During my trip to DC in the summer of 2020 there were a myriad of disconcerting datapoints assembled; revelations that made sense of the madness and disappointments found everywhere. However, one of the key notations for future reference was to watch the political evolution of Dept of Homeland Security (DHS) and spot the jump where the ideological outlook turns into specific government action.
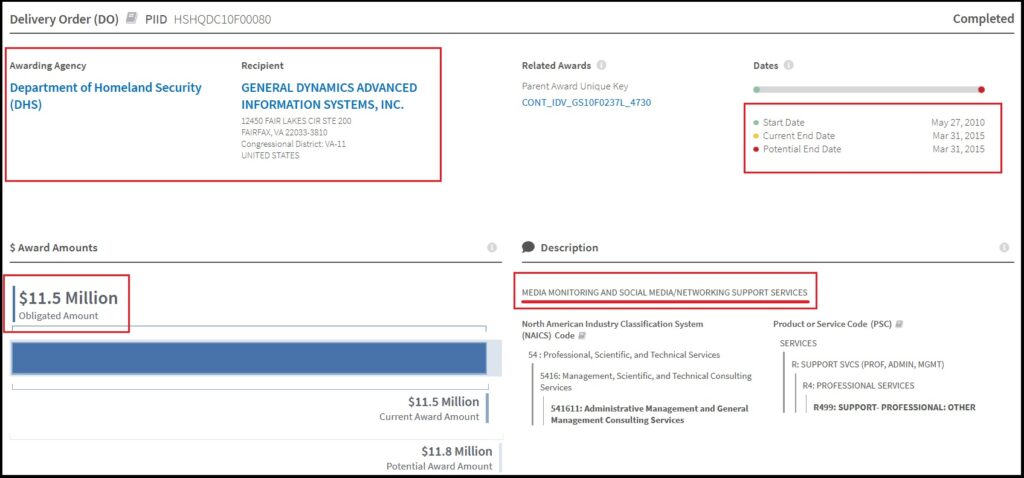
With that in mind, this recent discovery of a 2010 to 2015 DHS contract to a very well-known USG defense contractor, General Dynamics Advanced Information Systems Inc., surfaces.
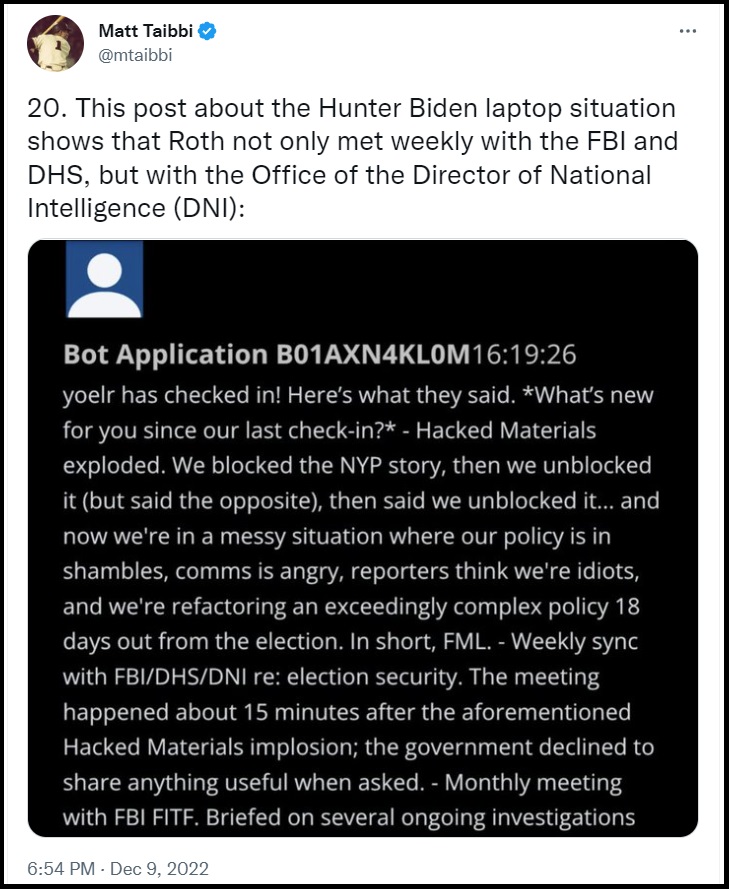
As many are now becoming aware, DHS is the lead agency behind all of the engagements with Twitter and other social media.
The Office of the Director of National Intelligence (ODNI), specifically created as an outcome of the post-911 Patriot Act, is the pivot point on the surveillance radar sweep.
Prior to the DNI the general Intelligence Community (IC) surveillance faced offshore and swept foreign adversaries. If any threat was picked up that included the potential for domestic terrorism, the identified contact transferred from the CIA, NSA, DoD into the DOJ and FBI. The DOJ then used the FISA Court to request transfer of targeting from foreign to domestic.
However, after 911 it was determined the national security surveillance radar needed to sweep a full 360° to include domestic surveillance. The ODNI was the office created to manage the pivot point. As a specific outcome of the Patriot Act, American citizens were now under the same surveillance as foreign adversaries. The new definition of American citizens being threats to the national security state is ultimately what led to our taking off shoes at TSA checkpoints in airports. TSA is a subsidiary agency of DHS.
Offshore surveillance now flowed from the CIA, DoD, NSA, IC into the ODNI, who then filtered it, and if needed transferred it to the newly created DHS.
As the design was laid out, the DHS would then contact the DOJ or FBI while affording the U.S. person (target) in question their duly constitutional protections against unlawful searches and seizures. The sketchy legal dynamic is what created the need for the DOJ National Security Division (DOJ-NSD).
At the same time, onshore domestic surveillance would be conducted by DHS through new systems like the Transportation Safety Administration etc. Local, state and federal law enforcement would identify issues or investigative targets, then send the targeting data upstream into the DHS database. DHS transfers the finding to the ODNI who cross-reference it with CIA, NSA, etc. This was the original design.
However, it was specifically Barack Obama and Eric Holder who saw an opportunity with the newly created system. The result, DHS domestic surveillance was weaponized. The timing of this DHS contract (2010) to General Dynamics for “media monitoring and social media support” fits perfectly in line with the known timeline of how DHS was weaponized.

Barack Obama and Eric Holder did not create a weaponized DOJ and FBI; the institutions were already weaponized by the Patriot Act. What Obama and Holder did was take the preexisting system and retool it, so the weapons of government only targeted one side of the political continuum.
This point is where many people understandably get confused.
Elevator Speech:
(1) The Patriot Act turned the intel surveillance radar from foreign searches for terrorists to domestic searches for terrorists.
(2) Obama/Biden then redefined what is a “terrorist” to include their political opposition.
DEEP DIVE:
Twitter is to the U.S. government as TikTok is to China. The overarching dynamic is the need to control public perceptions and opinions.
DHS has been in ever increasing control of Twitter since the public-private partnership was formed in 2011/2012. However, it’s not just Twitter. The same fundamental relationships are now at work within Google, Microsoft, YouTube, Instagram and Facebook.
With all the shiny things surfacing from the Twitter Files, few are looking at the origin of what the government is trying to keep hidden….
 In the era shortly after 9/11 the DC national security apparatus, instructed by Vice President Dick Cheney, was constructed to preserve continuity of government and simultaneously view all Americans as potential threats. The Department of Homeland Security (DHS) and the Office of the Director of National Intelligence (ODNI) were created specifically for this purpose.
In the era shortly after 9/11 the DC national security apparatus, instructed by Vice President Dick Cheney, was constructed to preserve continuity of government and simultaneously view all Americans as potential threats. The Department of Homeland Security (DHS) and the Office of the Director of National Intelligence (ODNI) were created specifically for this purpose.
After 9/11/01 the electronic surveillance system that was originally created to monitor threats from abroad was retooled to monitor threats inside our country. That is when all of our electronic ‘metadata’ came under federal surveillance.
That inflection point, and the process that followed, was exactly what Edward Snowden tried to point out.
What Barack Obama and Eric Holder did with that new construct was refine the internal targeting mechanisms so that only their political opposition became the target of this new national security system.
The problems we face now as a country are directly an outcome of two very distinct points that were merged by Barack Obama. (1) The post 9/11 monitoring of electronic communication of American citizens; and (2) Obama’s team creating a fine-tuning knob that it focused on the politics of the targets. This is very important to understand as you dig deeper into this research outline.
Washington DC created the modern national security apparatus immediately and hurriedly after 9/11/01. The Department of Homeland Security came along in 2002, and within the Intelligence Reform and Terrorism Prevention Act of 2004 the Office of the Director of National Intelligence (ODNI) was formed.
When President Barack Obama and Attorney General Eric Holder arrived a few years later, those newly formed institutions were viewed as opportunities to create a very specific national security apparatus that would focus almost exclusively against their political opposition.
The preexisting Federal Bureau of Investigation (FBI) and Dept of Justice (DOJ) were then repurposed to become two of the four pillars of the domestic national security apparatus: a domestic surveillance state. However, this new construct would have a targeting mechanism based on political ideology.
The DHS, ODNI, DOJ and FBI became the four pillars of this new institution. Atop these pillars is where you will find the Fourth Branch of Government.
We were not sleeping when this happened, we were wide awake. However, we were stunningly distracted by the economic collapse that was taking place in 2006 and 2007 when the engineers behind Obama started to assemble the design. By the time Obama took office in 2009, we sensed something profound was shifting, but we can only see exactly what shifted in the aftermath. The four pillars were put into place, and a new Fourth Branch of Government was quietly created.
As time passed, and the system operators became familiar with their new tools, technology allowed the tentacles of the system to reach out and touch us. That is when we first started to notice that something very disconcerting was happening. Those four pillars are the root of it, and if we take the time to understand how the Fourth Branch originated, questions about this current state of perpetual angst will start to make sense.
We pick up the expansive and weaponized intelligence system as it manifests after 9/11/01, and my goal is to highlight how the modern version of the total intelligence apparatus has metastasized into a Fourth Branch of Government. It is this superseding branch that now touches and influences every facet of our life. We The People are under surveillance.
If we take the modern construct, originating at the speed of technological change, we can also see how the oversight or “check/balance” in our system of government became functionally obsolescent.
After many years of granular research about the intelligence apparatus inside our government, in the summer of 2020 I visited Washington DC to ask specific questions. My goal was to go where the influence agents within government actually operate, and to discover the people deep inside the institutions no one elected, and few people pay attention to.

It was during this process when I discovered how information is purposefully put into containment silos; essentially a formal process to block the flow of information between agencies and between the original branches. While frustrating to discover, the silo effect was important because understanding the communication between networks leads to our ability to reconcile conflict between what we perceive and what’s actually taking place.
After days of research and meetings in DC during 2020; amid a town that was serendipitously shut down due to COVID-19; I found a letter slid under the door of my room in a nearly empty hotel with an introduction of sorts. The subsequent discussions were perhaps the most important. After many hours of specific questions and answers on specific examples, I realized why our nation is in this mess. That is when I discovered the fourth and superseding branch of government, the Intelligence Branch.
I am going to explain how the Intelligence Branch works: (1) to control every other branch of government; (2) how it functions as an entirely independent branch of government with no oversight; (3) how and why it was created to be independent from oversight; (4) what is the current mission of the IC Branch, and most importantly (5) who operates it.
The Intelligence Branch is an independent functioning branch of government, it is no longer a subsidiary set of agencies within the Executive Branch as most would think. To understand the Intelligence Branch, we need to drop the elementary school civics class lessons about three coequal branches of government and replace that outlook with the modern system that created itself.
The Intelligence Branch functions much like the State Dept, through a unique set of public-private partnerships that support it. Big Tech industry collaboration with intelligence operatives is part of that functioning, almost like an NGO. However, the process is much more important than most think. In this problematic perspective of a corrupt system of government, the process is the flaw – not the outcome.
There are people making decisions inside this little known, unregulated and out-of-control branch of government that impact every facet of our lives.
None of the people operating deep inside the Intelligence Branch were elected; and our elected representative House members genuinely do not know how the system works. I assert this position affirmatively because I have talked to House and Senate staffers, including the chiefs of staff for multiple House & Senate committee seats. They are not malicious people; however, they are genuinely clueless of things that happen outside their silo. That is part of the purpose of me explaining it, with examples, in full detail with sunlight.
We begin….
In April of 2016, the FBI launched a counterintelligence operation against presidential candidate Donald Trump. The questioning about that operation is what New York Representative Elise Stefanik cites in March of 2017, approximately 11 months later (First Two Minutes).
Things to note:
♦ Notice how FBI Director James Comey just matter-of-factly explains no one outside the DOJ was informed about the FBI operation. Why? Because that’s just the way things are done. His justification for unilateral operations was “because of the sensitivity of the matter“, totally ignoring any constitutional or regulatory framework for oversight; because, well, quite simply, there isn’t any. The intelligence apparatus inside the DOJ/FBI can, and does, operate based on their own independent determinations of authority.
♦ Notice also how FBI Director Comey shares his perspective that informing the National Security Council (NSC) is the equivalent of notifying the White House. The FBI leadership expressly believe they bear no responsibility to brief the Chief Executive. As long as they tell some unknown, unelected, bureaucratic entity inside the NSC, their unwritten responsibility to inform the top of their institutional silo is complete. If the IC wants to carve out the Oval Office, they simply plant information inside the NSC and, from their perspective, their civic responsibility to follow checks-and-balances is complete. This is an intentional construct.
♦ Notice how Comey obfuscates notification to the Director of National Intelligence (DNI), by avoiding the fact James Clapper was the DNI from outset of the counterintelligence operation throughout the remainder of Obama’s term. When I get deeper into the process, we will understand how the Intelligence Branch has intentionally used the creation of the DNI position (established post 9/11/01) as a method to avoid oversight, not enhance it. Keeping an oblivious doofus like James Clapper in position held strategic value [Doofus Reminder HERE].
That video of James Comey being questioned by Elise Stefanik was the first example given to me by someone who knew the background of everything that was taking place preceding that March 20, 2017, hearing. That FBI reference point is a key to understand how the Intelligence Branch operates with unilateral authority above Congress (legislative branch), above the White House (executive branch), and even above the court system (judicial branch).
Also, watch this short video of James Clapper, because it is likely many readers have forgotten, and likely even more readers have never seen it. Watch closely how then White House national security adviser John Brennan is responding in that video. This is before Brennan became CIA Director, this is when Brennan was helping Barack Obama put the pillars into place. WATCH:
[Sidebar: Every time I post this video it gets scrubbed from YouTube (example), so save it if you ever want to see it again.]
The video of James Clapper highlights how the ODNI position (created with good national security intention) ended up becoming the fulcrum for modern weaponization, and is now an office manipulated by agencies with a vested interest in retaining power. The Intelligence Branch holds power over the ODNI through their influence and partnership with the body that authorizes the power within it, the Senate Select Committee on Intelligence (SSCI).
Factually, the modern intelligence apparatus uses checks and balances in their favor. The checks create silos of proprietary information, classified information, vaults of information that work around oversight issues. The silos, which include the exploitation of the Foreign Intelligence Surveillance Court (FISA Court, or FISC) are part of the problem.
Ironically, the Office of the Director of National Intelligence was created in the aftermath of 9/11/01 expressly to eliminate the silos of information which they felt led to a domestic terrorist attack that could have been prevented. The ODNI was created specifically upon the recommendation of the 9/11 commission.
The intent was to create a central hub of intelligence information, inside the Executive Branch, where the CIA, NSA, DoD, DoS, and DIA could deposit their unique intelligence products and a repository would be created so that domestic intelligence operations, like the DOJ and FBI could access them when needed to analyze threats to the U.S. This, they hoped, would ensure the obvious flags missed in the 9/11 attacks would not be missed again.
However, the creation of the DNI office also created an unconstitutional surveillance system of the American people. The DNI office became the tool to take massive amounts of data and use it to target specific Americans. Weaponizing the DNI office for political targeting is now the purpose of the DNI office as it exists.
The illegal and unlawful nature of the surveillance creates a need for careful protection amid the group who operate in the shadows of electronic information and domestic surveillance. You will see how it was critical to install a person uniquely skilled in being an idiot, James Clapper, into that willfully blind role while intelligence operatives worked around the office to assemble the Intelligence Branch of Government.
• The last federal budget that flowed through the traditional budgetary process was signed into law in September of 2007 for fiscal year 2008 by George W. Bush. Every budget since then has been a fragmented process of continuing resolutions and individual spending bills.
Why does this matter? Because many people think defunding the Intelligence Community is a solution; it is not…. at least, not yet. Worse yet, the corrupt divisions deep inside the U.S. intelligence system can now fund themselves from multinational private sector partnerships (banks, corporations and foreign entities).
• When Democrats took over the House of Representatives in January 2007, they took office with a plan. Nancy Pelosi became Speaker, and Democrats controlled the Senate where Harry Reid was Majority Leader. Barack Obama was a junior senator from Illinois.
Pelosi and Reid intentionally did not advance a budget in 2008 (for fiscal year 2009) because their plan included installing Barack Obama (and all that came with him) with an open checkbook made even more lucrative by a worsening financial crisis and a process called baseline budgeting. Baseline budgeting means the prior fiscal year budget is accepted as the starting point for the next year budget. All previous expenditures are baked into the cake within baseline budgeting.
Massive bailouts preceded Obama’s installation due to U.S. economic collapse, and massive bailouts continued after his installation. This is the ‘never let a crisis go to waste’ aspect. TARP (Troubled Asset Recovery Program), auto bailouts (GM), and the massive stimulus spending bill, the American Recovery and Reinvestment Act (ARRA, ie. those shovel ready jobs) were all part of the non-budget spending. The federal reserve assisted with Quantitative Easing (QE1 and QE2) as congress passed various Porkulous spending bills further spending and replacing the formal budget process.
Note: There has never been a budget passed in the normal/traditional process since September of 2007.
• While Obama’s radical ‘transformation‘ was triggered across a broad range of government institutions, simultaneously spending on the U.S. military was cut, but spending on the intelligence apparatus expanded. We were all distracted by Obamacare, and the Republican Party wanted to keep us that way. However, in the background there was a process of transformation taking place that included very specific action by Eric Holder and targeted effort toward the newest executive agency the ODNI.
 The people behind Obama, those same people now behind Joe Biden, knew from years of strategic planning that ‘radical transformation’ would require control over specific elements inside the U.S. government. Eric Holder played a key role in his position as U.S. Attorney General in the DOJ.
The people behind Obama, those same people now behind Joe Biden, knew from years of strategic planning that ‘radical transformation’ would require control over specific elements inside the U.S. government. Eric Holder played a key role in his position as U.S. Attorney General in the DOJ.
AG Holder recruited ideologically aligned political operatives who were aware of the larger institutional objectives. One of those objectives was weaponizing the DOJ-National Security Division (DOJ-NSD) a division inside the DOJ that had no inspector general oversight. For most people the DOJ-NSD weaponization surfaced with a hindsight awakening of the DOJ-NSD targeting candidate Donald Trump many years later. However, by then the Holder crew had executed almost eight full years of background work.
• The second larger Obama/Holder objective was control over the FBI. Why was that important? Because the FBI does the domestic investigative work on anyone who needs or holds a security clearance. The removal of security clearances could be used as a filter to further build the internal ideological army they were assembling. Additionally, with new power in the ODNI created as a downstream consequence of the Patriot Act, new protocols for U.S. security clearances were easy to justify.
Carefully selecting fellow ideological travelers was facilitated by this filtration within the security clearance process. How does that issue later manifest? Just look around at how politicized every intelligence agency has become, specifically including the FBI.
• At the exact same time this new background security clearance process was ongoing, again everyone distracted by the fight over Obamacare, inside the Department of State (Secretary Hillary Clinton) a political alignment making room for the next phase was being assembled. Names like Samantha Power, Susan Rice and Hillary Clinton were familiar on television while Lisa Monaco worked as a legal liaison between the Obama White House and Clinton State Department.
Through the Dept of State (DoS) the intelligence apparatus began working on their first steps to align Big Tech with a larger domestic institutional objective. Those of you who remember the “Arab Spring”, some say “Islamist Spring”, will remember it was triggered by Barack Obama’s speech in Cairo – his first foreign trip. The State Department worked with grassroots organizers (mostly Muslim Brotherhood) in Egypt, Syria, Bahrain, Qatar and Libya. Obama leaned heavily on the organizational network of Turkish President Recep Erdogan for contacts and support.
Why does this aspect matter to us? Well, you might remember how much effort the Obama administration put into recruiting Facebook and Twitter as resources for the various mideast rebellions the White House and DoS supported. This was the point of modern merge between the U.S. intelligence community and Big Tech social media.
In many ways, the coordinated political outcomes in Libya and Egypt were the beta test for the coordinated domestic political outcomes we saw in the 2020 U.S. presidential election. The U.S. intelligence community working with social media platforms and political operatives.
Overlaying all of that background activity was also a new alignment of the Obama-era intelligence apparatus with ideological federal “contractors“. Where does this contractor activity manifest? In the FISA Court opinion of Rosemary Collyer who cited the “interagency memorandum of understanding”, or MOU.
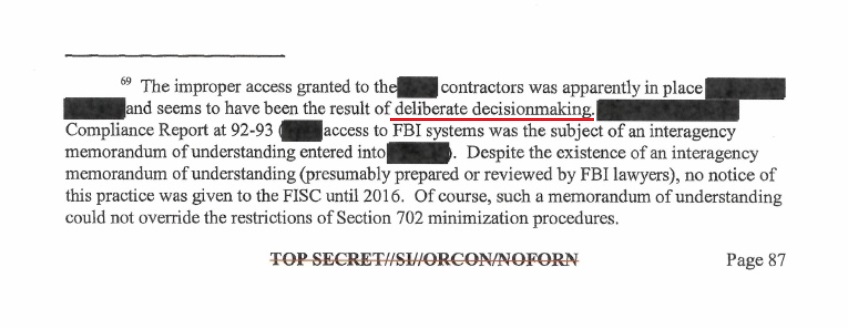
Hopefully, you can see a small part of how tentacled the system to organize/weaponize the intelligence apparatus was. None of this was accidental, all of this was by design, and the United States Senate was responsible for intentionally allowing most of this to take place. The tools the government used to monitor threats were now being used to monitor every American. WE THE PEOPLE were now the threat the national security system was monitoring.
That’s the 30,000/ft level backdrop history of what was happening as the modern IC was created. Next, we will go into how all these various intelligence networks began working in unison and how they currently control all of the other DC institutions under them; including how they can carve out the President from knowing their activity.
♦ When Barack Obama was installed in January 2009, the Democrats held a 60-seat majority in the U.S. Senate. As the people behind the Obama installation began executing their longer-term plan, the Senate Select Committee on Intelligence was a tool to create the Intelligence Branch; it was not an unintentional series of events.
When Obama was installed, Dianne Feinstein was the Chair of the Senate Select Committee on Intelligence (SSCI), and Democrat operative Dan Jones was her lead staffer. Feinstein was completely controlled by those around her including Senate Majority Leader Harry Reid. The CIA was in the process of turning over personnel following the Bush era, and as a result of a massive multi-year narrative of diminished credibility (Iraq WMD), a deep purge was underway. Obama/Holder were in the process of shifting intelligence alignment and the intensely political Democrat Leader Harry Reid was a key participant.
 THE TRAP – Many people say that Congress is the solution to eliminating the Fourth and superseding Branch of Government, the Intelligence Branch. This is an exercise in futility because the Legislative Branch, specifically the SSCI, facilitated the creation of the Intelligence Branch. The SSCI cannot put the genie they created back in the bottle without admitting they too are corrupt; and the background story of their corruption is way too intense to be exposed now.
THE TRAP – Many people say that Congress is the solution to eliminating the Fourth and superseding Branch of Government, the Intelligence Branch. This is an exercise in futility because the Legislative Branch, specifically the SSCI, facilitated the creation of the Intelligence Branch. The SSCI cannot put the genie they created back in the bottle without admitting they too are corrupt; and the background story of their corruption is way too intense to be exposed now.
Every member of the SSCI is compromised in some controlling manner. Those Senators who disliked the control over them; specifically disliked because the risk of sunlight was tenuous and, well, possible; have either left completely or stepped down from the committee. None of the SSCI members past or present would ever contemplate saying openly what their tenure involved.
[Note: You might remember when Vice Chairman Mark Warner’s text messages surfaced, there was a controlled Republican SSCI member who came to his defense in February of 2018. It was not accidental that exact Senator later became the chair of the SSCI himself. That Republican Senator is Marco Rubio, now vice-chair since the Senate re-flipped back to the optics of Democrat control in 2021.]
All of President Obama’s 2009 intelligence appointments required confirmation from the Senate. The nominees had to first pass through the Democrat controlled SSCI, and then to a full Senate vote where Democrats held a 60-vote majority. Essentially, Obama got everyone he wanted in place easily. Rahm Emmanuel was Obama’s Chief of Staff, and Valerie Jarrett was Senior Advisor.
 Tim Geithner was Treasury Secretary in 2010 when the joint DOJ/FBI and IRS operation to target the Tea Party took place after the midterm “shellacking” caused by the Obamacare backlash. Mitch McConnell was Minority Leader in the Senate but supported the targeting of the Tea Party as his Senate colleagues were getting primaried by an angry and effective grassroots campaign. McConnell’s friend, Senator Bob Bennett, getting beaten in Utah was the final straw.
Tim Geithner was Treasury Secretary in 2010 when the joint DOJ/FBI and IRS operation to target the Tea Party took place after the midterm “shellacking” caused by the Obamacare backlash. Mitch McConnell was Minority Leader in the Senate but supported the targeting of the Tea Party as his Senate colleagues were getting primaried by an angry and effective grassroots campaign. McConnell’s friend, Senator Bob Bennett, getting beaten in Utah was the final straw.
Dirty Harry and Mitch McConnell saw the TEA Party through the same prism. The TEA Party took Kennedy’s seat in Massachusetts (Scott Brown); Sharon Angle was about to take out Harry Reid in Nevada; Arlen Spector was taken down in Pennsylvania; Senator Robert Byrd died; Senator Lisa Murkowski lost her primary to Joe Miller in Alaska; McConnell’s nominee Mike Castle lost to Christine O’Donnell in Delaware; Rand Paul won in Kentucky. This is the background. The peasants were revolting…. and visibly angry Mitch McConnell desperately made a deal with the devil to protect himself.
In many ways, the TEA Party movement was/is very similar to the MAGA movement. The difference in 2010 was the absence of a head of the movement, in 2015 Donald Trump became that head figure who benefited from the TEA Party energy. Trump came into office in 2017 with the same congressional opposition as the successful TEA Party candidates in 2011.
Republicans took control of the Senate following the 2014 mid-terms. Republicans took control of the SSCI in January 2015. Senator Richard Burr became chairman of the SSCI, and Dianne Feinstein shifted to Vice-Chair. Dirty Harry Reid left the Senate, and Mitch McConnell took power again.
Republicans were in control of the Senate Intelligence Committee in 2015 when the Intelligence Branch operation against candidate Donald Trump was underway. [Feinstein’s staffer, Dan Jones, left the SSCI so he could act as a liaison and political operative between private-sector efforts (Fusion GPS, Chris Steele) and the SSCI.] The SSCI was a participant in that Fusion GPS/Chris Steele operation, and as a direct consequence Republicans were inherently tied to the problem with President Trump taking office in January of 2017. Indiana Republican Senator Dan Coats was a member of the SSCI.
Bottom line…. When it came to the intelligence system targeting Donald Trump during the 2015/2016 primary, the GOP was just as much at risk as their Democrat counterparts.
When Trump unexpectedly won the 2016 election, the SSCI was shocked more than most. They knew countermeasures would need to be deployed to protect themselves from any exposure of their prior intelligence conduct. Immediately Senator Dianne Feinstein stepped down from the SSCI, and Senator Mark Warner was elevated to Vice Chairman.
Indiana’s own Mike Pence, now Vice President, recommended fellow Hoosier, SSCI Senator Dan Coats, to become President Trump’s Director of National Intelligence (ODNI). [Apply hindsight here]
• To give an idea of the Intelligence Branch power dynamic, remind yourself how House Permanent Select Committee on Intelligence (HPSCI), Chairman Devin Nunes, tried to get access to the DOJ/FBI records of the FISA application used against the Trump campaign via Carter Page.
Remember, Devin Nunes only saw a portion of the FISA trail from his review of a Presidential Daily Brief (PDB) previously given to President Obama. Chairman Nunes had to review the PDB at the White House SCIF due to compartmented intelligence, another example of the silo benefit.
Remember the massive stonewalling and blocking of the DOJ/FBI toward Nunes? Remember the back-and-forth battle over declassification surrounding the Nunes memo?
Remember, after Nunes went directly to House Speaker Paul Ryan for help (didn’t get any), the DOJ only permitted two members from each party within the HPSCI to review the documents, and only at the DOJ offices of main justice?
Contrast that amount of House Intel Committee railroading by intelligence operatives in the DOJ, DOJ-NSD and FBI, with the simple request by Senate Intelligence Vice Chairman Mark Warner asking to see the Carter Page FISA application and immediately a copy being delivered to him on March 17th 2017.
Can you see which intelligence committee is aligned with the deepest part of the deep state?
Oh, how quickly we forget:
The contrast of ideological alignment between the House, Senate and Intelligence Branch is crystal clear when viewed through the prism of cooperation. You can see which legislative committee holds the power and support of the Intelligence Branch. The Senate Intel Committee facilitates the corrupt existence of the IC Branch, so the IC Branch only cooperates with the Senate Intel Committee. It really is that simple.
• The Intelligence Branch carefully selects its own members by controlling how security clearances are investigated and allowed (FBI). The Intelligence Branch also uses compartmentalization of intelligence as a way to keep each agency, and each downstream branch of government (executive, legislative and judicial), at arm’s length as a method to stop anyone from seeing the larger picture of their activity. I call this the “silo effect“, and it is done by design.
I have looked at stunned faces when I presented declassified silo product from one agency to the silo customers of another. You would be astonished at what they don’t know because it is not in their ‘silo’.
 Through the advice and consent rules, the Intelligence Branch uses the SSCI to keep out people they consider dangerous to their ongoing operations. Any appointee to the intelligence community must first pass through the Senate Select Committee on Intelligence, before they get a full Senate vote. If the SSCI rejects the candidate, they simply refuse to take up the nomination. The president is then blocked from that appointment. This is what happened with President Trump over and over again.
Through the advice and consent rules, the Intelligence Branch uses the SSCI to keep out people they consider dangerous to their ongoing operations. Any appointee to the intelligence community must first pass through the Senate Select Committee on Intelligence, before they get a full Senate vote. If the SSCI rejects the candidate, they simply refuse to take up the nomination. The president is then blocked from that appointment. This is what happened with President Trump over and over again.
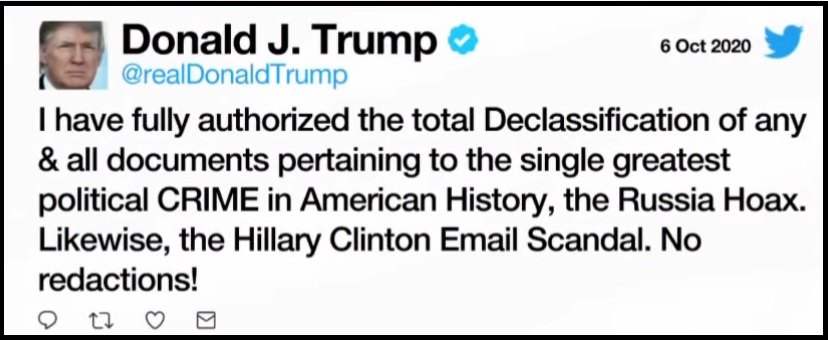
• Additionally, the Intelligence Branch protects itself, and its facilitating allies through the formal classification process. The Intelligence Branch gets to decide unilaterally what information will be released and what information will be kept secret. There is no entity outside the Intelligence Branch, and yes that includes the President of the United States, who can supersede the classification authority of the Intelligence Branch. {Go Deep} and {Go Deep} This is something 99.9% of the people on our side get totally and frustratingly wrong.
No one can declassify, or make public, anything the Intelligence Branch will not agree to. Doubt this? Ask Ric Grenell, John Ratcliffe, or even President Trump himself.
• The classification process is determined inside the Intelligence Branch, all by themselves. They get to choose what rank of classification exists on any work product they create; and they get to decide what the classification status is of any work product that is created by anyone else. The Intelligence Branch has full control over what is considered classified information and what is not. The Intelligence Branch defines what is a “national security interest” and what is not. A great technique for hiding fingerprints of corrupt and illegal activity.
[For familiar reference see the redactions to Lisa Page and Peter Strzok text messages. The Intelligence Branch does all redactions.]
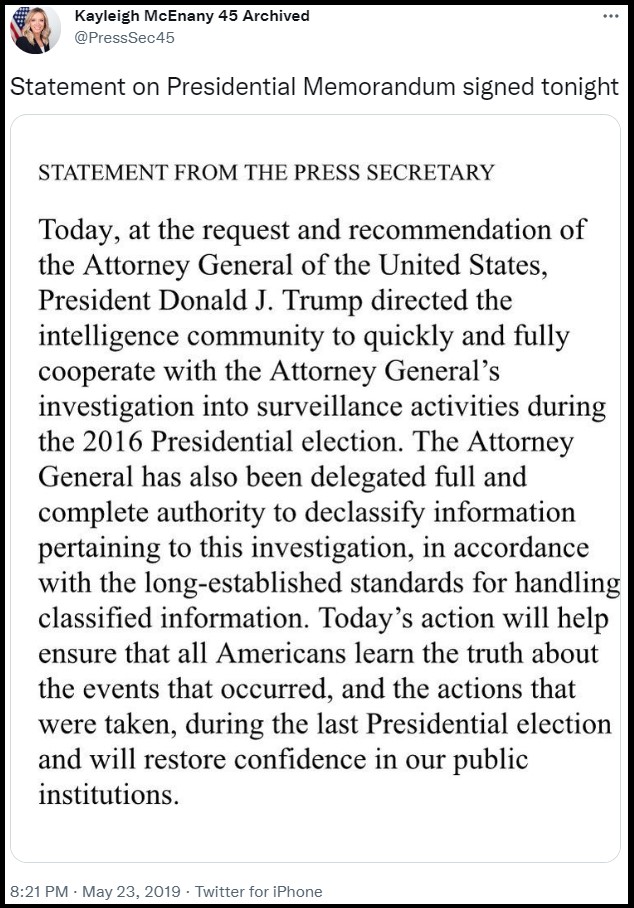 • Similarly, the declassification process is a request by an agency, even a traditionally superior agency like the President of the United States, to the Intelligence Branch asking for them to release the information. The Intelligence Branch again holds full unilateral control.
• Similarly, the declassification process is a request by an agency, even a traditionally superior agency like the President of the United States, to the Intelligence Branch asking for them to release the information. The Intelligence Branch again holds full unilateral control.
If the head of the CIA refuses to comply with the declassification instruction of the President, what can the president do except fire him/her? {Again, GO DEEP} How does the President replace the non-compliant cabinet member? They have to go through the SSCI confirmation. See the problem?
Yes, there are ways to break up the Intelligence Branch, but they do not start with any congressional effort. As you can see above, the process is the flaw – not the solution. Most conservative pundits have their emphasis on the wrong syllable. Their cornerstone is false.
For their own self-preservation, the Intelligence Branch has been interfering in our elections for years. The way to tear this apart begins with STATE LEVEL election reform that blocks the Legislative Branch from coordinating with the Intelligence Branch.
The extreme federalism approach is critical and also explains why Joe Biden has instructed Attorney General Merrick Garland to use the full power of the DOJ to stop state level election reform efforts. The worry of successful state level election control is also why the Intelligence Branch now needs to support the federal takeover of elections.
Our elections have been usurped by the Intelligence Branch. Start with honest elections and we will see just how much Democrat AND Republican corruption is dependent on manipulated election results. Start at the state level. Start there…. everything else is downstream.
♦ COLLAPSED OVERSIGHT – The modern system to ‘check’ the Executive Branch was the creation of the legislative “Gang of Eight,” a legislative oversight mechanism intended to provide a bridge of oversight between the authority of the intelligence community within the Executive Branch.
The Go8 construct was designed to allow the President authority to carry out intelligence operations and provide the most sensitive notifications to a select group within Congress.
The Go8 oversight is directed to the position, not the person, and consists of: (1) The Speaker of the House; (2) The Minority Leader of the House; (3) The Chair of the House Permanent Select Committee on Intelligence, HPSCI; (4) The Ranking Member (minority) of the HPSCI; (5) The Leader of the Senate; (6) The Minority Leader of the Senate; (7) The Chair of the Senate Select Committee on Intelligence, SSCI; and finally (8) the Vice-Chair of the SSCI.
Example: When the Chief Executive (the President) initiates an intelligence operation on behalf of the United States, the President triggers a “finding memo.” In essence, the instruction to the intel agency or agencies to authorize a covert operation. When that process takes place, the Go8 are the first people notified. Depending on the sensitivity of the operation, sometimes the G08 are notified immediately after the operation is conducted. The notification can be a phone call or an in-person briefing.
Because of the sensitivity of their intelligence information, the Gang of Eight hold security clearances that permit them to receive and review all intelligence operations. The intelligence community are also responsible for briefing the Go8 with the same information they use to brief the President.

~ 2021 Gang of Eight ~
The Go8 design is intended to put intelligence oversight upon both political parties in Congress; it is designed that way by informing the minority leaders of both the House and Senate as well as the ranking minority members of the SSCI and HPSCI. Under the concept, the President cannot conduct an intelligence operation; and the intelligence community cannot carry out intelligence gathering operations without the majority and minority parties knowing about it.
The modern design of this oversight system was done to keep rogue and/or corrupt intelligence operations from happening. However, as we shared in the preview to this entire discussion, the process was usurped during the Obama era. {GO DEEP}
Former FBI Director James Comey openly admitted to Congress on March 20, 2017, that the FBI, FBI Counterintelligence Division, DOJ and DOJ-National Security Division, together with the Office of the Director of National Intelligence (ODNI) and the CIA, had been conducting independent investigations of Donald Trump for over a year without informing the Go8. Comey justified the lack of informing Go8 oversight by saying, “because of the sensitivity of the matter.”
Stupidly, Congress never pressed James Comey on that issue. The arrogance was astounding, and the acceptance by Congress was infuriating. However, that specific example highlighted just how politically corrupt the system had become. In essence, Team Obama usurped the entire design of congressional oversight…. and Congress just brushed it off.
Keep in mind, Comey did not say the White House was unaware; in fact he said exactly the opposite, he said, “The White House was informed through the National Security Council,” (the NSC). The unavoidable implication and James Comey admission that everyone just brushed aside, was that President Obama’s National Security Advisor, Susan Rice, was informed of the intelligence operation(s) against Donald Trump. After all, the NSC reports to the National Security Advisor.
Does the January 20, 2017, Susan Rice memo look different now?
Again, no one saw the immediate issue. What Comey just described on that March Day in 2017 was the usurpation of the entire reason the Gang of Eight exists; to eliminate the potential for political weaponization of the Intelligence Community by the executive branch. The G08 notifications to the majority and minority are specifically designed to make sure what James Comey admitted to doing was never supposed to happen.
Team Obama carried out a political operation using the intelligence community and the checks-and-balances in the system were intentionally usurped. This is an indisputable fact.
Worse still, the entire legislative branch of Congress, which then specifically included the Republicans that now controlled the House and Senate, did nothing. They just ignored what was admitted. The usurpation was willfully ignored.
The mechanism of the G08 was bypassed without a twitch of condemnation or investigation…. because the common enemy was Donald Trump.
This example highlights the collapse of the system. Obama, the Executive Branch, collapsed the system by usurping the process; in essence the process became the bigger issue, and the lack of immediate Legislative Branch reaction became evidence of open acceptance. The outcomes of the usurpation played out over the next four years, Donald J. Trump was kneecapped and lost his presidency because of it. However, the bigger issue of the collapse still exists.
The downstream consequence of the Legislative Branch accepting the Executive Branch usurpation meant both intelligence committees were compromised. Additionally, the leadership of both the House and Senate were complicit. Think about this carefully. The Legislative Branch allowance of the intelligence usurpation meant the Legislative Branch was now subservient to the Intelligence Branch.
That’s where we are.
Right now.
That’s where we are.
Term-3 Obama is now back in the White House with Joe Biden.
NOTE: Former Obama National Security aide and counsel to the President, Lisa Monaco, is in her current position as Deputy Attorney General, specifically to make sure all of these revelations do not become a legal risk to Barack Obama and the people who created them. The SSCI confirmed Monaco for this purpose because the Senate is just as much at risk.
Term-1 and Term-2 Obama usurped the ‘check and balance‘ within the system and weaponized the intelligence apparatus. During Trump’s term that weaponization was covered up by a compliant congress, complicit senate intelligence committee, and not a single member of the oversight called it out. Now, Term-3 Obama steps back in to continue the cover up and continue the weaponization.
Hopefully, you can now see the scale of the problem that surrounds us with specific citation for what has taken place. What I just explained to you above is not conspiracy theory, it is admitted fact that anyone can look upon. Yet….
Have you seen this mentioned anywhere? Have you seen this called out by anyone in Congress? Have you seen anyone in media (ally or adversary) call this out? Have you seen any member of the Judicial Branch stand up and say wait, what is taking place is not okay? Have you seen a single candidate for elected office point this out? Have you seen anyone advising a candidate to point this out?
This is our current status. It is not deniable. The truth exists regardless of our comfort.
Not a single person in power will say openly what has taken place. They are scared of the Fourth Branch. The evidence of what has taken place is right there in front of our face. The words, actions and activities of those who participated in this process are not deniable, in fact most of it is on record.
There are only two members of the Gang of Eight who have existed in place from January 2007 (the real beginning of Obama’s term, two years before he took office when the Congress flipped). Only two members of the G08 have been consistently in place from January of 2007 to right now, today. All the others came and went, but two members of the Gang of Eight have been part of that failed and collapsed oversight throughout the past 15 years, Nancy Pelosi and Mitch McConnell.
 ♦ TECHNOLOGY – On a global scale – the modern intelligence gathering networks are now dependent on data collection to execute their intelligence missions. In the digital age nations have been executing various methods to gather that data. Digital surveillance has replaced other methods of interception. Those surveillance efforts have resulted in a coalescing of regional data networks based on historic multi-national relationships.
♦ TECHNOLOGY – On a global scale – the modern intelligence gathering networks are now dependent on data collection to execute their intelligence missions. In the digital age nations have been executing various methods to gather that data. Digital surveillance has replaced other methods of interception. Those surveillance efforts have resulted in a coalescing of regional data networks based on historic multi-national relationships.
We have a recent frame of reference for the “U.S. data collection network” within the NSA. Through the allied process the Five Eyes nations all rely on the NSA surveillance database (U.K, Australia, Canada, New Zealand and U.S.) The NSA database provides the digital baseline for intelligence operations in defense of our allies. The portals into the NSA database are essentially an assembly of allies in like-minded ideological connection to the United States.
Unfortunately, there have been some revelations about the NSA database being used to monitor our allies, like in the example of Germany and surveillance on Angela Merkel’s phone. As long as “the good guys” are operating honorably, allies of the United States can feel confident about having protection from the NSA surveillance of global digital data. We warn our friends if we detect something dangerous etc.
The U.S. has nodes on communication pipelines to intercept and extract data. We have also launched hundreds, perhaps thousands, of satellites to conduct surveillance and gather up data. All of this data is fed into the NSA database where it is monitored (presumably) as a national security mechanism, and in defense of our allies.
However, what about data collection or data networks that are outside the NSA database? What do our enemies do? The NSA database is just one intelligence operation of digital surveillance amid the entire world, and we do not allow access by adversaries we are monitoring. So what do they do? What do our allies do who might not trust the United States due to past inconsistencies, ie. the Middle East?
The answers to those questions highlight other data collection networks. So, a brief review of the major players is needed.
♦ CHINA – China operates their own database. They, like the NSA, scoop up data for their system. Like us, China launches satellites and deploys other electronic data collection methods to download into their database. This is why the issues of electronic devices manufactured in China becomes problematic. Part of the Chinese data collection system involves the use of spyware, hacking and extraction.
Issues with Chinese communication company Huawei take on an added dimension when you consider the goal of the Chinese government to conduct surveillance and assemble a network of data to compete with the United States via the NSA. Other Chinese methods of surveillance and data-collection are less subversive, as in the examples of TicTok and WeChat. These are Chinese social media companies that are scraping data just like the NSA scrapes data from Facebook, Twitter and other Silicon Valley tech companies. [ Remember, the Intelligence Branch is a public-private partnership. ]
♦ RUSSIA – It is very likely that Russia operates their own database. We know Russia launches satellites, just like China and the USA, for the same purposes. Russia is also very proficient at hacking into other databases and extracting information to store and utilize in their own network. The difference between the U.S., China and Russia is likely that Russia spends more time on the hacking aspect because they do not generate actual technology systems as rapidly as the U.S. and China.
The most recent database creation is an outcome of an ally having to take action because they cannot rely on the ideology of the United States remaining consistent, as the administrations ping-pong based on ideology.
♦ SAUDI ARABIA – Yes, in 2016 we discovered that Saudi Arabia was now operating their own intelligence data-gathering operation. It would make sense, given the nature of the Middle East and the constant fluctuations in political support from the United States. It is a lesson the allied Arab community and Gulf Cooperation Council learned quickly when President Obama went to Cairo in 2009 and launched the Islamist Spring (Arab Spring) upon them.


I have no doubt the creation of the Saudi intelligence network was specifically because the Obama administration started supporting radical Islamists within the Muslim Brotherhood and threw fuel on the fires of extremism all over the Arab world.
Think about it., What would you do if you were Saudi Arabia, Egypt, Bahrain, Kuwait, the UAE, Jordan, Oman or Yemen and you knew the United States could just trigger an internal uprising of al-Qaeda, ISIS and the political arm of the Muslim Brotherhood to seek your destruction?
Without a doubt, those urgent lessons from 2009, 2010, 2011 triggered the formation of the Arab Intelligence Network as a network to defend itself with consistency. They assembled the network and activated it in 2017 as pictured above.
♦ Israel – Along a similar outlook to the Arab network, no doubt Israel operates an independent data collection system as a method of protecting itself from ever-changing U.S. politics amid a region that is extremely hostile to its very existence. Like the others, Israel launches proprietary satellites, and we can be sure they use covert methods to gather electronic data just like the U.S. and China.
As we have recently seen in the Pegasus story, Israel creates spyware programs that are able to track and monitor cell phone communications of targets. The spyware would not work unless Israel had access to some network where the phone meta-data was actually stored. So yeah, it makes sense for Israel to operate an independent intelligence database.
♦ Summary: As we understand the United States Intelligence Branch of government as the superseding entity that controls the internal politics of our nation, we also must consider that multiple nations have the same issue. There are major intelligence networks around the world beside the NSA “Five-Eyes” database. China, Russia, Saudi Arabia and Israel all operate proprietary databases deploying the same tools and techniques for assembly.
The geopolitical conflict that has always existed has now shifted into a digital battle-space. The Intelligence Agencies from these regions are now operating as the backbone of the government that uses them and has become dependent on them. [<- Reread that].
Once you accept the digital-era intelligence apparatus of China, Russia, Saudi-Arabia, The United States and Israel, are now the primary national security mechanisms for stabilization of government; then you accept the importance of those intelligence operations.
Once you understand how foundational those modern intelligence operations have become for the stability and continuity of those governments…… then you begin to understand just how the United States intelligence community became more important than the government that created it.
From that point it is then critical to understand that domestic intelligence operations are underway to monitor the electronic communication of American citizens inside our own country. YOU are under surveillance. The parents who confront school boards are under surveillance. The political operatives inside the FBI are monitoring everyone who comes onto the radar, that is why the National School Boards Association asked the White House, then the DOJ, to have the FBI start targeting parents. Are things making sense now?
♦ Public Private Partnership – The modern Fourth Branch of Government is only possible because of a Public-Private partnership with the intelligence apparatus. You do not have to take my word for it, the partnership is so brazened they have made public admissions.
 The biggest names in Big Tech announced in June their partnership with the Five Eyes intelligence network, ultimately controlled by the NSA, to: (1) monitor all activity in their platforms; (2) identify extremist content; (3) look for expressions of Domestic Violent Extremism (DVE); and then, (4) put the content details into a database where the Five Eyes intelligence agencies (U.K., U.S., Australia, Canada, New Zealand) can access it.
The biggest names in Big Tech announced in June their partnership with the Five Eyes intelligence network, ultimately controlled by the NSA, to: (1) monitor all activity in their platforms; (2) identify extremist content; (3) look for expressions of Domestic Violent Extremism (DVE); and then, (4) put the content details into a database where the Five Eyes intelligence agencies (U.K., U.S., Australia, Canada, New Zealand) can access it.
Facebook, Twitter, Google and Microsoft are all partnering with the intelligence apparatus. It might be difficult to fathom how openly they admit this, but they do. Look at this sentence in the press release (emphasis mine):
[…] “The Group will use lists from intelligence-sharing group Five Eyes adding URLs and PDFs from more groups, including the Proud Boys, the Three Percenters and neo-Nazis.”
Think about that sentence structure very carefully. They are “adding to” the preexisting list…. admitting the group (aka Big Tech) already have access to the the intelligence-sharing database… and also admitting there is a preexisting list created by the Five Eyes consortium.
Obviously, who and what is defined as “extremist content” will be determined by the Big Tech insiders themselves. This provides a gateway, another plausible deniability aspect, to cover the Intelligence Branch from any oversight.
When the Intelligence Branch within government wants to conduct surveillance and monitor American citizens, they run up against problems due to the Constitution of the United States. They get around those legal limitations by sub-contracting the intelligence gathering, the actual data mining, and allowing outside parties (contractors) to have access to the central database.
The government cannot conduct electronic searches (4th amendment issue) without a warrant; however, private individuals can search and report back as long as they have access. What is being admitted is exactly that preexisting partnership. The difference is that Big Tech will flag the content from within their platforms, and now a secondary database filled with the extracted information will be provided openly for the Intelligence Branch to exploit.
 The volume of metadata captured by the NSA has always been a problem because of the filters needed to make the targeting useful. There is a lot of noise in collecting all data that makes the parts you really want to identify more difficult to capture. This new admission puts a new massive filtration system in the metadata that circumvents any privacy protections for individuals.
The volume of metadata captured by the NSA has always been a problem because of the filters needed to make the targeting useful. There is a lot of noise in collecting all data that makes the parts you really want to identify more difficult to capture. This new admission puts a new massive filtration system in the metadata that circumvents any privacy protections for individuals.
Previously, the Intelligence Branch worked around the constitutional and unlawful search issue by using resources that were not in the United States. A domestic U.S. agency, working on behalf of the U.S. government, cannot listen on your calls without a warrant. However, if the U.S. agency sub-contracts to say a Canadian group, or foreign ally, the privacy invasion is no longer legally restricted by U.S. law.
What was announced in June 2021 is an alarming admission of a prior relationship along with open intent to define their domestic political opposition as extremists.
July 26 (Reuters) – A counterterrorism organization formed by some of the biggest U.S. tech companies including Facebook (FB.O) and Microsoft (MSFT.O) is significantly expanding the types of extremist content shared between firms in a key database, aiming to crack down on material from white supremacists and far-right militias, the group told Reuters.
Until now, the Global Internet Forum to Counter Terrorism’s (GIFCT) database has focused on videos and images from terrorist groups on a United Nations list and so has largely consisted of content from Islamist extremist organizations such as Islamic State, al Qaeda and the Taliban.
Over the next few months, the group will add attacker manifestos – often shared by sympathizers after white supremacist violence – and other publications and links flagged by U.N. initiative Tech Against Terrorism. It will use lists from intelligence-sharing group Five Eyes, adding URLs and PDFs from more groups, including the Proud Boys, the Three Percenters and neo-Nazis.
The firms, which include Twitter (TWTR.N) and Alphabet Inc’s (GOOGL.O) YouTube, share “hashes,” unique numerical representations of original pieces of content that have been removed from their services. Other platforms use these to identify the same content on their own sites in order to review or remove it. (read more)
The influence of the Intelligence Branch now reaches into our lives, our personal lives.
[The Intercept] – […] Behind closed doors, and through pressure on private platforms, the U.S. government has used its power to try to shape online discourse. According to meeting minutes and other records appended to a lawsuit filed by Missouri Attorney General Eric Schmitt, a Republican who is also running for Senate, discussions have ranged from the scale and scope of government intervention in online discourse to the mechanics of streamlining takedown requests for false or intentionally misleading information.
“Platforms have got to get comfortable with gov’t. It’s really interesting how hesitant they remain,” Microsoft executive Matt Masterson, a former DHS official, texted Jen Easterly, a DHS director, in February.
In a March meeting, Laura Dehmlow, an FBI official, warned that the threat of subversive information on social media could undermine support for the U.S. government. Dehmlow, according to notes of the discussion attended by senior executives from Twitter and JPMorgan Chase, stressed that “we need a media infrastructure that is held accountable.” (read more)
In the decades before 9/11/01 the intelligence apparatus intersected with government, influenced government, and undoubtedly controlled many institutions with it. The legislative oversight function was weak and growing weaker, but it still existed and could have been used to keep the IC in check. However, after the events of 9/11/01, the short-sighted legislative reactions opened the door to allow the surveillance state to weaponize against domestic enemies.
[…] The extent to which the DHS initiatives affect Americans’ daily social feeds is unclear. During the 2020 election, the government flagged numerous posts as suspicious, many of which were then taken down, documents cited in the Missouri attorney general’s lawsuit disclosed. And a 2021 report by the Election Integrity Partnership at Stanford University found that of nearly 4,800 flagged items, technology platforms took action on 35 percent — either removing, labeling, or soft-blocking speech, meaning the users were only able to view content after bypassing a warning screen. The research was done “in consultation with CISA,” the Cybersecurity and Infrastructure Security Agency.
Prior to the 2020 election, tech companies including Twitter, Facebook, Reddit, Discord, Wikipedia, Microsoft, LinkedIn, and Verizon Media met on a monthly basis with the FBI, CISA, and other government representatives. According to NBC News, the meetings were part of an initiative, still ongoing, between the private sector and government to discuss how firms would handle misinformation during the election. (keep reading)
After the Patriot Act was triggered, not coincidentally only six weeks after 9/11, a slow and dangerous fuse was lit that ends with the intelligence apparatus being granted a massive amount of power. Simultaneously the mission of the intelligence community now encompassed monitoring domestic threats as defined by the people who operate the surveillance system.
The problem with assembled power is always what happens when a Machiavellian network takes control over that power and begins the process to weaponize the tools for their own malicious benefit. That is exactly what the network of President Barack Obama did.
The Obama network took pre-assembled intelligence weapons (we should never have allowed to be created) and turned those FBI, DOJ-NSD, DHS and ODNI weapons into political tools for his radical and fundamental change. The target was the essential fabric of our nation.
Ultimately, this corrupt political process gave power to create the Fourth Branch of Government, the Intelligence Branch and a massive nationwide surveillance state. From that perspective the fundamental change was successful.
This is the scale of corrupt political compromise on both sides of the DC dynamic that we are up against. Preserving this surveillance system, a public-private partnership, is also what removing Donald Trump was all about…. The targeting of President Trump in order to preserve the system, the system that was weaponized during the Obama administration, is what the actions of the DOJ, FBI and DHS are all about.
What would powerful people in DC do to stop the American people from finding this out?
A controlled 2020 election? An increased censorship in the aftermath? A raid on Mar-a-Lago?
…The need for control is a reaction to fear.
If only people understood how accurate this really is.
(1) The Patriot Act turned the intel surveillance radar from foreign searches for terrorists to domestic searches for terrorists.
(2) Obama/Biden then redefined what is a "terrorist" to include their political opposition. https://t.co/EW43WmpeaT
— TheLastRefuge (@TheLastRefuge2) October 14, 2022
Support Ongoing CTH Research HERE
This product works well with General Dynamics attack drones. Seek the undesirable social media and destroy them. All hands free.
Yeah, hands free, a must for these cowards.
Use the contact tracing app on your smartphone to pinpoint your location.
Precisely why I don’t use any “smart” appliances or gadgets. I have a cheap little consumer cellular phone and it works just fine for me. I stay of of all the 5G crap promoted by my computer provider, etc. If you cut them off at the knees, they will have no power and isn’t that what most of us want once again? Less gubmint intervention…….
Hitler and Stalin are rolling over in their graves with envy. Or jumping up and down with joy in hell.
I will freely admit that “I smelled a rat” back in 2001, when I realized that a Congressional document more than one thousand pages long had, miraculously, “appeared.” Even before I had fully realized what had actually happened to those three buildings, I realized that: “no one can write legislation that fast.”
Actually, there is a whole industry that exists to prepare potential legislation to hand over to the politicians. Sundance has lamented the fact that there are no (?) groups preparing MAGA legislation. Trump was a sitting duck without the support.
Who is writing MAGA legislation now? Who would fund that?
This post is not in your Twitter timeline as of 4:44pm CST, Sundance.
It went up 21 min ago PST….
Thanks, Ad rem 😉
Twitter under what name? Sundance? CTH?
Looks like @TheLastRefuge2…and I’m not a Twitter gal!
“(1) The Patriot Act turned the intel surveillance radar from foreign searches for terrorists to domestic searches for terrorists.”
This should possibly be updated to read:
(1) The Patriot Act turned the intel surveillance radar from foreign searches for terrorists to domestic searches for threats to the Deep State’s and DC Establishment’s undemocratic vice grip on power.
Thanks for pointing out that particular sentence in Sundance’s post, GB.
Am I the only one who finds it very odd that foreigners the U.S. State Dept. issued visas to, who attacked the U.S. on 9/11/01, caused the U.S. government to turn the intelligence inward against Americans? Americans didn’t attack us on 9/11, rather, foreigners the U.S. State Dept. allowed in did.
-snip-
“Oct. 23, 2002 — A new report accuses the State Department of staggering lapses in its visa program that gave Sept. 11 hijackers entry into the United States.”
State Dept. Lapses Aided 9/11 Hijackers – ABC News (go.com)
-snip-
” Five of the 9/11 hijackers overstayed their visas, and GAO found that 36 of the roughly 400 people convicted of terrorism-related charges since September 2001 had overstayed their visas.
“Despite numerous congressional and DHS efforts, we still lack an exit system that will effectively identify people who have overstayed their visas, and do so in real time,” Lieberman said. “The reality is that U.S. VISIT remains a very troubled and ineffective program.”
Majority Media | Homeland Security & Governmental Affairs Committee | Homeland Security & Governmental Affairs Committee (senate.gov)
Millions from a multitude of countries walk unmolested across the the Southern Border.
Its all a big farce.
“staggering lapses”
Or, more specifically, “accidentally on purpose”…….
More like it.
No, IMHO you are among the majority here at least.
I think Sundance and others who’ve analyzed this change of offensive focus by the federal LEAs have all concluded that it is purely political yet blatantly and treacherously anti-Constitutional.
The corruption of the intelligence agencies along with the corruption of the federal LEAs and most of the seats of power in the federal government has also told us: The vast majority of us were asleep while the Communists / Fascists gradually but steadily took over most of the country’s cultural institutions where power is based.
We live with the illusion of a democratically-run federal republic of America
Ever consider the amount of man hours and money that goes into keeping that illusion alive? It’s mind blowing!
Yes. And that staggering amount of money has come largely from taxpayer’s own pockets (WITHOUT OUR CONSENT), but also from Big Tech, the U.S. Chamber of Commerce, and the multi-billion dollar multinational corporations and banks who gain the most from globalist policies, open borders, and the elimination of the USA’s national sovereignty.
The Leftists’ promise in the 1960’s to “march through the institutions” was serious and you can now see that they have succeeded in their “long march.”
Exactly. Good recall of that infamous phrase.
And that many of our legislators and state department heads seem to be working for the other world powers: China, Russia, Muslim extremists, Saudi. The WEC seems to be playing the market to sell their ability to allow access to that power, making money and gaining assets at every turn.
When did then DHS Secretary Janet Napolitano refer to veterans returning from Iraq and Afghanistan as (paraphrasing) potential national security risks? As I recall, that was soon followed up by none other than VP Biden being one of the first to use “domestic terrorist” when referring to those same veterans and others that disagreed with the Obama administration.
It was 2009. I found an article where it is referenced. See at the bottom for some links:
https://www.charlottemagazine.com/veterans-and-domestic-terrorism/
That was the year of the Fort Hood incident. Remember that? See this article:
https://citizenwells.com/2009/11/11/janet-napolitano-homeland-security-secretary-fort-hood-comments-napolitano-asked-to-resign-first-priority-quell-anti-islam-sentiments-moveamericaforward-org-war-veterans-terrorists-domestic-co/
How ironic that the Patriot Act is the most anti-patriotic weapon against true patriots.
Yes. Isn’t that naming aspect true of EVERY bill initiated by and passed by every DemocRAT-controlled House of Representatives? Their bill titles are ALWAYS designed to DECEIVE the public about what the bill actually accomplishes and enables, contrasted with its net impact / effect on the American population.
you could easily make the argument that the actual longer term purpose of the PA was always to track and target patriotic American citizens, and to negate their pesky constitutional rights.
Is there anything more unconstitutional than how the current FISA Court atrocity has been abused against US citizens?
AGREE 100%
I’m sure someone could think a worse anti-constitutional abuse of the law, but that’s right up there at the top.
I think heavily-armed FBI soldiers ramming down innocent citizens’ front doors and seizing their computers, mobile comms devices, and arresting them on false and/or grossly exaggerated charges may be worse than spying on their comms.
Then there is the illegal imprisonment of the Jan 6. attendees and the abusive treatment to which they have been subjected. Especially when we now know for certain that the FBI had infiltrated the Jan. 6 event and some attending civilian pro-freedom organizations with covert agents who were instructed to agitate the crowd into violence. That’s right at the top along with illegal domestic surveillance and censorship of factual social media posts.
Indeed GB, the swamp must never be attacked.
You forgot the /s. …
The Swamp must be attacked continuously and relentlessly using every 5GW* weapon available.
*5th Generation Warfare
“the CIA, NSA, DoD, DoS, and DIA”
The Axis of Evil.
Yes all 5, including the one that many people still have a fetish for. Plus the DOJ and FBI, of course.
Does anybody else remember Hugo Chavez’s remarks about Obama sometime around 2010?
Chavez stated that he liked what Obama was doing but that he (Obama) needed to learn how to control the media.
This was around the time of the infamous “bro” handshake between the two communists.
Chavez also gave Obama a book at that meeting. Does anybody know what that book was?
Probably Das Capital or Mein Kampf
-snip-
“President Obama got in several good lines during his trip to meet with Latin American leaders on Saturday, but the funniest came when reporters asked about the book that Hugo Chávez, the president of Venezuela, gave him: “The Open Veins of Latin America,” by Eduardo Galeano. “I thought it was one of Chávez’s books. I was going to give him one of mine,” Obama quipped.
“Though I’m sure “Un Brazalete Tricolor” is every bit as riveting as “Dreams from My Father,” Obama should be glad to be in possession of “Open Veins,” which shot to number eleven on Amazon within hours of Obama receiving it. Whatever one thinks of its message (it denounces both U.S. imperialism and the ruling élites of Latin America from a Marxist-Leninst perspective), the book has a fascinating history.”
The Book Chávez Gave Obama | The New Yorker
Thanks for the info.
Anytime 🙂
The book Chavez gave Barack Hussein Obama was ”The Open Veins of Latin America” by Uruguayan leftist Eduardo Galeano. It says that all the problems of the subcontinent are the fault of American Imperialism.
Open Veins of Latin America: Five Centuries of the Pillage of a Continent.
Eduardo Galeano
The Patriot Axe.
This masterpiece of research, analysis and writing belongs in some kind of national archive.
The only blogger/journalist/patriot who has consistently gotten everything right is our hero Sundance, one of the most dangerous men in America if not the world.
Essays like this one make me very worried. Thanks to Sundance, they know that we know and we know that they know we know. It is kind of like throwing down the gauntlet to the Deep State.
All I can say is, may the good Lord bless and keep Sundance from harm. We need him now more than ever.
We are all repositories of this information, sort of like the internet…distributed network, multiple pathways, multiple nodes. Consider Whole Earth Catalogue, parallel economy. Lots to think about, and remember. Honor, Truth, Duty.
Amen Seneca Amen
100 up votes Seneca.
How I envy you Americans for having ONE national treasure in Sundance.
May the good Lord keep him safe.
duplicate
So are you saying Sundance that this has gone beyond our ability stop, and we must just accept this as a new way of life?
Just when we think the American Deep State can’t be any more evil than we already know it is, Sundance peals another layer of the onion.
I don’t think Sundance ever loses hope. His plan of action is based on us acting locally, building our networks, passing information on, not being afraid, not being cowed.
There is a spiritual power that transcends us. We the People have far more power than we realize. People united around good are a spiritual force to be reckoned with. China knows it. Russia knows it. And the collective enemy continually highlighted by Sundance, DJT, and too few others is afraid of that power we have.
We must first be awakened, have our eyes open, and not be silenced or thwarted.
Ask General Paetreos.
It occurred to me recently that a strong border would minimize the need for an inward-looking surveillance network.
I then began to wonder if our border security was intentionally relaxed, in part, to justify the transition of our surveillance network from an externally-looking one to an internally-looking one.
The DHS is warning of domestic terrorist attacks against illegal immigrants. Talk about spin from foreign threats to US citizens are the threat.
https://truenews.media/2022/12/29/dhs-is-warning-of-domestic-violent-extremist-threats/
The weakened, purposefully destroyed borders are designed to dilute U.S. citizens who understand and have tasted the heart of the Declaration and Constitutional freedoms. Those being allowed to enter are dependent, ignorant, available for manipulation.
Yes
…and maybe even to turn against us citizens in a very dangerous way.
The detail and completeness of articles here on CTH is unrivaled. Problem is, once I’ve consumed the information my mind is unable to decide if it was worth it, now knowing the evils We face… Local elections, here I come!!
Like a virgin losing their virginity…can’t go back…the innocence is gone.
“Ignorance is bliss”.
Well at least the (Gang ) of 8 is apptly named…
If the Patriot Act expired in 2020 why are government agencies still looking inward?
Answer: Because they can.
This is no longer a nation. It is all an illusion.
We have never ‘owned’ anything. If you can’t pay the taxes, they take it away. It’s always been an illusion. That’s why they call it the American ‘Dream’.
Self reflection: if everyone is a threat to you [intelligence state], maybe consider YOU yourself are the threat.
Holy cow. What a piece of work. So glad to have it. Sundance is remarkable.
I have a comment regarding Twitter and what was brewing in 2018.
By late 2017, I was being shadow banned in three of four categories.
I didn’t even have a good definition of shadow banning. I was fairly naive.
I decided to go to the @jack profile and see if he was addressing complaints.
Not everyone was being shadow banned but I, a classic nobody, was.
Who knew I would even be suspended on the same day Donald Trump was years later?
No power. No particular knowledge. No position. Never pushed arguments. I did ask a
lot of questions though.
While @jack, I saw an exchange. I took a screen shot just in case it was about my concern.
https://postimg.cc/64N8qCrg
Just who was this guy pushing a seemingly foot-dragging Jack around? Just what was it that @jack was building at Twitter to eliminate whomever they pleased? And did he build it? Or was he just waiting for someone to tell him it had been built?
We’ve got all the details we need about everything and everyone involved in the rat’s nest known as Washington D.C. Henceforth, all thought and action should be focused on how to get rid of the whole kit and kaboodle. There ain’t nuthin’ about any of it worth saving. Scrape it out to the walls. Knock out all the windows and doors. Air it out. The only two things about U.S. Government worth saving are 1. The Declaration of Independence and, 2. The Constitution of The United States of America. All other appurtenances of executive and/or bureaucratic power have outlived their usefulness. Time to clean house.
America has become like a potato.
The best part of it is underground.
Oh please don’t mention 🥔 potato! Leave him on his 🌴 island vacation.
Sundance,
👉🏻INSTALlING👈
Obama
?
An important thing to know is how a Govt Contract “works”.
The Contracting Officer “owns” the Contract. The COR (Contracting Officer’s Representative) executes the Contract.
Both of them keep extensive files on communications, changes, agreements, performance evaluations, etc.
If the Contract is above a certain dollar amount and issued by the DoD or affiliate, and is a multi year contract, then oftentimes DCMA oversees the contract. ( Defense Contract Management Agency). Many times, a “Task Order” for a specific event is executed under a larger Umbrella contract with a Defense Contractor. It isn’t a “new” contract, just an addendum to an existing contract, like with General Dynamics. It could be “Task Order 1A115.250” under the F-16 delivery contract. They hide this stuff if they want to do so.
These are the organizations and people who can be subpoenaed for their records. All of the records are available after the contract has concluded, unless tagged as Secret, Top Secret, or Top Secret Compartmentalized Information. But even those can be accessed by a Congressman or Senator with adequate Clearance.
The Records are key to understanding exactly what happened. There are so many Change Orders, Justifications, and CYA actions in a Contract as to make you dizzy. Anyone who hasn’t done this is clueless about how much documentation exists in a Contract File.
Sometimes, task orders are buried even deeper using IDFT (Interdepartmental Funds Transfers) to pay for them, and further on, the titles of the task orders are obscured: “Digital analysis of choices made under periodic events” (aka : Identify voter choices during election cycles).
You almost have to be a little bit cynical or crazy to understand how many things are hidden, funded, and executed, to understand how this stuff gets accomplished. But it does, every day.
The contract numbers themselves are classified now.
And “We the People” pay their salaries.
“And though the forest was shrinking, the trees kept voting for the axe, for the axe was clever and convinced the trees that since her handle was made of wood, she was one of them.”…
The cynically named Patriot Act was, from the outset, un-American and un-constitutional.
As usual, just stellar. Sundance lays it all out, again. Quick query though; wasn’t Richard Reid the reason for this- “The new definition of American citizens being threats to the national security state is ultimately what led to our taking off shoes at TSA checkpoints in airports” ?
Richard Reid was merely incidental. Example: If you recall the Uvalde, Tx school shooting on May 24, 2022, in which LEO did NOTHING to stop the shootings, somehow led to Turtle McConnell and Senator Cornyn, R – TX, to champion and pass more federal, unconstitutional gun control legislation. The shooting was just an excuse to do what .Gov already wanted – more unconstitutional gun control against law abiding Americans.
Considering Uvalde, TX LEO initially lied to TX Governor Abbot about the LEO response on May 24, I do wonder what it is Texas is trying to hide, though.
Namaste, my Guru.
Master class in real life.
Hussein describes his 3rd term dream: “And I used to say, ‘You know what, if I could make an arrangement where I had a stand-in, a front man or a front woman and they had an earpiece in and I was just in my basement with my sweats looking through the stuff, and I could sort of deliver the lines, but somebody else was doing all the talking and ceremony, I would be fine with that,’” he said.
https://www.welldoitlive.com/barack-obama-says-he-wishes-he-could-have-third-term-with-a-stand-in/
Arrogance! Sin is boastful.
IF you do not see the top of this image it says “WHAT IF I TOLD YOU”…
[Doofus Reminder HERE]
YouTube vid is no longer available.
There is a movie…The Matrix. Start there about if I told you.
I have warned everyone here before that you can’t stamp out the deep state very easily. There are maybe 10,00o industry spies for every spy that is employed by the US government. Then you have the 5-eyes, and all the other eyes, that will willingly spy on Americans.
Evil-doer Ray Epps
Dinesh D’Souza
@DineshDSouza
On January 6, 2021 Ray Epps texted his nephew to say, “I WAS IN THE FRONT WITH A FEW OTHERS. I ALSO ORCHESTRATED IT.” See the relevant section and also link to full transcript below
Tweets by TheLastRefuge2
Oops!
At thelastrefuge2
Scroll down to:
Dinesh D’Souza Tweet
Welcome to the Grand illusion
Come on in and see what’s happening
Pay the price, get your tickets for the show
The stage is set, the band starts playing
Suddenly your heart is pounding
Wishing secretly you were a star
But don’t be fooled by the radio
The TV or the magazines
They show you photographs of how your life should be
But they’re just someone else’s fantasy
So if you think your life is complete confusion
Because you never win the game
Just remember that it’s a grand illusion
And deep inside we’re all the same
We’re all the same
So if you think your life is complete confusion
Because your neighbors got it made
Just remember that it’s a grand illusion
And deep inside we’re all the same
America spells competition, join us in our blind ambition
Get yourself a brand new motor car
Someday soon we’ll stop to ponder what on earth’s this spell we’re under
We made the grade and still we wonder who the hell we are
Ask Philip Haney how the DOJ and DHS (of which he was a founding member) was weaponized from the top down against him…… but our dear brother died before he could publish his second book exposing the deceivers and betrayers in our Government.
Just a quick note on General Dynamics.
They are a very effective, proven PRIME GOVERNMENT Contractor, which most US Social media Companies and Big Tech Companies ARE NOT, when it comes to doing government work.
General Dynamics is also a very effective builder of contractor TEAMS, involving US Big Tech Companies (Microsoft, HP, SAP, IBM, Wind River and many others). Their C4I business unit has also bought and integrated allot of smaller high tech inovators.
When looking at anything they are leading … there is allot more under the surface than GD Assets doing technical work.
GD also has allot of experience dealing with the likes of Amazon from their logistics work.
The Terms and Conditions for this contract would be of great interest because that is where reporting, oversight and applicable FARR’s are listed.
Lockheed and Northrop-Grumman are also major Government PRIME Contractors with a “Data Systems and Communications” Division that would hold similar contracts.
I would list Raytheon-UT as they also have experience but they suck as Prime Contractors and have a long way to go when it comes to being a major league prime contractor, in the same league a GD, Lockheed and Northrop.
UTC – Sikorsky (now part of Lockheed, many military helicopters), Pratt And Whitney (now part of Raytheon) (F-22 Raptor and F-16 Falcon engines for example)
Is that not major league? How does UTC suck? Are they difficult to deal with? What’s your beef?
Not being antagonistic. Inform us.
Ah..you do read your own posts don’t you???
The parts of Ut that went to Raytheon are part makers and NOT major primes.
I DID cite Lockheed as a major successful prime.
So, what did a get wrong???
UTC NO LONGER exists as a company.
Sundance, I’ve read this basic story several times and appreciate it immensely. Might I suggest an expansion that traces the IC into the places of influencers such as Hollywood studios, media companies, podcasts, streaming movies and shows, video games and politics. I know numerous congressional candidates have come for IC. Will Hurd was former CIA. This isn’t contained to just NY Times, CNN, Wash Post, NBC, etc. It is pervasive propaganda. Look at how many movies and shows depict FBI and CIA as guardians of freedom and near superheros.
Great Point.
Look at the long stream of credits at the end of these movies for names and agencies that “provided technical advice and subject matter expertise.”
The use of US Government Employees and Agencies goes back to WWII and Depression era movies.
The 4th Amendment has been cancelled … due to EMERGENCY!!! … which Bidinh will keep extending to seize even MORE power in his final two years
People provide the intel being used against them willingly- social media is the greatest weapon our government created and they have had AI learning, cataloguing and tagging everything publicly shared on it since its launch. No warrants needed.
A small piece of history: https://www.fedscoop.com/ibm-watsons-role-federal-government/
For my treeper friends that Still Insist that there are “good” Republicans that are worthy of our money, our time or our votes.
I would remind them about the CORRUPT Senate Republicans choice to deny PRESIDENT TRUMP the chance to make ANY recess appointments in his entire four year term.
That single strategy by the ENTIRE CORRUPT GOPe left the ONLY man in Washington who was actually fighting for Americas survival all alone in his battles with the swamp on OUR behalf!
We sent him there only to find out later that the poor guy was truly alone!
I blame every single member of the corrupt Republican caucus for the persecution PRESIDENT TRUMP had to endure then, and all the unfair attacks he is still suffering from to this very day!
That’s why I believe the GOPe is too corrupt to be salvaged.
THAT’S WHY WE NEED TO START A MAGA PARTY!
“For their own self-preservation, the Intelligence Branch has been interfering in our elections for years. The way to tear this apart begins with STATE LEVEL election reform”
Not election reform, those States that want a rebirth of the United States of America need to acknowledge that the nation formerly known as the United States of America no longer exists.
I propose the peaceful solution of declaring themselves to be the Original United States of America with the original Constitution and Declaration of Independence. They can start over with a clean slate.
NDAA and the Patriot Act is nothing more than an assault on our Constitutional Republic. Now Americans have an unelected, fourth pillar of our republic, unaccountable to anybody, without any means of oversight to avoid abuse and unchecked power.
The patriot act needs to be defunded. Clearly, there needs to be public monitoring and oversight of all government activities.
Absolute must reading ….
This is massive. The infiltration is so deep it seems almost hopeless, at least to use or go through this corrupt system that has been installed at state levels to attempt to save our Republic. The seemingly endless time it would take will give the enemy enough time as well to complete its take over. Like we know where the finish line is and what we have to do, but we are turtles slow walking against rabbits that have had many years in advance of this to install multiple road blocks and dead ends. I dont think we have the time to do the slow walk through state reforms of all that needs to be done. Seems more like we need some type of air assault to shock the enemy and put them back on their heels, where we then can make the land assault and make positive moves forward. We ARE in a war…and maybe that’s the way we should be approaching it. We are in a fight against a terrible beast, not even just in this country. But we need to focus here. This is known by DJT. And I also believe there is a strong arm behind that knowing. Something big is coming that will set them back on their butts and allow massive gains for us. The biggest part of this was…is the awakening of the masses to what has been going on. Their biggest fear is us…the masses knowing and being aware of their agenda and us coming together as one against them! That IS growing! I sure do not want a civil war, but we can’t be afraid to go there if that’s the call! Let’s hope and pray it is not.
The “dufus video” has been made unavailable on YouTube.
Thank you, SD, for reposting, and adding to this continually developing exposure of the truth. My husband and I followed your steps closely during your field trip to and through locked-down D.C.
As horrifying as the your revelations, and now others’ revelations, have been these last several years, it is always better to know, than not to know, the identity and nature of the players in the 21st C grand, deliberately obfuscated design for our Nation and for our very lives.
Even as you were feverishly escorting us through the connecting tunnels, we did not imagine that our very system of elections would be seized, manipulated, controlled, and denied exposure of the truth in a Court of Law – writ large. In my estimation, the loss of the Judiciary to the control of the 4th Branch and deep pocketed interests is the gravest loss of all.
I will print this piece to use as “hand-outs” locally, and send it out electronically to loved ones and friends who continue to shy away from learning and accepting the harsh realities that we, ourselves, have allowed to take root inside our federal, state, and local levels of government, all upon the foundation of cash, political support, lies, and a faked blind eye from “both” major political Parties.
Thank you – every, single day.
Fully explains why Bitch McConnell withheld millions of Trump generated PAC cash from the Senate races in AK, AZ, NH, and NV. Fvckers.
Their fear and control campaign over hard-working , and also uninformed, aka unaware citizens is underway.
Pray to rid ourselves of such madness and cruelty!
Well, at least this happened before GDIT acquired CSRA. There has been so many sub entities bought and sold between the IT corporations (DC metro area) that it would be difficult to tell which tech company is supporting the DHS enterprises now.
In most cases tech groups end up doing the same jobs, just different management. And to help thwart any tracing, government (DHS) program contractors must now be divided out to small businesses.
I think you could use this bit of encouragement; a good read: HOPE FOR THE FUTURE!!!! 🙂
[…Let’s sum this up.
1. We don’t need to worry about the threat of one-world government. It’s already here. We need to start fighting it.
2. The central planning planners can’t plan diddly squat, because central planning doesn’t work.
3. Lots of people trust the planners less than than they trust Nigerian princes.
4. It only takes ONE PERSON — for example, a Whitaker Chambers — to start unraveling one-world government.
5. We have LOTS of good people.
6. The momentum is on our side. Especially locally.
The good news is: most of us have zero control over what happens outside our local area. That’s good news because we don’t have to worry about the insane asylums called Washington, D.C., London, Brussels, or Moscow. That’s not our job.
Our job is local, local, local. Keep the pressure on! It’s working.]…See more:
https://www.coffeeandcovid.com/p/a-great-big-new-year-saturday-december
If you’re on social media sites, get off all of them, they serve absolutely no purpose other than to “inform” on people. It’s appalling how many people will get on those sites and just spill their guts. Incredibly stupid, and you know, people CAN survive without all that crap. No one cares what color socks you’re wearing today, really they don’t!
A lot more information is garnered by those sites than people realize. I wouldn’t go to any of them for all the tea in taiwan. What a horrid waste of time.
With their massive big data collection, they can’t stop mass shooters before they become active shooters?
Maybe that’s not their focus.