Anthony Fauci.

Earlier today, Milley was attempting to flex his power in the almost identical way we saw former FBI Director James Comey pull the same angle. You might remember, during congressional testimony in March 2017 when Comey was questioned about why he never informed congressional ‘gang-of-eight’ oversight about the preceding eleven month FBI investigating the incoming President, Donald Trump. Director Comey pontificated, obfuscated, dodged carefully, and then deflected responsibility by saying he informed the “national security council” under President Obama.
When General Milley attempted to justify his unilateral contacts with Chinese military officials, he made a similar, and remarkably telling, admission and deflection.
For the January 8th phone call with General Lee of China, Milley stated he informed President Trump’s Chief-of-Staff Mark Meadows and Secretary of State Mike Pompeo. Keep in mind that Kash Patel has publicly stated General Milley did not inform Acting Defense Secretary Chris Miller directly; at least to his knowledge. So, Milley’s secondary point about notifying Christopher Miller in January 2020 needs to be reconciled carefully.
Listen carefully to how Milley is describing those calls. Specifically, pay attention to Milley saying the calls were initiated by him in response to “concerning intelligence, which caused us to believe the Chinese were worried about an attack on them by the United States.” It is important to note what this is NOT.

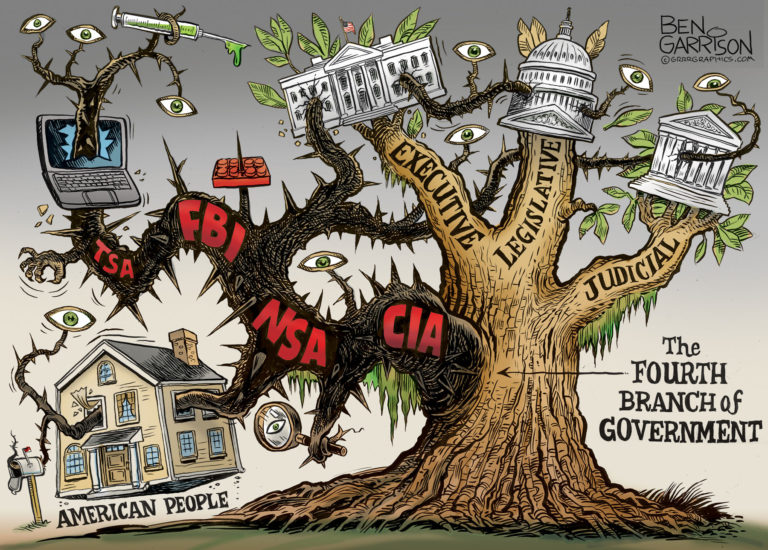
 Today, the biggest names in Big Tech announce they have partnered with the Five Eyes intelligence network, ultimately controlled by the NSA, to: (1) monitor all activity in their platforms; (2) identify extremist content; (3) look for expressions of Domestic Violent Extremism (DVE); and then, (4) put the content details into a database where the Five Eyes intelligence agencies (U.K., U.S., Australia, Canada, New Zealand) can access it.
Today, the biggest names in Big Tech announce they have partnered with the Five Eyes intelligence network, ultimately controlled by the NSA, to: (1) monitor all activity in their platforms; (2) identify extremist content; (3) look for expressions of Domestic Violent Extremism (DVE); and then, (4) put the content details into a database where the Five Eyes intelligence agencies (U.K., U.S., Australia, Canada, New Zealand) can access it.