This is very weedy but also very interesting to me, perhaps you. Completely unrelated to my own years of research into “Jack’s Magic Coffee Shop,” aka Twitter, and the intelligence community use of the platform to shape public opinion, another research group has looked at the tentacles & data points and come to the exact same conclusion.
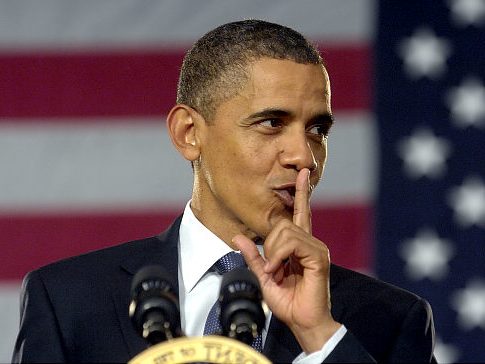 For years CTH has outlined how the Obama administration leveraged social media networks as part of a larger objective to shape public opinion, ultimately leading to the shaping of U.S. elections.
For years CTH has outlined how the Obama administration leveraged social media networks as part of a larger objective to shape public opinion, ultimately leading to the shaping of U.S. elections.
It’s a long arc of modern assembly, but the bottom line reached by EDIFY, an independent research group, is that the ‘Arab Spring’ was the beta test for deploying the same system to shape U.S. elections.
Remarkably, that is the exact same conclusion reached by CTH several years ago as highlighted in the story of how Obama shifted the mission of new agencies (ODNI, DHS, DOJ-NSD) and assembled the fourth branch of government.
Writing in his Substack [SEE HERE], Dr Robert Malone draws attention to the EDIFY research.
EDIFY – […] “”At the time, Egyptians and Tunisians were rising up, facilitated by technology, in what the media dubbed a Twitter Revolution. “It was a no-brainer for me, because I wanted to be part of a company that was really dramatically changing the world,” Gadde says. She credits her boss at Juniper, General Counsel Mitchell Gaynor, for being supportive.” – NYU Law Magazine [1]
What are the chances that then President Obama did nothing to promote and ensure success for the Arab Spring because its true purpose was to serve as a beta-test for the use of the Twitter platform in future censorship and color revolution applications in the U.S.?
The application of Occam’s reveals that this is likely the case and Vadde’s testimony here is evidence suggestive of this position.
WSGR product and central node Alex Macgillivray threads the Obama and Biden White Houses together. Macgillivray currently serves as the Biden White House CTO. Macgillivray appointed WSGR product Gadde to be his successor at Twitter and whereby Gadde was central both to the de-platforming of then President Trump and the censorship of the Hunter Biden laptop affair. It further aggravates the position on Twitter relative to engagement in color revolutions.
At the time, President Obama said this,
“The United States has supported the forces of change.” – President Obama [2]
Obama did not say that he supported the countries of change but rather the forces of change; citing the countries as “inspiration”.
Those are carefully constructed statements with specific word choice and when discernment is applied, we understand the “forces of change” to be digital ones, like Twitter. This comports with the Arab Spring being a Twitter Beta test. The same general people are now positioned to serve the Biden Administration on the follow-through. (read more)
Yes. A million-fold YES.
We cannot fight our way through the issues until we first realize what lies at the root of the problem.

Barack Obama and Eric Holder did not create a weaponized DOJ and FBI; the institutions were already weaponized by the Patriot Act. What Obama and Holder did was take the preexisting system and retool it, so the weapons of government only targeted one side of the political continuum.
This point is where many people understandably get confused.
Elevator Speech:
(1) The Patriot Act turned the intel surveillance radar from foreign searches for terrorists to domestic searches for terrorists.
(2) Obama/Biden then redefined what is a “terrorist” to include their political opposition.
DEEP DIVE:
In the era shortly after 9/11 the DC national security apparatus, instructed by Vice President Dick Cheney, was constructed to preserve continuity of government and simultaneously view all Americans as potential threats. The Department of Homeland Security (DHS) and the Office of the Director of National Intelligence (ODNI) were created specifically for this purpose.
After 9/11/01 the electronic surveillance system that was originally created to monitor threats from abroad was retooled to monitor threats inside our country. That is when all of our electronic ‘metadata’ came under federal surveillance.
That inflection point, and the process that followed, was exactly what Edward Snowden tried to point out.
What Barack Obama and Eric Holder did with that new construct was refine the internal targeting mechanisms so that only their political opposition became the target of this new national security system.
The problems we face now as a country are directly an outcome of two very distinct points that were merged by Barack Obama. (1) The post 9/11 monitoring of electronic communication of American citizens; and (2) Obama’s team creating a fine-tuning knob that it focused on the politics of the targets. This is very important to understand as you dig deeper into this research outline.
Washington DC created the modern national security apparatus immediately and hurriedly after 9/11/01. The Department of Homeland Security came along in 2002, and within the Intelligence Reform and Terrorism Prevention Act of 2004 the Office of the Director of National Intelligence (ODNI) was formed.
When President Barack Obama and Attorney General Eric Holder arrived a few years later, those newly formed institutions were viewed as opportunities to create a very specific national security apparatus that would focus almost exclusively against their political opposition.
The preexisting Federal Bureau of Investigation (FBI) and Dept of Justice (DOJ) were then repurposed to become two of the four pillars of the domestic national security apparatus: a domestic surveillance state. However, this new construct would have a targeting mechanism based on political ideology.
The DHS, ODNI, DOJ and FBI became the four pillars of this new institution. Atop these pillars is where you will find the Fourth Branch of Government.
We were not sleeping when this happened, we were wide awake. However, we were stunningly distracted by the economic collapse that was taking place in 2006 and 2007 when the engineers behind Obama started to assemble the design. By the time Obama took office in 2009, we sensed something profound was shifting, but we can only see exactly what shifted in the aftermath. The four pillars were put into place, and a new Fourth Branch of Government was quietly created.
As time passed, and the system operators became familiar with their new tools, technology allowed the tentacles of the system to reach out and touch us. That is when we first started to notice that something very disconcerting was happening. Those four pillars are the root of it, and if we take the time to understand how the Fourth Branch originated, questions about this current state of perpetual angst will start to make sense.

Remember, it is not my intent to outline the entire history of how we got to this place where the intelligence community now acts as the superseding Fourth Branch of Government. Such an effort would be exhausting and likely take our discussion away from understanding the current dynamic.
History provided enough warnings from Dwight D. Eisenhower (military) to John F. Kennedy (CIA), to Richard Nixon (FBI), to all the modern versions of warnings and frustrations from HPSCI Devin Nunes and ODNI Ric Grenell.
None of those prior reference points are invalid, and all documented outlines of historic reference are likely true and accurate. However, a generational review is not useful, as the reference impacting us ‘right now‘ gets lost.
Instead, we pick up the expansive and weaponized intelligence system as it manifests after 9/11/01, and my goal is to highlight how the modern version of the total intelligence apparatus has metastasized into a Fourth Branch of Government. It is this superseding branch that now touches and influences every facet of our life. We The People are under surveillance.
If we take the modern construct, originating at the speed of technological change, we can also see how the oversight or “check/balance” in our system of government became functionally obsolescent.
After many years of granular research about the intelligence apparatus inside our government, in the summer of 2020 I visited Washington DC to ask specific questions. My goal was to go where the influence agents within government actually operate, and to discover the people deep inside the institutions no one elected, and few people pay attention to.
 It was during this process when I discovered how information is purposefully put into containment silos; essentially a formal process to block the flow of information between agencies and between the original branches. While frustrating to discover, the silo effect was important because understanding the communication between networks leads to our ability to reconcile conflict between what we perceive and what’s actually taking place.
It was during this process when I discovered how information is purposefully put into containment silos; essentially a formal process to block the flow of information between agencies and between the original branches. While frustrating to discover, the silo effect was important because understanding the communication between networks leads to our ability to reconcile conflict between what we perceive and what’s actually taking place.
After days of research and meetings in DC during 2020; amid a town that was serendipitously shut down due to COVID-19; I found a letter slid under the door of my room in a nearly empty hotel with an introduction of sorts. The subsequent discussions were perhaps the most important. After many hours of specific questions and answers on specific examples, I realized why our nation is in this mess. That is when I discovered the fourth and superseding branch of government, the Intelligence Branch.
I am going to explain how the Intelligence Branch works: (1) to control every other branch of government; (2) how it functions as an entirely independent branch of government with no oversight; (3) how and why it was created to be independent from oversight; (4) what is the current mission of the IC Branch, and most importantly (5) who operates it.
The Intelligence Branch is an independent functioning branch of government, it is no longer a subsidiary set of agencies within the Executive Branch as most would think. To understand the Intelligence Branch, we need to drop the elementary school civics class lessons about three coequal branches of government and replace that outlook with the modern system that created itself.
The Intelligence Branch functions much like the State Dept, through a unique set of public-private partnerships that support it. Big Tech industry collaboration with intelligence operatives is part of that functioning, almost like an NGO. However, the process is much more important than most think. In this problematic perspective of a corrupt system of government, the process is the flaw – not the outcome.
There are people making decisions inside this little known, unregulated and out-of-control branch of government that impact every facet of our lives.
None of the people operating deep inside the Intelligence Branch were elected; and our elected representative House members genuinely do not know how the system works. I assert this position affirmatively because I have talked to House and Senate staffers, including the chiefs of staff for multiple House & Senate committee seats. They are not malicious people; however, they are genuinely clueless of things that happen outside their silo. That is part of the purpose of me explaining it, with examples, in full detail with sunlight.
We begin….
In April of 2016, the FBI launched a counterintelligence operation against presidential candidate Donald Trump. The questioning about that operation is what New York Representative Elise Stefanik cites in March of 2017, approximately 11 months later (First Two Minutes).
Things to note:
♦ Notice how FBI Director James Comey just matter-of-factly explains no one outside the DOJ was informed about the FBI operation. Why? Because that’s just the way things are done. His justification for unilateral operations was “because of the sensitivity of the matter“, totally ignoring any constitutional or regulatory framework for oversight; because, well, quite simply, there isn’t any. The intelligence apparatus inside the DOJ/FBI can, and does, operate based on their own independent determinations of authority.
♦ Notice also how FBI Director Comey shares his perspective that informing the National Security Council (NSC) is the equivalent of notifying the White House. The FBI leadership expressly believe they bear no responsibility to brief the Chief Executive. As long as they tell some unknown, unelected, bureaucratic entity inside the NSC, their unwritten responsibility to inform the top of their institutional silo is complete. If the IC wants to carve out the Oval Office, they simply plant information inside the NSC and, from their perspective, their civic responsibility to follow checks-and-balances is complete. This is an intentional construct.
♦ Notice how Comey obfuscates notification to the Director of National Intelligence (DNI), by avoiding the fact James Clapper was the DNI from outset of the counterintelligence operation throughout the remainder of Obama’s term. When I get deeper into the process, we will understand how the Intelligence Branch has intentionally used the creation of the DNI position (established post 9/11/01) as a method to avoid oversight, not enhance it. Keeping an oblivious doofus like James Clapper in position held strategic value [Doofus Reminder HERE].
That video of James Comey being questioned by Elise Stefanik was the first example given to me by someone who knew the background of everything that was taking place preceding that March 20, 2017, hearing. That FBI reference point is a key to understand how the Intelligence Branch operates with unilateral authority above Congress (legislative branch), above the White House (executive branch), and even above the court system (judicial branch).
Also, watch this short video of James Clapper, because it is likely many readers have forgotten, and likely even more readers have never seen it. Watch closely how then White House national security adviser John Brennan is responding in that video. This is before Brennan became CIA Director, this is when Brennan was helping Barack Obama put the pillars into place. WATCH:
[Sidebar: Every time I post this video it gets scrubbed from YouTube (example), so save it if you ever want to see it again.]
The video of James Clapper highlights how the ODNI position (created with good national security intention) ended up becoming the fulcrum for modern weaponization, and is now an office manipulated by agencies with a vested interest in retaining power. The Intelligence Branch holds power over the ODNI through their influence and partnership with the body that authorizes the power within it, the Senate Select Committee on Intelligence (SSCI).
Factually, the modern intelligence apparatus uses checks and balances in their favor. The checks create silos of proprietary information, classified information, vaults of information that work around oversight issues. The silos, which include the exploitation of the Foreign Intelligence Surveillance Court (FISA Court, or FISC) are part of the problem.
Ironically, the Office of the Director of National Intelligence was created in the aftermath of 9/11/01 expressly to eliminate the silos of information which they felt led to a domestic terrorist attack that could have been prevented. The ODNI was created specifically upon the recommendation of the 9/11 commission.
The intent was to create a central hub of intelligence information, inside the Executive Branch, where the CIA, NSA, DoD, DoS, and DIA could deposit their unique intelligence products and a repository would be created so that domestic intelligence operations, like the DOJ and FBI could access them when needed to analyze threats to the U.S. This, they hoped, would ensure the obvious flags missed in the 9/11 attacks would not be missed again.
However, the creation of the DNI office also created an unconstitutional surveillance system of the American people. The DNI office became the tool to take massive amounts of data and use it to target specific Americans. Weaponizing the DNI office for political targeting is now the purpose of the DNI office as it exists.
The illegal and unlawful nature of the surveillance creates a need for careful protection amid the group who operate in the shadows of electronic information and domestic surveillance. You will see how it was critical to install a person uniquely skilled in being an idiot, James Clapper, into that willfully blind role while intelligence operatives worked around the office to assemble the Intelligence Branch of Government.
• The last federal budget that flowed through the traditional budgetary process was signed into law in September of 2007 for fiscal year 2008 by George W. Bush. Every budget since then has been a fragmented process of continuing resolutions and individual spending bills.
Why does this matter? Because many people think defunding the Intelligence Community is a solution; it is not…. at least, not yet. Worse yet, the corrupt divisions deep inside the U.S. intelligence system can now fund themselves from multinational private sector partnerships (banks, corporations and foreign entities).
• When Democrats took over the House of Representatives in January 2007, they took office with a plan. Nancy Pelosi became Speaker, and Democrats controlled the Senate where Harry Reid was Majority Leader. Barack Obama was a junior senator from Illinois.
Pelosi and Reid intentionally did not advance a budget in 2008 (for fiscal year 2009) because their plan included installing Barack Obama (and all that came with him) with an open checkbook made even more lucrative by a worsening financial crisis and a process called baseline budgeting. Baseline budgeting means the prior fiscal year budget is accepted as the starting point for the next year budget. All previous expenditures are baked into the cake within baseline budgeting.
Massive bailouts preceded Obama’s installation due to U.S. economic collapse, and massive bailouts continued after his installation. This is the ‘never let a crisis go to waste’ aspect. TARP (Troubled Asset Recovery Program), auto bailouts (GM), and the massive stimulus spending bill, the American Recovery and Reinvestment Act (ARRA, ie. those shovel ready jobs) were all part of the non-budget spending. The federal reserve assisted with Quantitative Easing (QE1 and QE2) as congress passed various Porkulous spending bills further spending and replacing the formal budget process.
Note: There has never been a budget passed in the normal/traditional process since September of 2007.
• While Obama’s radical ‘transformation‘ was triggered across a broad range of government institutions, simultaneously spending on the U.S. military was cut, but spending on the intelligence apparatus expanded. We were all distracted by Obamacare, and the Republican Party wanted to keep us that way. However, in the background there was a process of transformation taking place that included very specific action by Eric Holder and targeted effort toward the newest executive agency the ODNI.
 The people behind Obama, those same people now behind Joe Biden, knew from years of strategic planning that ‘radical transformation’ would require control over specific elements inside the U.S. government. Eric Holder played a key role in his position as U.S. Attorney General in the DOJ.
The people behind Obama, those same people now behind Joe Biden, knew from years of strategic planning that ‘radical transformation’ would require control over specific elements inside the U.S. government. Eric Holder played a key role in his position as U.S. Attorney General in the DOJ.
AG Holder recruited ideologically aligned political operatives who were aware of the larger institutional objectives. One of those objectives was weaponizing the DOJ-National Security Division (DOJ-NSD) a division inside the DOJ that had no inspector general oversight. For most people the DOJ-NSD weaponization surfaced with a hindsight awakening of the DOJ-NSD targeting candidate Donald Trump many years later. However, by then the Holder crew had executed almost eight full years of background work.
• The second larger Obama/Holder objective was control over the FBI. Why was that important? Because the FBI does the domestic investigative work on anyone who needs or holds a security clearance. The removal of security clearances could be used as a filter to further build the internal ideological army they were assembling. Additionally, with new power in the ODNI created as a downstream consequence of the Patriot Act, new protocols for U.S. security clearances were easy to justify.
Carefully selecting fellow ideological travelers was facilitated by this filtration within the security clearance process. How does that issue later manifest? Just look around at how politicized every intelligence agency has become, specifically including the FBI.
• At the exact same time this new background security clearance process was ongoing, again everyone distracted by the fight over Obamacare, inside the Department of State (Secretary Hillary Clinton) a political alignment making room for the next phase was being assembled. Names like Samantha Power, Susan Rice and Hillary Clinton were familiar on television while Lisa Monaco worked as a legal liaison between the Obama White House and Clinton State Department.
Through the Dept of State (DoS) the intelligence apparatus began working on their first steps to align Big Tech with a larger domestic institutional objective. Those of you who remember the “Arab Spring”, some say “Islamist Spring”, will remember it was triggered by Barack Obama’s speech in Cairo – his first foreign trip. The State Department worked with grassroots organizers (mostly Muslim Brotherhood) in Egypt, Syria, Bahrain, Qatar and Libya. Obama leaned heavily on the organizational network of Turkish President Recep Erdogan for contacts and support.
Why does this aspect matter to us? Well, you might remember how much effort the Obama administration put into recruiting Facebook and Twitter as resources for the various mideast rebellions the White House and DoS supported. This was the point of modern merge between the U.S. intelligence community and Big Tech social media.
In many ways, the coordinated political outcomes in Libya and Egypt were the beta test for the coordinated domestic political outcomes we saw in the 2020 U.S. presidential election. The U.S. intelligence community working with social media platforms and political operatives.
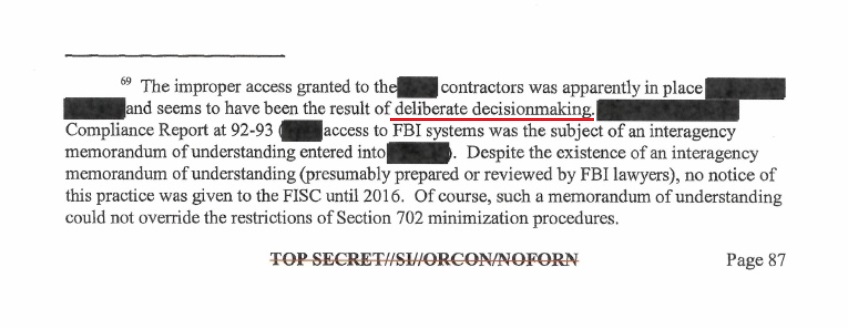
Overlaying all of that background activity was also a new alignment of the Obama-era intelligence apparatus with ideological federal “contractors“. Where does this contractor activity manifest? In the FISA Court opinion of Rosemary Collyer who cited the “interagency memorandum of understanding”, or MOU.
Hopefully, you can see a small part of how tentacled the system to organize/weaponize the intelligence apparatus was. None of this was accidental, all of this was by design, and the United States Senate was responsible for intentionally allowing most of this to take place. The tools the government used to monitor threats were now being used to monitor every American. WE THE PEOPLE were now the threat the national security system was monitoring.
That’s the 30,000/ft level backdrop history of what was happening as the modern IC was created. Next, we will go into how all these various intelligence networks began working in unison and how they currently control all of the other DC institutions under them; including how they can carve out the President from knowing their activity.
♦ When Barack Obama was installed in January 2009, the Democrats held a 60-seat majority in the U.S. Senate. As the people behind the Obama installation began executing their longer-term plan, the Senate Select Committee on Intelligence was a tool to create the Intelligence Branch; it was not an unintentional series of events.
When Obama was installed, Dianne Feinstein was the Chair of the Senate Select Committee on Intelligence (SSCI), and Democrat operative Dan Jones was her lead staffer. Feinstein was completely controlled by those around her including Senate Majority Leader Harry Reid. The CIA was in the process of turning over personnel following the Bush era, and as a result of a massive multi-year narrative of diminished credibility (Iraq WMD), a deep purge was underway. Obama/Holder were in the process of shifting intelligence alignment and the intensely political Democrat Leader Harry Reid was a key participant.
 THE TRAP – Many people say that Congress is the solution to eliminating the Fourth and superseding Branch of Government, the Intelligence Branch. This is an exercise in futility because the Legislative Branch, specifically the SSCI, facilitated the creation of the Intelligence Branch. The SSCI cannot put the genie they created back in the bottle without admitting they too are corrupt; and the background story of their corruption is way too intense to be exposed now.
THE TRAP – Many people say that Congress is the solution to eliminating the Fourth and superseding Branch of Government, the Intelligence Branch. This is an exercise in futility because the Legislative Branch, specifically the SSCI, facilitated the creation of the Intelligence Branch. The SSCI cannot put the genie they created back in the bottle without admitting they too are corrupt; and the background story of their corruption is way too intense to be exposed now.
Every member of the SSCI is compromised in some controlling manner. Those Senators who disliked the control over them; specifically disliked because the risk of sunlight was tenuous and, well, possible; have either left completely or stepped down from the committee. None of the SSCI members past or present would ever contemplate saying openly what their tenure involved.
[Note: You might remember when Vice Chairman Mark Warner’s text messages surfaced, there was a controlled Republican SSCI member who came to his defense in February of 2018. It was not accidental that exact Senator later became the chair of the SSCI himself. That Republican Senator is Marco Rubio, now vice-chair since the Senate re-flipped back to the optics of Democrat control in 2021.]
All of President Obama’s 2009 intelligence appointments required confirmation from the Senate. The nominees had to first pass through the Democrat controlled SSCI, and then to a full Senate vote where Democrats held a 60-vote majority. Essentially, Obama got everyone he wanted in place easily. Rahm Emmanuel was Obama’s Chief of Staff, and Valerie Jarrett was Senior Advisor.
 Tim Geithner was Treasury Secretary in 2010 when the joint DOJ/FBI and IRS operation to target the Tea Party took place after the midterm “shellacking” caused by the Obamacare backlash. Mitch McConnell was Minority Leader in the Senate but supported the targeting of the Tea Party as his Senate colleagues were getting primaried by an angry and effective grassroots campaign. McConnell’s friend, Senator Bob Bennett, getting beaten in Utah was the final straw.
Tim Geithner was Treasury Secretary in 2010 when the joint DOJ/FBI and IRS operation to target the Tea Party took place after the midterm “shellacking” caused by the Obamacare backlash. Mitch McConnell was Minority Leader in the Senate but supported the targeting of the Tea Party as his Senate colleagues were getting primaried by an angry and effective grassroots campaign. McConnell’s friend, Senator Bob Bennett, getting beaten in Utah was the final straw.
Dirty Harry and Mitch McConnell saw the TEA Party through the same prism. The TEA Party took Kennedy’s seat in Massachusetts (Scott Brown); Sharon Angle was about to take out Harry Reid in Nevada; Arlen Spector was taken down in Pennsylvania; Senator Robert Byrd died; Senator Lisa Murkowski lost her primary to Joe Miller in Alaska; McConnell’s nominee Mike Castle lost to Christine O’Donnell in Delaware; Rand Paul won in Kentucky. This is the background. The peasants were revolting…. and visibly angry Mitch McConnell desperately made a deal with the devil to protect himself.
In many ways, the TEA Party movement was/is very similar to the MAGA movement. The difference in 2010 was the absence of a head of the movement, in 2015 Donald Trump became that head figure who benefited from the TEA Party energy. Trump came into office in 2017 with the same congressional opposition as the successful TEA Party candidates in 2011.
Republicans took control of the Senate following the 2014 mid-terms. Republicans took control of the SSCI in January 2015. Senator Richard Burr became chairman of the SSCI, and Dianne Feinstein shifted to Vice-Chair. Dirty Harry Reid left the Senate, and Mitch McConnell took power again.
Republicans were in control of the Senate Intelligence Committee in 2015 when the Intelligence Branch operation against candidate Donald Trump was underway. [Feinstein’s staffer, Dan Jones, left the SSCI so he could act as a liaison and political operative between private-sector efforts (Fusion GPS, Chris Steele) and the SSCI.] The SSCI was a participant in that Fusion GPS/Chris Steele operation, and as a direct consequence Republicans were inherently tied to the problem with President Trump taking office in January of 2017. Indiana Republican Senator Dan Coats was a member of the SSCI.
Bottom line…. When it came to the intelligence system targeting Donald Trump during the 2015/2016 primary, the GOP was just as much at risk as their Democrat counterparts.
When Trump unexpectedly won the 2016 election, the SSCI was shocked more than most. They knew countermeasures would need to be deployed to protect themselves from any exposure of their prior intelligence conduct. Immediately Senator Dianne Feinstein stepped down from the SSCI, and Senator Mark Warner was elevated to Vice Chairman.
Indiana’s own Mike Pence, now Vice President, recommended fellow Hoosier, SSCI Senator Dan Coats, to become President Trump’s Director of National Intelligence (ODNI). [Apply hindsight here]
• To give an idea of the Intelligence Branch power dynamic, remind yourself how House Permanent Select Committee on Intelligence (HPSCI), Chairman Devin Nunes, tried to get access to the DOJ/FBI records of the FISA application used against the Trump campaign via Carter Page.
Remember, Devin Nunes only saw a portion of the FISA trail from his review of a Presidential Daily Brief (PDB) previously given to President Obama. Chairman Nunes had to review the PDB at the White House SCIF due to compartmented intelligence, another example of the silo benefit.
Remember the massive stonewalling and blocking of the DOJ/FBI toward Nunes? Remember the back-and-forth battle over declassification surrounding the Nunes memo?
Remember, after Nunes went directly to House Speaker Paul Ryan for help (didn’t get any), the DOJ only permitted two members from each party within the HPSCI to review the documents, and only at the DOJ offices of main justice?
Contrast that amount of House Intel Committee railroading by intelligence operatives in the DOJ, DOJ-NSD and FBI, with the simple request by Senate Intelligence Vice Chairman Mark Warner asking to see the Carter Page FISA application and immediately a copy being delivered to him on March 17th 2017.
Can you see which intelligence committee is aligned with the deepest part of the deep state?
Oh, how quickly we forget:
The contrast of ideological alignment between the House, Senate and Intelligence Branch is crystal clear when viewed through the prism of cooperation. You can see which legislative committee holds the power and support of the Intelligence Branch. The Senate Intel Committee facilitates the corrupt existence of the IC Branch, so the IC Branch only cooperates with the Senate Intel Committee. It really is that simple.
• The Intelligence Branch carefully selects its own members by controlling how security clearances are investigated and allowed (FBI). The Intelligence Branch also uses compartmentalization of intelligence as a way to keep each agency, and each downstream branch of government (executive, legislative and judicial), at arm’s length as a method to stop anyone from seeing the larger picture of their activity. I call this the “silo effect“, and it is done by design.
I have looked at stunned faces when I presented declassified silo product from one agency to the silo customers of another. You would be astonished at what they don’t know because it is not in their ‘silo’.
 Through the advice and consent rules, the Intelligence Branch uses the SSCI to keep out people they consider dangerous to their ongoing operations. Any appointee to the intelligence community must first pass through the Senate Select Committee on Intelligence, before they get a full Senate vote. If the SSCI rejects the candidate, they simply refuse to take up the nomination. The president is then blocked from that appointment. This is what happened with President Trump over and over again.
Through the advice and consent rules, the Intelligence Branch uses the SSCI to keep out people they consider dangerous to their ongoing operations. Any appointee to the intelligence community must first pass through the Senate Select Committee on Intelligence, before they get a full Senate vote. If the SSCI rejects the candidate, they simply refuse to take up the nomination. The president is then blocked from that appointment. This is what happened with President Trump over and over again.
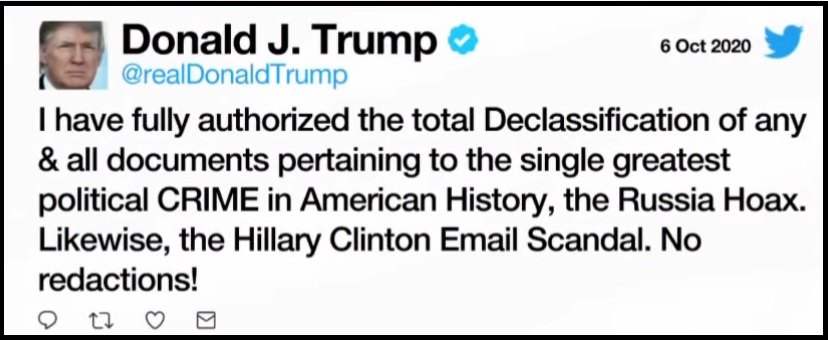
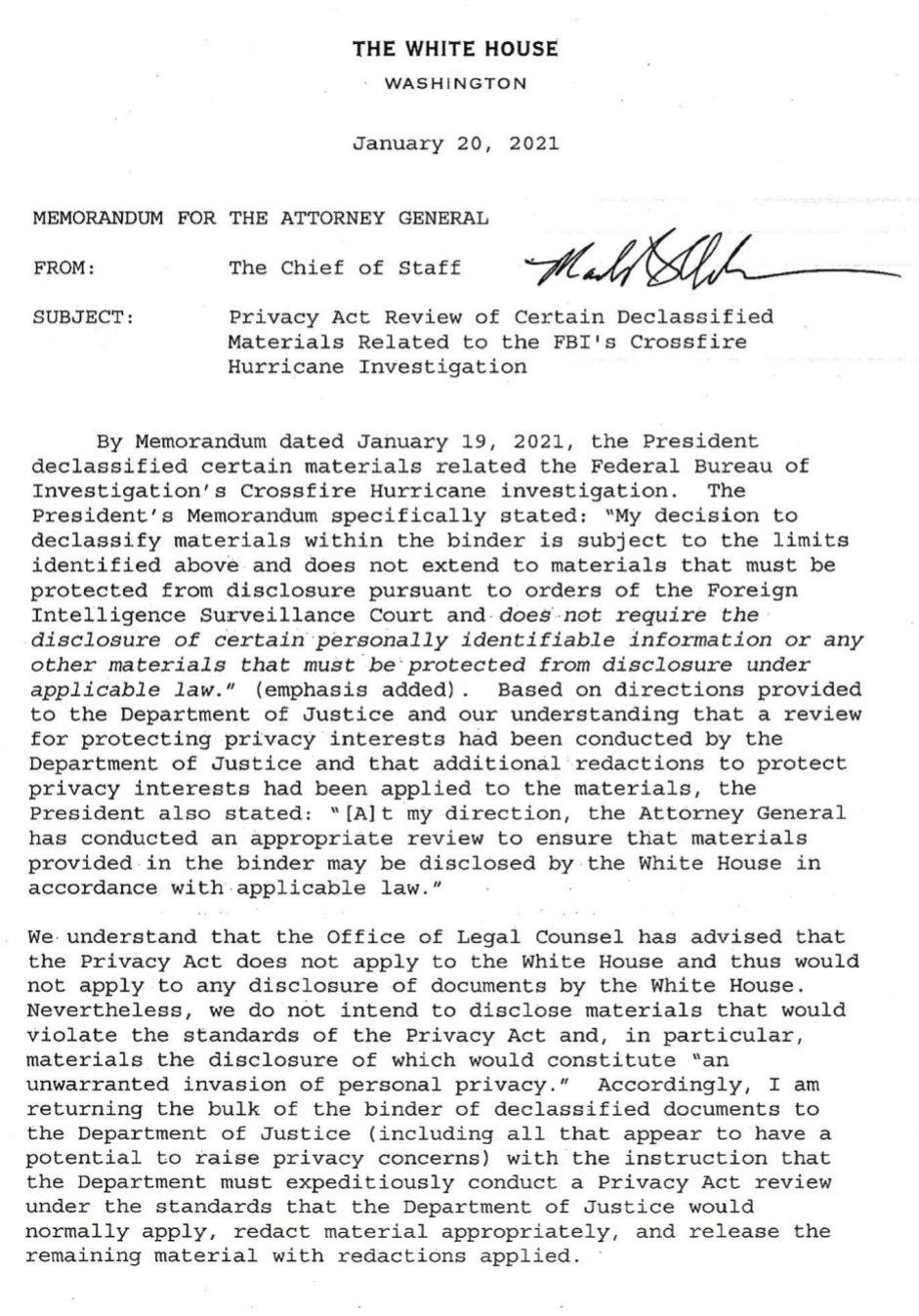
• Additionally, the Intelligence Branch protects itself, and its facilitating allies through the formal classification process. The Intelligence Branch gets to decide unilaterally what information will be released and what information will be kept secret. There is no entity outside the Intelligence Branch, and yes that includes the President of the United States, who can supersede the classification authority of the Intelligence Branch. {Go Deep} and {Go Deep} This is something 99.9% of the people on our side get totally and frustratingly wrong.
No one can declassify, or make public, anything the Intelligence Branch will not agree to. Doubt this? Ask Ric Grenell, John Ratcliffe, or even President Trump himself.
• The classification process is determined inside the Intelligence Branch, all by themselves. They get to choose what rank of classification exists on any work product they create; and they get to decide what the classification status is of any work product that is created by anyone else. The Intelligence Branch has full control over what is considered classified information and what is not. The Intelligence Branch defines what is a “national security interest” and what is not. A great technique for hiding fingerprints of corrupt and illegal activity.
[For familiar reference see the redactions to Lisa Page and Peter Strzok text messages. The Intelligence Branch does all redactions.]
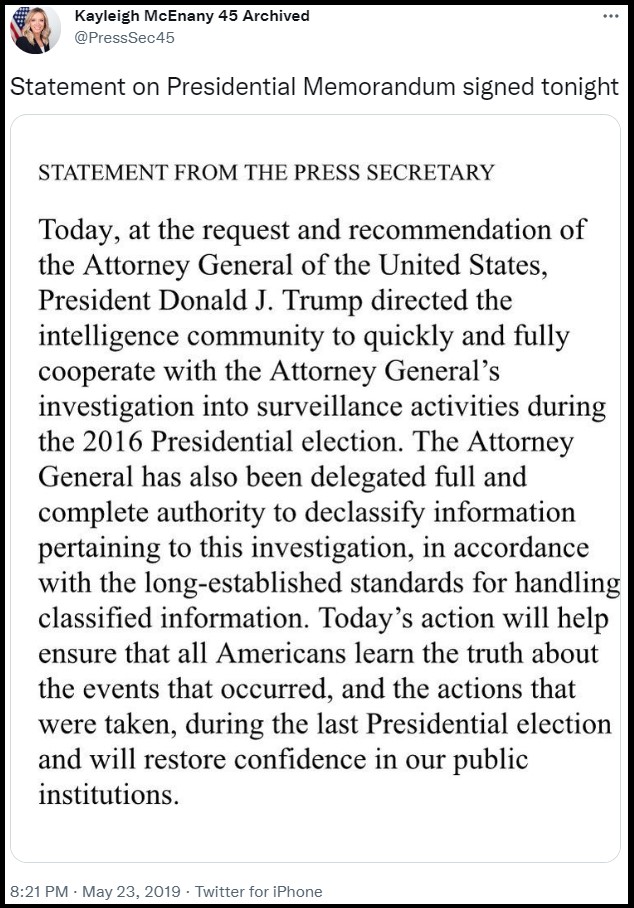 • Similarly, the declassification process is a request by an agency, even a traditionally superior agency like the President of the United States, to the Intelligence Branch asking for them to release the information. The Intelligence Branch again holds full unilateral control.
• Similarly, the declassification process is a request by an agency, even a traditionally superior agency like the President of the United States, to the Intelligence Branch asking for them to release the information. The Intelligence Branch again holds full unilateral control.
If the head of the CIA refuses to comply with the declassification instruction of the President, what can the president do except fire him/her? {Again, GO DEEP} How does the President replace the non-compliant cabinet member? They have to go through the SSCI confirmation. See the problem?
Yes, there are ways to break up the Intelligence Branch, but they do not start with any congressional effort. As you can see above, the process is the flaw – not the solution. Most conservative pundits have their emphasis on the wrong syllable. Their cornerstone is false.
For their own self-preservation, the Intelligence Branch has been interfering in our elections for years. The way to tear this apart begins with STATE LEVEL election reform that blocks the Legislative Branch from coordinating with the Intelligence Branch.
The extreme federalism approach is critical and also explains why Joe Biden has instructed Attorney General Merrick Garland to use the full power of the DOJ to stop state level election reform efforts. The worry of successful state level election control is also why the Intelligence Branch now needs to support the federal takeover of elections.
Our elections have been usurped by the Intelligence Branch. Start with honest elections and we will see just how much Democrat AND Republican corruption is dependent on manipulated election results. Start at the state level. Start there…. everything else is downstream.
♦ COLLAPSED OVERSIGHT – The modern system to ‘check’ the Executive Branch was the creation of the legislative “Gang of Eight,” a legislative oversight mechanism intended to provide a bridge of oversight between the authority of the intelligence community within the Executive Branch.
The Go8 construct was designed to allow the President authority to carry out intelligence operations and provide the most sensitive notifications to a select group within Congress.
The Go8 oversight is directed to the position, not the person, and consists of: (1) The Speaker of the House; (2) The Minority Leader of the House; (3) The Chair of the House Permanent Select Committee on Intelligence, HPSCI; (4) The Ranking Member (minority) of the HPSCI; (5) The Leader of the Senate; (6) The Minority Leader of the Senate; (7) The Chair of the Senate Select Committee on Intelligence, SSCI; and finally (8) the Vice-Chair of the SSCI.
Example: When the Chief Executive (the President) initiates an intelligence operation on behalf of the United States, the President triggers a “finding memo.” In essence, the instruction to the intel agency or agencies to authorize a covert operation. When that process takes place, the Go8 are the first people notified. Depending on the sensitivity of the operation, sometimes the G08 are notified immediately after the operation is conducted. The notification can be a phone call or an in-person briefing.
Because of the sensitivity of their intelligence information, the Gang of Eight hold security clearances that permit them to receive and review all intelligence operations. The intelligence community are also responsible for briefing the Go8 with the same information they use to brief the President.

~ 2021 Gang of Eight ~
The Go8 design is intended to put intelligence oversight upon both political parties in Congress; it is designed that way by informing the minority leaders of both the House and Senate as well as the ranking minority members of the SSCI and HPSCI. Under the concept, the President cannot conduct an intelligence operation; and the intelligence community cannot carry out intelligence gathering operations without the majority and minority parties knowing about it.
The modern design of this oversight system was done to keep rogue and/or corrupt intelligence operations from happening. However, as we shared in the preview to this entire discussion, the process was usurped during the Obama era. {GO DEEP}
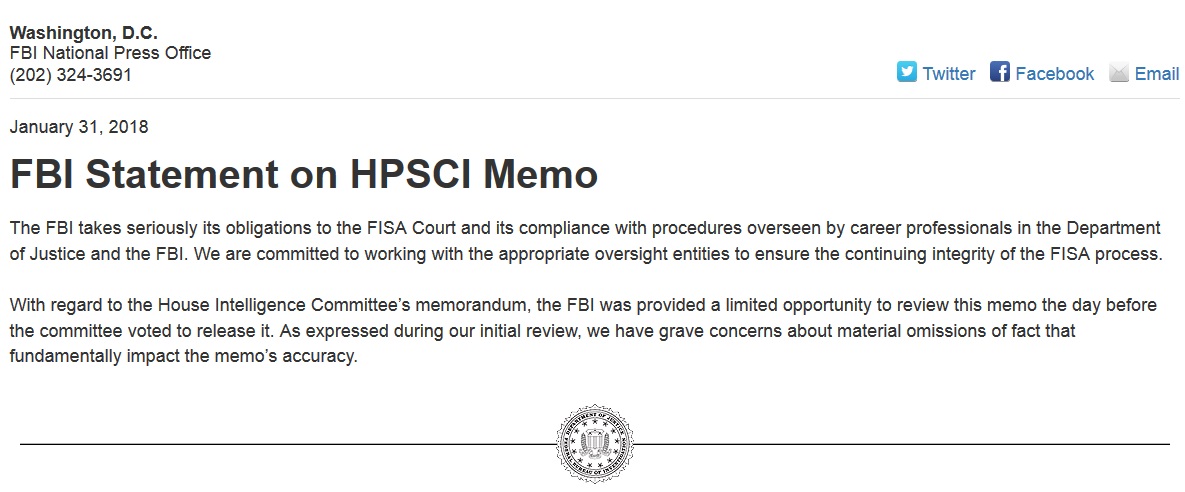
Former FBI Director James Comey openly admitted to Congress on March 20, 2017, that the FBI, FBI Counterintelligence Division, DOJ and DOJ-National Security Division, together with the Office of the Director of National Intelligence (ODNI) and the CIA, had been conducting independent investigations of Donald Trump for over a year without informing the Go8. Comey justified the lack of informing Go8 oversight by saying, “because of the sensitivity of the matter.”
Stupidly, Congress never pressed James Comey on that issue. The arrogance was astounding, and the acceptance by Congress was infuriating. However, that specific example highlighted just how politically corrupt the system had become. In essence, Team Obama usurped the entire design of congressional oversight…. and Congress just brushed it off.
Keep in mind, Comey did not say the White House was unaware; in fact he said exactly the opposite, he said, “The White House was informed through the National Security Council,” (the NSC). The unavoidable implication and James Comey admission that everyone just brushed aside, was that President Obama’s National Security Advisor, Susan Rice, was informed of the intelligence operation(s) against Donald Trump. After all, the NSC reports to the National Security Advisor.
Does the January 20, 2017, Susan Rice memo look different now?
Again, no one saw the immediate issue. What Comey just described on that March Day in 2017 was the usurpation of the entire reason the Gang of Eight exists; to eliminate the potential for political weaponization of the Intelligence Community by the executive branch. The G08 notifications to the majority and minority are specifically designed to make sure what James Comey admitted to doing was never supposed to happen.
Team Obama carried out a political operation using the intelligence community and the checks-and-balances in the system were intentionally usurped. This is an indisputable fact.
Worse still, the entire legislative branch of Congress, which then specifically included the Republicans that now controlled the House and Senate, did nothing. They just ignored what was admitted. The usurpation was willfully ignored.
The mechanism of the G08 was bypassed without a twitch of condemnation or investigation…. because the common enemy was Donald Trump.
This example highlights the collapse of the system. Obama, the Executive Branch, collapsed the system by usurping the process; in essence the process became the bigger issue, and the lack of immediate Legislative Branch reaction became evidence of open acceptance. The outcomes of the usurpation played out over the next four years, Donald J. Trump was kneecapped and lost his presidency because of it. However, the bigger issue of the collapse still exists.
The downstream consequence of the Legislative Branch accepting the Executive Branch usurpation meant both intelligence committees were compromised. Additionally, the leadership of both the House and Senate were complicit. Think about this carefully. The Legislative Branch allowance of the intelligence usurpation meant the Legislative Branch was now subservient to the Intelligence Branch.
That’s where we are.
Right now.
That’s where we are.
Term-3 Obama is now back in the White House with Joe Biden.
NOTE: Former Obama National Security aide and counsel to the President, Lisa Monaco, is in her current position as Deputy Attorney General, specifically to make sure all of these revelations do not become a legal risk to Barack Obama and the people who created them. The SSCI confirmed Monaco for this purpose because the Senate is just as much at risk.
Term-1 and Term-2 Obama usurped the ‘check and balance‘ within the system and weaponized the intelligence apparatus. During Trump’s term that weaponization was covered up by a compliant congress, complicit senate intelligence committee, and not a single member of the oversight called it out. Now, Term-3 Obama steps back in to continue the cover up and continue the weaponization.
Hopefully, you can now see the scale of the problem that surrounds us with specific citation for what has taken place. What I just explained to you above is not conspiracy theory, it is admitted fact that anyone can look upon. Yet….
Have you seen this mentioned anywhere? Have you seen this called out by anyone in Congress? Have you seen anyone in media (ally or adversary) call this out? Have you seen any member of the Judicial Branch stand up and say wait, what is taking place is not okay? Have you seen a single candidate for elected office point this out? Have you seen anyone advising a candidate to point this out?
This is our current status. It is not deniable. The truth exists regardless of our comfort.
Not a single person in power will say openly what has taken place. They are scared of the Fourth Branch. The evidence of what has taken place is right there in front of our face. The words, actions and activities of those who participated in this process are not deniable, in fact most of it is on record.
There are only two members of the Gang of Eight who have existed in place from January 2007 (the real beginning of Obama’s term, two years before he took office when the Congress flipped). Only two members of the G08 have been consistently in place from January of 2007 to right now, today. All the others came and went, but two members of the Gang of Eight have been part of that failed and collapsed oversight throughout the past 15 years, Nancy Pelosi and Mitch McConnell.
 ♦ TECHNOLOGY – On a global scale – the modern intelligence gathering networks are now dependent on data collection to execute their intelligence missions. In the digital age nations have been executing various methods to gather that data. Digital surveillance has replaced other methods of interception. Those surveillance efforts have resulted in a coalescing of regional data networks based on historic multi-national relationships.
♦ TECHNOLOGY – On a global scale – the modern intelligence gathering networks are now dependent on data collection to execute their intelligence missions. In the digital age nations have been executing various methods to gather that data. Digital surveillance has replaced other methods of interception. Those surveillance efforts have resulted in a coalescing of regional data networks based on historic multi-national relationships.
We have a recent frame of reference for the “U.S. data collection network” within the NSA. Through the allied process the Five Eyes nations all rely on the NSA surveillance database (U.K, Australia, Canada, New Zealand and U.S.) The NSA database provides the digital baseline for intelligence operations in defense of our allies. The portals into the NSA database are essentially an assembly of allies in like-minded ideological connection to the United States.
Unfortunately, there have been some revelations about the NSA database being used to monitor our allies, like in the example of Germany and surveillance on Angela Merkel’s phone. As long as “the good guys” are operating honorably, allies of the United States can feel confident about having protection from the NSA surveillance of global digital data. We warn our friends if we detect something dangerous etc.
The U.S. has nodes on communication pipelines to intercept and extract data. We have also launched hundreds, perhaps thousands, of satellites to conduct surveillance and gather up data. All of this data is fed into the NSA database where it is monitored (presumably) as a national security mechanism, and in defense of our allies.
However, what about data collection or data networks that are outside the NSA database? What do our enemies do? The NSA database is just one intelligence operation of digital surveillance amid the entire world, and we do not allow access by adversaries we are monitoring. So what do they do? What do our allies do who might not trust the United States due to past inconsistencies, ie. the Middle East?
The answers to those questions highlight other data collection networks. So, a brief review of the major players is needed.
♦ CHINA – China operates their own database. They, like the NSA, scoop up data for their system. Like us, China launches satellites and deploys other electronic data collection methods to download into their database. This is why the issues of electronic devices manufactured in China becomes problematic. Part of the Chinese data collection system involves the use of spyware, hacking and extraction.
Issues with Chinese communication company Huawei take on an added dimension when you consider the goal of the Chinese government to conduct surveillance and assemble a network of data to compete with the United States via the NSA. Other Chinese methods of surveillance and data-collection are less subversive, as in the examples of TicTok and WeChat. These are Chinese social media companies that are scraping data just like the NSA scrapes data from Facebook, Twitter and other Silicon Valley tech companies. [ Remember, the Intelligence Branch is a public-private partnership. ]
♦ RUSSIA – It is very likely that Russia operates their own database. We know Russia launches satellites, just like China and the USA, for the same purposes. Russia is also very proficient at hacking into other databases and extracting information to store and utilize in their own network. The difference between the U.S., China and Russia is likely that Russia spends more time on the hacking aspect because they do not generate actual technology systems as rapidly as the U.S. and China.
The most recent database creation is an outcome of an ally having to take action because they cannot rely on the ideology of the United States remaining consistent, as the administrations ping-pong based on ideology.
♦ SAUDI ARABIA – Yes, in 2016 we discovered that Saudi Arabia was now operating their own intelligence data-gathering operation. It would make sense, given the nature of the Middle East and the constant fluctuations in political support from the United States. It is a lesson the allied Arab community and Gulf Cooperation Council learned quickly when President Obama went to Cairo in 2009 and launched the Islamist Spring (Arab Spring) upon them.


I have no doubt the creation of the Saudi intelligence network was specifically because the Obama administration started supporting radical Islamists within the Muslim Brotherhood and threw fuel on the fires of extremism all over the Arab world.
Think about it., What would you do if you were Saudi Arabia, Egypt, Bahrain, Kuwait, the UAE, Jordan, Oman or Yemen and you knew the United States could just trigger an internal uprising of al-Qaeda, ISIS and the political arm of the Muslim Brotherhood to seek your destruction?
Without a doubt, those urgent lessons from 2009, 2010, 2011 triggered the formation of the Arab Intelligence Network as a network to defend itself with consistency. They assembled the network and activated it in 2017 as pictured above.
♦ Israel – Along a similar outlook to the Arab network, no doubt Israel operates an independent data collection system as a method of protecting itself from ever-changing U.S. politics amid a region that is extremely hostile to its very existence. Like the others, Israel launches proprietary satellites, and we can be sure they use covert methods to gather electronic data just like the U.S. and China.
As we have recently seen in the Pegasus story, Israel creates spyware programs that are able to track and monitor cell phone communications of targets. The spyware would not work unless Israel had access to some network where the phone meta-data was actually stored. So yeah, it makes sense for Israel to operate an independent intelligence database.
♦ Summary: As we understand the United States Intelligence Branch of government as the superseding entity that controls the internal politics of our nation, we also must consider that multiple nations have the same issue. There are major intelligence networks around the world beside the NSA “Five-Eyes” database. China, Russia, Saudi Arabia and Israel all operate proprietary databases deploying the same tools and techniques for assembly.
The geopolitical conflict that has always existed has now shifted into a digital battle-space. The Intelligence Agencies from these regions are now operating as the backbone of the government that uses them, and has become dependent on them. [<- Reread that].
Once you accept the digital-era intelligence apparatus of China, Russia, Saudi-Arabia, The United States and Israel, are now the primary national security mechanisms for stabilization of government; then you accept the importance of those intelligence operations.
Once you understand how foundational those modern intelligence operations have become for the stability and continuity of those governments…… then you begin to understand just how the United States intelligence community became more important than the government that created it.
From that point it is then critical to understand that domestic intelligence operations are underway to monitor the electronic communication of American citizens inside our own country. YOU are under surveillance. The parents who confront school boards are under surveillance. The political operatives inside the FBI are monitoring everyone who comes onto the radar, that is why the National School Boards Association asked the White House, then the DOJ, to have the FBI start targeting parents. Are things making sense now?
♦ Public Private Partnership – The modern Fourth Branch of Government is only possible because of a Public-Private partnership with the intelligence apparatus. You do not have to take my word for it, the partnership is so brazened they have made public admissions.
 The biggest names in Big Tech announced in June their partnership with the Five Eyes intelligence network, ultimately controlled by the NSA, to: (1) monitor all activity in their platforms; (2) identify extremist content; (3) look for expressions of Domestic Violent Extremism (DVE); and then, (4) put the content details into a database where the Five Eyes intelligence agencies (U.K., U.S., Australia, Canada, New Zealand) can access it.
The biggest names in Big Tech announced in June their partnership with the Five Eyes intelligence network, ultimately controlled by the NSA, to: (1) monitor all activity in their platforms; (2) identify extremist content; (3) look for expressions of Domestic Violent Extremism (DVE); and then, (4) put the content details into a database where the Five Eyes intelligence agencies (U.K., U.S., Australia, Canada, New Zealand) can access it.
Facebook, Twitter, Google and Microsoft are all partnering with the intelligence apparatus. It might be difficult to fathom how openly they admit this, but they do. Look at this sentence in the press release (emphasis mine):
[…] “The Group will use lists from intelligence-sharing group Five Eyes adding URLs and PDFs from more groups, including the Proud Boys, the Three Percenters and neo-Nazis.”
Think about that sentence structure very carefully. They are “adding to” the preexisting list…. admitting the group (aka Big Tech) already have access to the the intelligence-sharing database… and also admitting there is a preexisting list created by the Five Eyes consortium.
Obviously, who and what is defined as “extremist content” will be determined by the Big Tech insiders themselves. This provides a gateway, another plausible deniability aspect, to cover the Intelligence Branch from any oversight.
When the Intelligence Branch within government wants to conduct surveillance and monitor American citizens, they run up against problems due to the Constitution of the United States. They get around those legal limitations by sub-contracting the intelligence gathering, the actual data mining, and allowing outside parties (contractors) to have access to the central database.
The government cannot conduct electronic searches (4th amendment issue) without a warrant; however, private individuals can search and report back as long as they have access. What is being admitted is exactly that preexisting partnership. The difference is that Big Tech will flag the content from within their platforms, and now a secondary database filled with the extracted information will be provided openly for the Intelligence Branch to exploit.
 The volume of metadata captured by the NSA has always been a problem because of the filters needed to make the targeting useful. There is a lot of noise in collecting all data that makes the parts you really want to identify more difficult to capture. This new admission puts a new massive filtration system in the metadata that circumvents any privacy protections for individuals.
The volume of metadata captured by the NSA has always been a problem because of the filters needed to make the targeting useful. There is a lot of noise in collecting all data that makes the parts you really want to identify more difficult to capture. This new admission puts a new massive filtration system in the metadata that circumvents any privacy protections for individuals.
Previously, the Intelligence Branch worked around the constitutional and unlawful search issue by using resources that were not in the United States. A domestic U.S. agency, working on behalf of the U.S. government, cannot listen on your calls without a warrant. However, if the U.S. agency sub-contracts to say a Canadian group, or foreign ally, the privacy invasion is no longer legally restricted by U.S. law.
What was announced in June 2021 is an alarming admission of a prior relationship along with open intent to define their domestic political opposition as extremists.
July 26 (Reuters) – A counterterrorism organization formed by some of the biggest U.S. tech companies including Facebook (FB.O) and Microsoft (MSFT.O) is significantly expanding the types of extremist content shared between firms in a key database, aiming to crack down on material from white supremacists and far-right militias, the group told Reuters.
Until now, the Global Internet Forum to Counter Terrorism’s (GIFCT) database has focused on videos and images from terrorist groups on a United Nations list and so has largely consisted of content from Islamist extremist organizations such as Islamic State, al Qaeda and the Taliban.
Over the next few months, the group will add attacker manifestos – often shared by sympathizers after white supremacist violence – and other publications and links flagged by U.N. initiative Tech Against Terrorism. It will use lists from intelligence-sharing group Five Eyes, adding URLs and PDFs from more groups, including the Proud Boys, the Three Percenters and neo-Nazis.
The firms, which include Twitter (TWTR.N) and Alphabet Inc’s (GOOGL.O) YouTube, share “hashes,” unique numerical representations of original pieces of content that have been removed from their services. Other platforms use these to identify the same content on their own sites in order to review or remove it. (read more)
The influence of the Intelligence Branch now reaches into our lives, our personal lives.
In the decades before 9/11/01 the intelligence apparatus intersected with government, influenced government, and undoubtedly controlled many institutions with it. The legislative oversight function was weak and growing weaker, but it still existed and could have been used to keep the IC in check. However, after the events of 9/11/01, the short-sighted legislative reactions opened the door to allow the surveillance state to weaponize against domestic enemies.
After the Patriot Act was triggered, not coincidentally only six weeks after 9/11, a slow and dangerous fuse was lit that ends with the intelligence apparatus being granted a massive amount of power. Simultaneously the mission of the intelligence community now encompassed monitoring domestic threats as defined by the people who operate the surveillance system.
The problem with assembled power is always what happens when a Machiavellian network takes control over that power and begins the process to weaponize the tools for their own malicious benefit. That is exactly what the network of President Barack Obama did.
The Obama network took pre-assembled intelligence weapons (we should never have allowed to be created) and turned those weapons into political tools for his radical and fundamental change. The target was the essential fabric of our nation.
Ultimately, this corrupt political process gave power to create the Fourth Branch of Government, the Intelligence Branch. From that perspective the fundamental change was successful.
This is the scale of corrupt political compromise on both sides of the DC dynamic that we are up against. Preserving this system is also what removing Donald Trump is all about…. The targeting of President Trump in order to preserve the system, the system that was weaponized during the Obama administration, is what the actions of the DOJ and FBI were all about.
What would powerful people in DC do to stop the American people from finding this out?
…. Including a raid on Mar-a-Lago.
If only people understood how accurate this really is.
(1) The Patriot Act turned the intel surveillance radar from foreign searches for terrorists to domestic searches for terrorists.
(2) Obama/Biden then redefined what is a "terrorist" to include their political opposition. https://t.co/EW43WmpeaT
— TheLastRefuge (@TheLastRefuge2) October 14, 2022
Support Ongoing CTH Research HERE

Arab Spring
Iran Syria Policy and Operations Group
https://www.liquisearch.com/iran_syria_policy_and_operations_group
Didn’t work out. Taliban has a saying… “Americans have the watches, but we have the time.”
What Wesley forgets is your enemy gets a vote. Also when your spending 200k to blow up a mud hut, your in the wrong war.
Minerals, its all minerals. That is what those countries have. They are currently starving Africa. Did you know Ukraine has $9 trillion in minerals? They were signing the mining rights just before Russia invaded.
Exactly. Where are a large percentage of rare earth minerals used for much of the schlock “Green” energy come from?
Africa. Who controls much of Africa now? China.
Now you know why the Christian/western/good governments of Central & South Africa were overthrown.
No better fighters in their time than the brave & innovative Rhodesian military.
Still at it
Obama did *not* revise his position on Iran. He doubled down on #JCPOAppeasement.
If you thought Obama was expressing regret about his Iran policy when you saw the clip yesterday…you got played. Watch the rest of the clip:
It wasn’t just a beta test for American Tyranny, though.
Barry of Arabia was also trying to rebuild the Caliphate for his Ayatollah.
“Papa’s Got a Brand New Bagram!”
I have a feeling his newly installed heating oil tank will spring a leak
“Barry of Arabia was also trying to rebuild the Caliphate for his Ayatollah.”
And the details of this plan was brilliantly described and expertly detailed in Dinesh D’Souza’s movie “2016: Obama’s America”
Yep. Informative movie.
I ask only that you kneel
Looks like a serious case of lack of cultural marxist “Diversity” lies. The Cabal never practices what they preach though they do in this instance have their clown golem
Unlike the cruel Trump, who demanded that you stand, I require only that you kneel
Bizarre would be an understatement. Who is he bending his knee too?
St George Floyd of Fentanyl-Crack?
Mass Psychosis, Need to give obama longer fingernails to properly portray the devil. I always knew who he was.
We can’t live long enough to see this jumbled up mess resolved.
Kudos Sundance. I see a book in that screed and that picture posted by Mass Psychosis would make a great cover.
I really do hope you have security.
Satan
“The Patriot Act turned the intel surveillance radar from foreign searches for terrorists to domestic searches for terrorists.”
Bongino interviewed an FBI whistleblower tonight who explained how the FBI was using the J6 investigation as a vehicle to inflate domestic terrorist numbers around the country.
Essential starts at about 8:00
On March 2, 2021, FBI director Wray testified to Congress about J6 and said unequivocally that white supremacists are the most lethal domestic terrorist in our country. Sounds like Wray may have been trying to pad numbers to justify his testimony.
What event lead to the patriot act? Guess who performed the act? Same people that took out JFK and all others who don’t play by the rules.
Should be “led” not lead.You make a fair amount of verb tense mistakes—foreign born?
Shhhh, don’t tell the FBI!
One Negro and the rest white folk.
The political class hitches their wagon to anyone willing to pull them along.
It’s to bad Jim Jones wasn’t in charge of the drink at that table.
Should be “too” not to.
This is not a spelling test. We all make mistakes.
It’s not grammar class here. Please give it a break.
Yes, and the fraudulent vote count itself is another of the weapons used against us, as well as the complete corruption of the political dialog. The whole sorry pattern is the same as the “color revolutions” in other nations, as you’ve noted. It is, in fact, a worldwide movement against humanity. And guess who’s behind it?
Many people HAVE recognized what has been happening. They’ve often been derided by folks who prefer the fantasy of FOXCNNNBCBS when they’ve even been acknowledged at all. Things are dire.
They are voting for people who refuse to address these issues. My Republican rep isn’t and I am sure yours isn’t either. When you give these guys power you provide the power structure with legitimacy. This is why UofF is hiring Sasse. Don’t give them legitimacy. Don’t vote for them. Legitimizing these issues does more damage than a Democrat.
Well, I do what I can when voting. Although I don’t feel like getting into another argument with anyone, I agree that voting for confirmed leftists such as Romney, Collins or McConnell just because they have an R after their name is only assisting the Enemy in his awful scheme. I still vote for candidates who make a difference, but otherwise one’s time, energy and money needs to be concentrated elsewhere including doing what one can to restore legitimate vote counting, and opening the eyes of the blind.
There is only one conclusion:
President Trump is in the gravest danger from his own government.
And if the danger blossoms into a successfully lethal action, a question fraught with the greatest weight of Destiny will gaze at us and ask:
“What will you do?”
Well, that’s the real question isn’t it? So far, I don’t see the will to do anything of genuine substance by very many. — Pray, and do what you can.
Funny, I see ALL SORTS of “WILL”, and a LOT of action.
Guess all you woebegones and eeyores are frickin blind, huh?
Ain’t even gonna waste my time, recounting all the ways you are wrong, or the things happening that you pretend not to see; your hopeless!
I’ll take the expected criticism for challenging the concept that prayer is not an effort of “genuine substance”. Having recommended prayer as the first course of action, I trust that you also agree.
They keep saying Ukraine is winning, or banning you if you say otherwise. How is your supermarket compared to a Russia supermarket
The most sanctioned country on earth.
They have more food than my Aldi, prices are cheaper than Aldi, and it was nice to see Barilla pasta and Heinz on the shelves lol
I still will not eat Zee Bugzs.
Thanks, now I’m hungry.
that makes america’s shopping centers look like a ragtag bunch of discount stores IF great shopping centers even exist now. However, it is what america’s shopping centers USE to look like. I still remember.
Yep we have been assimilated..
With massive fraud on open global display in the 2020 elections, the Republican Party sat quiet as the worst administration in U.S. history stole the White House and numerous Congressional seats in broad daylight, or the dark of night when it came to after-hours DNC ballot drops at key swing state distracts, captured on film.
“But we are talking about a nation of fools, now. Millions of healthy Americans are standing in line to be tested for an illness for which they have no symptoms, using a test already proven to be more than 80% false, for an illness that had a 99.5% survival rate without any “vaccines.” Clearly, we are not dealing with the sharpest knives in the drawer here! In fact, the average American isn’t sharp enough to cut melted butter now.
Nope, so long as the American people remain ignorant of so many facts and unwilling to confront the evil we have witnessed in the past two years, we can forget about solving anything with elections. We don’t have legitimate elections anymore, and until we confront the fraud and corruption in 2020, we will never have legitimate elections ever again.”
Lex Greene
We are NOT voting our way out of this slow burn to tyranny.
my gut says the same thing
elections are a mirage
my gut also says when they do come around
behind every blade of grass
Keyboard warriors,…just exactly HOW is EXCERCISING the 2A option going to accomplish our goals of restoring a Constitutional Republic?
How are WE going to “Make America Great Again” by resorting to the ammo box, when we haven’t even fully explored the ballot box?
Vote on Nov 8th, “what have you got to LOSE?”
Other than rediculous “you can’t vote your way out of tyranny” statements, y’all don’t actually suggest ANY plan.
All you are really doing, is “sewing despondency” and suppressing MAGA votes, which sure sounds like “aid and comfort” to me.
Bullshirt we aren’t.
Just WATCH us, lol!
Ain’t sayin its EASY, war ISN’T easy, and we ARE in a Global war for humanity, and ONE part of the battle is fighting with BALLOTS, not bullets.
Agreed. If people don’t vote because what they know about the machines then they just fell victim to part two of the cheat tactic. Demoralization. They beat a weak mind into submitting one of his arrows from the quiver just because he believed it wasn’t sharp enough.
If you’re fighting for your life and life of everyone on earth, you use that arrow whether it’s dull, broken, featherless, whatever…. You don’t just cast it aside. It’s sharp enough. Take a shot and hope it lands.
True Bshaw.
I know many who have not been “assimilated”.
Many who have hope for the future of our country for themselves and their families.
This is real life, not a “Star Trek” episode, not fantasy or fiction.
Like you say, I will take that “last shot” with my last breath for my children and grandchildren.
And I will dam sure make it lands.
I agree voting is still a part of what we do. But the reality is the Democrats and the Republicans are protecting their millions not our interests. . Not to mention voting has been rigged…..we no longer gave elections but “selections”.
We can not be dismissive of our Founding Documents and the wisdom that lies therein.
“When a long train of abuses and usurpations, pursuing invariably the same object, evinces a Design to reduce them under absolute Depotism, it is the Right, it is their Duty, to throw off such Government, and to provide new guards for their future security.”
Declaration of Independence
You CANNOT comply your way out of tyranny.
Especially since the major portion of the fraud occurred in a “relatively” small number of places. If we win a lot of small battles we can regain some state legislators. I’m not going to just hand them this country on a silver platter. Make them cheat their balls off even worse than last time. More than half the country already believes the election was stolen. Make them even more illegitimate. It makes it harder for them to wield power. Fraud at this level costs them massive resources, coordination, and exposes them.
Fight them on EVERY front we can. We concede nothing. Not an inch to these punks.
For what it’s worth… TPTB seem to be concerned about the election. I think that is why you’re seeing such reckless spending. Sure, the “Great Reset” is part of it but they’re also trying trying to feed at the trough one last time in case they do lose their power.
Another thing I want to point about the fraud is that I believe a large part of the Dems also know that there was massive fraud but wouldn’t admit it because they believe it was justified to get rid of Trump. Now they’ll have to come to grips with the fact that all of our elections are rigged. I expect a MAGA turnout like 2020 because so many people are furious. The fraud will have to surpass that. For a midterm? It will be even more blatant and so much harder to defend.
The upcoming midterms will be the test of your theory that this battle against the swamp can be won at the ballot box. The amount of cheating will be the deciding factor, as the Democrats will not give up the election without using every weapon in their arsenal.
“Educate and inform the whole mass of people. They are the only sure reliance for the preservation of our liberty.”
— Thomas Jefferson
As Sundance pointed out on Twiter: Look at what Pelosi and Sxhumer were able to accomplish with tiny majorities versus Ryan and McConnell with large majorities.
Woke up yesterday with a stuffy nose and sneezing – Guess What? I have the *common* cold!! Yes! the old fashion cold is back and this 80 yo is treating it accordingly just like in all the past years of my life!!!
Absolutely true. I have no doubt you will find many Republicans on the Hill willingly complicit in the Democrat Party corruption. Many of these politicians bend over to corporate America and especially Big Pharma. They will do as their lobbyists tell them to. Would be interesting to see how many of the politicians get huge donations from Pfizer and Moderna.
For example, I have listened to Rand Paul rage at Fauci, but never once go after Pfizer or any other drug company for producing the disastrous Covid vaccines.
Well, it worked. Here’s another one. An indirect marketing play for Big Pharma. Read both links.
https://t.me/DonbassDevushka/29883
Now from the NY Post:
https://t.me/DonbassDevushka/29882
Obama Doctrine: Reward Friends, Punish Enemies
The master beta for the US Intelligence cabal..
On a related note, the Pentagon is now going to pay Ukraine’s Starlink bills shortly after Elon Musk agrees to purchase Jack’s Magic Coffee Shop at the original share price, shortly after “disruptions” to Starlink’s services in Ukraine, shortly after Musk calls for peace talks, and shortly after Musk talks about an “App for Everything.”
Anyone else see a quid, a pro, and a quo somewhere in there?
“History provided enough warnings from Dwight D. Eisenhower (military) to John F. Kennedy (CIA), to Richard Nixon (FBI), to all the modern versions of warnings and frustrations from HPSCI Devin Nunes and ODNI Ric Grenell.”
And by Harry Truman on the CIA even though he had signed the authorization for it.
President Truman created the CIA. But in the 1970s, he told his biographer, Merle Miller:
I think [creation of the CIA] was a mistake. And if I’d known what was going to happen, I never would have done it.
Why, they’ve got an organization over there in Virginia now that is practically the equal of the Pentagon in many ways. And I think I’ve told you, one Pentagon is one too many.
Now, as nearly as I can make out, those fellows in the CIA don’t just report on wars and the like, they go out and make their own, and there’s nobody to keep track of what they’re up to. They spend billions of dollars on stirring up trouble so they’ll have something to report on. They’ve become … it’s become a government all of its own and all secret. They don’t have to account to anybody.
That’s a very dangerous thing in a democratic society, and it’s got to be put a stop to. The people have got a right to know what those birds are up to. And if I was back in the White House, people would know.
This is how some Republican Senators voted with Joe Biden’s destructive agenda.
– Susan Collins (ME): 69.10%
– Lisa Murkowski (AK): 66.70%
– Rob Portman (OH): 61.80%
– Lindsey Graham (SC): 58.20%
– Mitt Romney (UT): 56.40%
– Mitch McConnell (KY): 54.50%
Why the alphabet agencies are running rampant with no oversight.
________________________
EDITED TO ADD: The non-RINOs’ record
– Rand Paul (R-KY)= 17.60%
– Tom Cotton (R-AR)= 17.00%
– Marsha Blackburn (R-TN)= 16.70%
– Ted Cruz (R-TX)= 14.80%
– Rick Scott (R-FL)= 14.50%
– Josh Hawley (R-MO)= 12.70%
The UNEDITED Version of the Washington Post LETTER by POTUS TRUMAN
https://archive.org/details/LimitCIARoleToIntelligenceByHarrySTruman/mode/2up
I’m suspicious cat when liberals need to “name” an event. As SOON as I heard Arab Spring I was sure it was bogus.
Neither Arab nor Spring. Discuss.
“The problem with assembled power is always what happens when a Machiavellian network takes control over that power and begins the process to weaponize the tools for their own malicious benefit. That is exactly what the network of President Barack Obama did.”
This is not Machiavellian.
Machiavellian is amoral (practical). These people are immoral (corrupt / evil). The two are not the same.
The above (Obama and his spawn) is more like what was described by Lord Action.
(Power corrupts and absolute power corrupts absolutely)
The only power we have is within the Republican Party. Make Rubio address this or get him out of office. He is up for re-election. Target him for removal.
It’s review day, must be a test on Monday.
Eight Full Years
Sundance: “The second larger Obama/Holder objective was control over the FBI. Why was that important? Because the FBI does the domestic investigative work on anyone who needs or holds a security clearance. The removal of security clearances could be used as a filter to further build the internal ideological army they were assembling. Additionally, with new power in the ODNI created as a downstream consequence of the Patriot Act, new protocols for U.S. security clearances were easy to justify.”
The FBI’s vetting program, however, generates a separate worry: that political authorities will make ideology a component of political promotion, fraying the military’s loyalty to the U.S. Constitution and introducing a specific partisan perspective. If political violence continues, the military will be called upon to preserve order. And with the precedent of ideological examination, it is possible that the Senate, exercising its power to confirm or deny senior-level military promotions, may conduct ideological tests during promotion hearings.
https://thehill.com/opinion/national-security/535823-we-must-resist-ideological-tests-for-the-us-military/
Amazon to link Kuiper satellites to DoD’s mesh network in space
by Sandra Erwin — October 14, 2022
Some Kuiper satellites will serve as “translators” between commercial imagery providers and DoD’s Transport Layer
WASHINGTON — Amazon’s Project Kuiper will install DoD-compliant laser communications terminals on its internet satellites so they can transfer data from remote-sensing satellites directly into the military’s mesh network in low Earth orbit.
Derek Tournear, director of the U.S. Space Force’s Space Development Agency, said the plan is for some Kuiper satellites to serve as “translators” so they can support high-speed data transfer, for example, from commercial imaging satellites to military users on the ground.
Speaking Oct. 13 at the MilSat Symposium in Mountain View, California, Tournear said the agreement with Amazon is significant because it will help move data more quickly and securely.
The Space Development Agency (SDA) is building a mesh network — called Transport Layer — of hundreds of satellites in low Earth orbit to relay time-sensitive data to military forces around the world. To make its satellites interoperable, the agency requires vendors to use optical terminals that comply with SDA’s specifications.
SDA also plans to establish agreements with commercial remote-sensing companies so they can send imagery from their satellites directly to the Transport Layer. But not every imagery provider will have compatible optical links, Tournear noted, so having a commercial data-relay partner like Amazon to serve as a translator will be important.
“Amazon Kuiper will have their own optical terminals that they’re planning on using for their mesh network,” Tournear said. “But they’re going to put some SDA-compatible optical terminals on some of their satellites so that those satellites act as translators. That way we can move data on and off the Kuiper network onto the Transport Layer.”
Project Kuiper is planning a network of 3,236 satellites in low Earth orbit to provide high-speed internet globally. The Federal Communications Commission authorized the system in 2020. The first two prototype satellites are projected to launch in 2023.
____________________________________________________
You can Read The Whole Thing Here but the rest of the story not really relevant to this point.
Since 2009, the US Government (i.e. DoD, DHS, et al) have had under contract a consortium composed of a Who is Who of the NASDAQ defined BIG TECH firms (Amazon, Google, HP, Microsoft, INTEL, et al). The stated purpose of the CONTRACT was “INTEGRATED Data Management Services”.
Amazon is defined as more than a “Digital Department Store” on NASDAQ and by the US Government.
Also, add to the US Big Tech companies their legally formed and linked foreign partners.
Google and Microsoft were Beta testing the Social Report Card APPS developed for China Inc. long before 2016.
“However, a generational review is not useful, as the reference impacting us ‘right now‘ gets lost.” You make a very important point. I cannot describe my impatience with anyone who wants to reach back to a historical reference to describe our current situation. I feel it dilutes the intensity of focusing on what needs to be done right now. I feel it draws light away from laser focus on the individuals causing the problems right now.
On the one hand, those who don’t learn from history,…on the other hand we have NEVER seen anything in History exactly like what we are seeing now.
I seem to remember Gen. Stanley McChrystal was involved in working for the DNC in 2020:
https://www.washingtonpost.com/politics/technology-once-used-to-combat-
isis-propaganda-is-enlisted-by-democratic-group-to-counter-trumps-coronavirus-messaging/2020/05/01/6bed5f70-8a5b-11ea-ac8a-fe9b8088e101_story.html
I’ve been wondering if they’ve taken the Twitter Psy-op about as far as it can go – because it really doesn’t look like their attempt to fight Russia via Twitter and Tech is going so well. And their recent move the censor anything that even slightly conflicts with their propaganda – kind of smacks of desperation.
Personally I think they blew it on Ukraine because they forgot that a significant portion of the country was primed to be suspicious of anything related to Ukraine-Russia based on 1) the failed Russia Witch Hunt, 2) the perfect phone call to Ukraine impeachment, and 3) the Hunter Biden laptop conflicts in Ukraine.
They’ve co-opted the brains of at least half of conservatives with it (“it” being the Current-Thing mob, which has now been sicced on Russia). Sure, a bunch of people like you and me are still standing. But once they’ve got 3/4 of Americans wrapped around their finger, the next 1/8 will be reached in their next venture.
Living as I do in a federal census-defined area of “frontier” status(<2 people/ sq mile), I find it hard to accept why so many people feel the need for connectivity with others via strangers on the interwebs. Here, I’m talking about the need of people for Facebook, Twitter, and other similar sites.
From my perspective, social media sites are not necessary for good A’s of a healthy DL. (The common ADL thing.) People who need social media sites I think may have a problem tending towards narcissistic personality disorder, but that’s just me.
In the August primary election here, 43 people cast votes in my voting precinct for US Congressional Rep. Liz Cheney got six of those votes. Not a bad neighborhood to live in, here.
I would demand the six move out.
Well, 3 were octeganarians, with eyesite that makes Mr. McGoo seem 20/20 by comparison, and didn’t realise they were voting for Liz,..
HA!!!! Then they will not know they are being moved! Unless their nurses can be cuffed!
“Writing in his Substack [SEE HERE], Dr Robert Malone draws attention to the EDIFY research.”
Can anyone tell me just who Dr. Robert Malone is?
For months I have been asking this question. It seems as thought he is hiding in plain sight.
I do not care that his original intent was for mRNA-producing spike proteins to be used as a delivery system for other reasons…his own technology seems to be killing people.
And what does he have to do with EDIFY research?
One place to start would be what Dr. Malone himself says about his background, the info can be checked:
https://rwmalonemd.substack.com/p/robert-malone-responds-to-trolls?utm_source=post-email-title&publication_id=583200&post_id=75427972&isFreemail=true&token=eyJ1c2VyX2lkIjo5Mzc0NjQwNCwicG9zdF9pZCI6NzU0Mjc5NzIsImlhdCI6MTY2NDM4OTkyOSwiZXhwIjoxNjY2OTgxOTI5LCJpc3MiOiJwdWItNTgzMjAwIiwic3ViIjoicG9zdC1yZWFjdGlvbiJ9.snBrVdc-BHqKX8NHrGayAgN44Nj193uAjmhnNoLN8RA&utm_medium=email
In these times, it is impossible to know for sure the truth about any figure or source. (This also applies to reader comments appended to articles like this one.)
The facts of the issues are the important focus, the nature of the messenger is not unimportant but should not be a primary focus. Ad hominem attacking the messenger is a common ploy of Machiavellians attempting to divert attention.
Thank you for the article. Dr. Malone’s own words prove my point.
First, Malone is not a messenger but the active scientist who invented mRNA, with with synthetic spike proteins. He himself called the technology failed and toxic.
Second, if we take Malone at his word, why did he apply for nine patents, why did the patent office award them and why did Merck -a failed company – purchase said patents?
I have friends who are virologists who know of Dr. Malone and have always advised that penetrating a cell’s nucleus with anything synthetic was “never a good idea”.
Over thirty years, Malone knew about this situation yet no one lifted a finger to ban this technology, knowing it was a failure and toxic.
wow
Sundance is very impressive
not only does he toss out a theory
he brings all the goods to back it all up!
we now know the harm Obowel and the DemonRats have done to this country
God better save them because I don’t know what will be left
of them after the people catch on and get their hands on them!
Cough yak Lamp Post Ornaments Cough cough
I only made it to the 12th or so paragraph and it stuck me: The acolytes no longer need the media, they truly are obsolete. The media will be dispatched just as Yuri Besmenov described.
Back to reading.
0’Bama was just the salesman, a political Milli Vanilli if you will. The real question is, who was running him? Schwab? S0R0S? PRC? Qatar? Iran? All of the above? And why? That’s the question!
Well, SOMEBODY has been running our military for a long time!
That is the million dollar question we all want answered.
I agree, he is little different than Zalenski, picked to play a role; a dillatente, a liteweight.
Some get so focused on HIM, and aim their hatred at HIM; letting their emotions dictate their thoughts and actions like a frickin liberal.
What a waste of energy, and a distraction.
Dutchman, did you eat nails or razorblades?
America is a dying empire you cannot save it. The people don’t believe in the ideals or history of the country.
That is not my opinion. You are entitled to your opinion, but you are not entitled to speak for me.
Respectfully, this IS all important, in understanding what they do, and how they are doing it, but…
Using the “Color revolutions in the middle east as a “beta test” is only a small part of “the Big picture” which we can see now, much better in hindsight.
I think its clear the “war on oil” began MUCH earlier.
Perhaps the beta test was in Venezuela, which isn’t producing much oil, as its oil infrastructure is severely damaged thru negligence. And Venezuela WAS a “Beta test” for Dominion.
As for the color revolution, YES, they used twitter as a tool, to trigger violent “revolutions” in Tunisia, Egypt, Syria and Lybia.
It SEEMED to be a brush fire, which THREATENED TO DESTABILISE THE WHOLE MIDDLE EAST; and THATS the point of the excercise.
At the same time that they were sparking these “revolutions” in the least stable countries, they were desperately trying to “cut a deal” with IRAN, the major de-stabilising country in the ME, and shunning Israel, our ally.
Billions of $, on pallets of cash, which flowed directly to terrorist groups, like the houthis who are,…?fighting SAUDI ARABIA.
Point being, I think their goal was to destabilise the middle east, in order to stop oil production.
And, at the same time they sponsored the Euromaiden coup, putting Zalenski in power, arming/training the Azog nazis, etc.
I think the plan (put on hold when PDJT won)was to do what we are seeing now, in Ukraine, in 2018 had Hillary won.
Knock out Russia, Middle East and possibly Venezuela as oil producing regions, and of coarse keep US oil production low as Joe is doing.
Notice PDJT’s FIRST foreign visit? He arms Saudi Arabia to the teeth, institutesthe Abrams accords, getting the Sunni oil producing countries to work with Israel, against Iran, so COUNTERING what Obama/Hillary were trying to do.
Without the muh Russia narrative, PDJT WOULD have been able to work with Putin, in areas of mutual intetest, andasa counter to China.
Occams razor says the destabilising of the ME was about more than just “beta testing” twitter as a tool to manipulate public opinion, they created ISIS, a two country caliphate.
They WOULD have spread that to”the Kingdom” eventually.
A war, not “over oil” but “AGAINST oil”,..THATS what this is ‘all about’.
Touché!
This is a very good comment., DM. Might an epilogue be somewhat as follows?
“Hence, the opening another front on the war against oil in the form of the GND.
And that war is a step to achieving the Great Reset by the WEF”.
This reminds me of “We came, we saw, he died” followed by the cackle of a vicious witch.
Influencing, hiding reality, killing people.
Here’s such a story. Has anyone seen it in mainstream media? This is huge, its 90% of the crab population wiped out, dead!
One billion snow crab missing – Season Cancelled for Alaskan fleet https://thefishingdaily.com/featured-news/one-billion-snow-crab-missing-season-cancelled-for-alaskan-fleet/
This reeks bad when climate change is the reason given for no crabs.
We don’t know why would be a more valid answer !
I suspect it has to do with the weakening of the earth magnetic field and the migration of the north and south poles…..
the snow crabs probably got lost…. they went somewhere else that aligned with their inate magnetic field receptors…. it is now in a different place…
Declaring them wiped out dead with no data does not fly…
Watching Deadliest Catch, the last few seasons, the fishermen have been battling russian large scale operations – they don’t care about ecology, they just take as much as they can cram into their boats. I would say the lack of crab is due to illegal over fishing by foreigners. The chinese do the exact same thing all over the oceans.
Then you have all the damnable windmills generating sounds that confuse sea life…
Nothing to do with climate change.
“What are the chances that then President Obama did nothing to promote and ensure success for the Arab Spring because its true purpose was to serve as a beta-test for the use of the Twitter platform in future censorship and color revolution applications in the U.S.?”
What are the chances that Obama hiring Facebook co-founder Chris Hughes as his Information technology director in both the 2008 campaign and the in the Obama administration to ensure all sorts of success in manipulation of the electorate?
I foolishly thought Big Brother would be imposed on us. I never dreamed we would enthusiastically sign up for it.
“I foolishly thought Big Brother would be imposed on us. I never dreamed we would enthusiastically sign up for it.”
But even after the repeated exposure of the “social networking apps” for what they are, it’s almost guaranteed that tomorrows Presidential Thread will be a compilation of twitter links.
SMH
Just the other night, I watched an episode of NOVA on PBS that dealt with the use of computer algorithms to predict crime.
It was full of the usual liberal claptrap, but it discussed research by a guy who examined the interpersonal networks of victims to predict future victims.
Law enforcement took his research and used it to try to predict who would commit crime, rather than who would be the victim of it.
Now, think of the flash mobs, like the one that recently hit the WaWa in Philadelphia.
The perpetrators were most likely connected by a certain number of degrees to each other and rapidly organized via social media.
Imagine you’re an intelligence agency and you want to create a riot.
If you already have databases on interconnected networks of various radical groups, you can play them like a fiddle using social media.
You can get them to do your bidding without them even realizing it.
The key isn’t just social media, it’s knowing WHO to manipulate and WHO all their likeminded associates are.
This is the real value of all the data they’ve been collecting off of social media for years.
They know who is most likely to be a victim and who is most likely to victimize them.
They simply move them, using social media, like pieces on a chessboard.
Writing in his Substack [SEE HERE], Dr Robert Malone draws attention to the EDIFY research.
I hit the link to Dr. Malone’s Substack article and (somewhat to my surprise) found it very readable and understandable. I usually don’t try to get into the stack-of-needles on these kinds of things.
He lays out the overview of things that Sundance often refers to–not providing totally new information for Treehouse readers, but providing very large context and motivations, confirming the observations and conclusions that Sundance has been presenting for years.
I am very glad to be under the care and supervision of Almighty God, my Creator and my Redeemer.
Re: Dr. Malone: The worst thing those clowns did was to rile him up about WuFlu. He started his Substack with exposing WuFlu lies and just kept going to WEF, Deep State, etc. There are people you do. not. want to make mad. He’s one of them, and he proves that the axiom about people with advanced degrees being one trick ponies certainly isn’t always true.
I hope no one minds me reposting my comment from up post, because I still do not know who Malone is…
“Writing in his Substack [SEE HERE], Dr Robert Malone draws attention to the EDIFY research.”
Can anyone tell me just who Dr. Robert Malone is?
For months I have been asking this question. It seems as thought he is hiding in plain sight. I do not care that his original intent was for mRNA-producing spike proteins to be used as a delivery system for other reasons…his own technology seems to be killing people.
And what does he have to do with EDIFY research?”
Hope no one minds a repost of response to the reposter:
One place to start would be what Dr. Malone himself says about his background, the info can be checked:
https://rwmalonemd.substack.com/p/robert-malone-responds-to-trolls?utm_source=post-email-title&publication_id=583200&post_id=75427972&isFreemail=true&token=eyJ1c2VyX2lkIjo5Mzc0NjQwNCwicG9zdF9pZCI6NzU0Mjc5NzIsImlhdCI6MTY2NDM4OTkyOSwiZXhwIjoxNjY2OTgxOTI5LCJpc3MiOiJwdWItNTgzMjAwIiwic3ViIjoicG9zdC1yZWFjdGlvbiJ9.snBrVdc-BHqKX8NHrGayAgN44Nj193uAjmhnNoLN8RA&utm_medium=email
In these times, it is impossible to know for sure the truth about any figure or source. (This also applies to reader comments appended to articles like this one.)
The facts of the issues are the important focus, the nature of the messenger is not unimportant but should not be a primary focus. Ad hominem attacking the messenger is a common ploy of Machiavellians attempting to divert attention.
Dr. Malone grew up very near where I live. He attended local schools. One of my son’s girlfriends worked for him. I believe he is exactly who he says he is.
I can and will. I’ve watched every video he’s ever done. I’ll post a couple of informative links especially for WSB on the open thread since this is off topic here on this thread.
However, in re-reading this thread, I see you already know so I won’t post further information.
Here is a video on rumble platform , about wife of Robert Malone defending his contribution to advancing the technology for mRNA usage. It’s long, but perhaps someone can gain clues on this. Link: Ep 108.4: The Hateful Jill – PTSD and starvation caused by Wolff Rhodes Felgner
I remember watching “news” back in the day during the so-called Arab Spring and they kept showing the facebook/twitter logos when they talked about it.
I don’t do social media because I never saw the point, but it was kind of surreal seeing those logos all the time. I think one or the other of those went public around that time too – sick.
I was like, “dude – are you using human suffering to promote your platform???”
There is no easy way to fix this. It will require years and years of hard and dedicated labor.
In fact, it will take generations.
We ourselves won’t see the victory, we will only witness the beginning of the restoration.
America as we knew her has passed. It is possible that something as magnificent may rise in her place.
But it seems as likely that America reverts to the global mean. Hunger, poverty, & genocide.
America as we knew her has never passed.
So long as the Constitution, Bill of Rights and Declaration of Independence are in place, the bulwark for restoring proper balance remains in place. This is why I disagree with a bottom up only thought process as the grand strategy. As Paine outlines in Rights of Man, a Constitution supersedes and precedes all government. No one person or government can change a Constitution – that authority is invested in the people alone.
All well and good, but the constitution hasn’t constrained the process Sundance laid out.. everything that they did was UNconstitutional, yet they did it. We need effective Law Enforcement against the corrupt technocratic elite, or this thing descends into an abyss. I bet the abyss is more likely than an Obama perp walk.
Obama recently in a podcast mentioned how we all can say things that are taken the wrong way and we all can make mistakes.
That does not sound like Obama especially in a discussion about President Trump.
Is Obama trying to get ahead of something that is about to go public.
I think maybe the advice of Admen’s cat is needed.
And this is what you will find no where els THANK YOU SUNDANCE research unequaled anywhere in the crapisphere
R.D.
I felt a kinship with Malone thru his many posts plus shared memories of SBCC and Goleta and that historic horse ride post, I forget the name. This Substack post cements it.
Dude if you ever need a place to hide out let me know. I allow Admin here right to give out any and all of my info to you.
Ditto.
And they all conspired and stole the 2020 election by any means possible, and anyone who disagrees is an election denier, despite all the anomalies and irregularities.
While BHO and his minions may have weaponized gov’t against their political enemies, who GAVE them the tools to do it, hmmm? Oh, that would be the GOP! The GOP controlled both houses of Congress until 2006…
“Our elections have been usurped by the Intelligence Branch. Start with honest elections and we will see just how much Democrat AND Republican corruption is dependent on manipulated election results. Start at the state level. Start there…. everything else is downstream.”
Even election integrity could be assured, politicians are nearly all corrupted by the fourth branch tentacles in the transition to office, if not already.
This much illicit power recalls the famous line from the movie The Godfather, “…make ’em an offer they can’t refuse”.
So, what is the solution?
Must reading for every citizen.
The ukraine war is being fought in social media. Not much actual fighting being done
Thank you for your exhaustive research, Sundance. Doesn’t this yet again serve as an example of the Rockefeller template for ruining the country, conduct socialist experiments both abroad and in small manageable states such as leftist, corrupt Rhode Island, and then take them national?
Having grown up in the dark shadow of the Aldrich Mansion in Providence, RI, former home to Rockefeller son-in-law and FedReserve point man, Senator Nelson Aldrich, the Twitter experiment reeks of the same old Rockefelon Petri Dish, doesn’t it?
It’s not working anymore, Things are about to get interesting.
Astute observation.
Other factors come into play – just as trust.
Back during Obama’s reign Glenn Beck noted “they are building something” that he was unable to articulate but likened to a machine that would be set in motion once built. Sundance has done yeoman’s work documenting what that machine actually is….
Barry came to destroy. “I’m the “one” you’ve been waiting for” “the fundamental transformation of the USA”
The one “who’s (you)” has been waiting for and transformation into what exactly?
EVIL!
Sundance.
So the digital/big data aspects are of course interesting. One only has to look at grid loadings in certain obvious locations to get an understanding of the scale of operation.
Somewhere in the first decade of this century the shared vision of modern warfare among leadership and the huge colossus of national security political, civil service, contractor work forces departed from more traditional warfighting concepts (e.g.,defense industrial base, massed forces, superior logistics, boots on the ground ultimately taking/holding/controlling land masses, etc.) in a radical way. Based on seminal literature published in the 90s by folks such as Fred Stein and a few senior visionaries in the 6 worlds of the Services, information warfare and the flexibility of digital technologies gained traction as a “force multiplier”. Vision eventually evolved into transition. Weapon system design concepts, target selection, CONOPS, tactics, force structure – all changed. It wasn’t a facile process. Physics and combat dynamics ensured there were many surprises along the way. Concepts such as the OODA (observe, orient, decide, act) loop were seen in a new light when viewed from the perspective of digitized, networked nodes that connected sensors, decision-makers and shooters/weapons in near real time.
The semiconductor lay at the heart of all of it.
Naturally, the professional literature developed a concept structure for integrating these new capabilities into doctrine, Service organizational structure, CONOPS, acquisition priorities, recruiting, training, labs, R&D/T&E, exercises, etc. There was a concomitant shift in recruiting and hiring priorities across the board. There was, and remain, huge opportunities to fashion lengthy and lucrative careers in all dimensions of digital warfare.
Younger (a relative term obviously) members of the new “paradigm” across all layers (warfighter, political, civil service, contractor, etc.) have a very different view of modern warfare.
I can recall conversations in the early 2000s with younger folks, for example, that the Navy did not require 12-15 carrier battle groups (the numbers are driven by national security strategy and the operational life cycle of forces – training, operations, repairs) to much lower numbers. On what basis? The idea had taken hold that the dominant factor in warfare was the semiconductor. Take out/disable digital components of threat nodes and connecting networks (while protecting own force digital infrastructure) and the advantages accrue exponentially – decision speed/accuracy, shared awareness, etc. Simplifying, the belief developed that digital technology evolution, integration and operationalizing create advantages that warrant vast reductions in traditional kinetic force structure (to include warfighters). Hence, “we only need six battle groups” was often heard around the soda fountain and team building off-campus visits to local beer establishments.
A curious graft onto the messaging occurred around 2010-21012: digital/information warfare AND targeted assassination came to be centerpiece talking points for many in the new age workforce. The latter has been in place for a long time and currently/obviously in place around the world when it comes to folks with nuclear weapons expertise – and confirmed terrorists. Anecdotally (in my experience), the graft was most frequently expressed by folks from or supporting a specific community in the grand scheme of things. There are pro/con reasons for adopting this strategy. And obvious dangers/risks.
So why the boring history reprisal?
Soooooo. What to do about it?
Note the obvious: the digital world has vulnerabilities. Lots of them. This in fact expands into the whole system-of-systems (power, people, transport, hardware, software, concepts, models, resources). The vulnerabilities apply to all the players.
Probably the one major unstated amazing fact is that in 2015-16 Candidate Donald Trump and again 2016-2020 President Donald Trump was actually able to out maneuver the Uni-Party, 4th Branch of Government, democrats, international foes, et al using the very same weapons described in the article.
The success of Donald Trump also points to the 2-edged nature of the Social Media Weapon.
His election in 2016 likely stands out as one of the most amazing as Uni-Party, 4th Branch of Government and democrats had an 8-year head start in developing their capabilities.
A major caveat I will add though, is that Hillary Clinton was seen as an uncontrollable “outsider” in 2007-08, 2011-12 and again in 2015-16. She remains one today, which is the reason the democrats are not so supportive of her ever gaining the White House. The Clinton’s are useful but having their hands on the Presidential Power is not a desirable situation to the Puppet Masters and Democrats.